Catch of the Day: Amex Phish
Chef’s Special: World Cup Phish
Examples of clever phish that made it past my spam filters and into my inbox. Some are sent by clients or readers like you, and other reliable sources on the Internet.
You can send phishing samples to me at phish@wyzguys.com.
My intention is to provide a warning and show current examples of phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your inbox. If the pictures are too small or extend off the page, double clicking the image will display them in a photo viewer app.
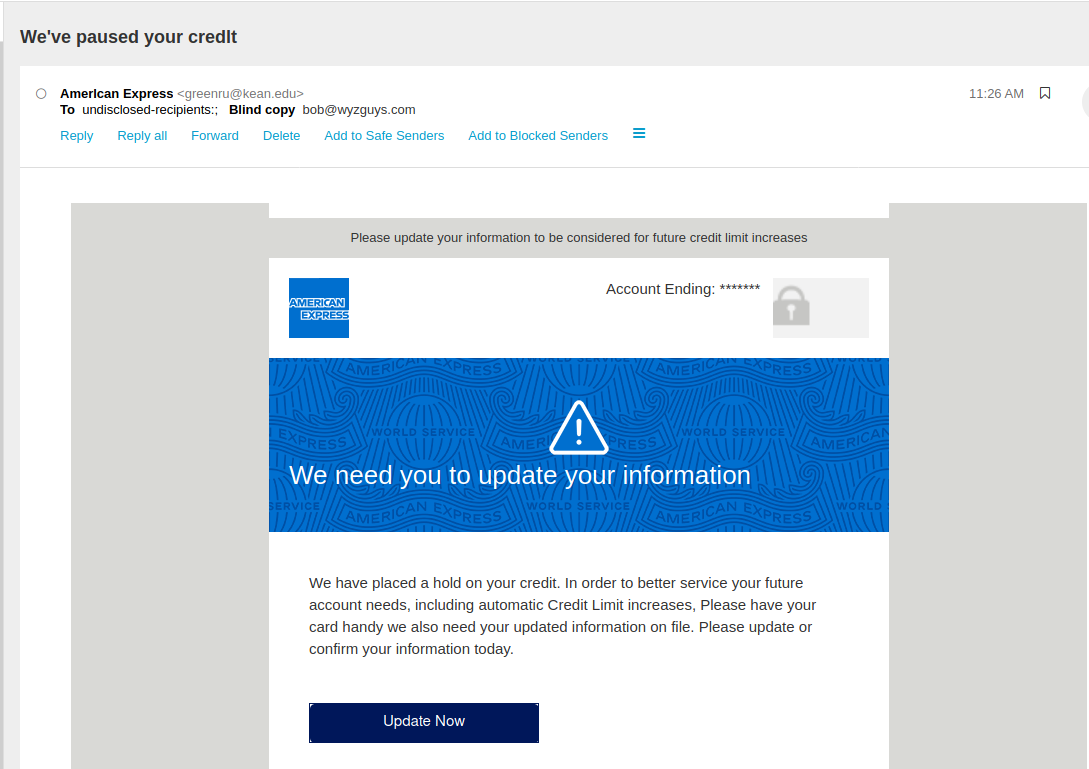
Amex Phish
There are a couple of different motivating claims being made in this email. The first is that my American Express account has been “paused”. The second is that I may qualify for an increase in my credit limit. So what is this? Good news, bad news?
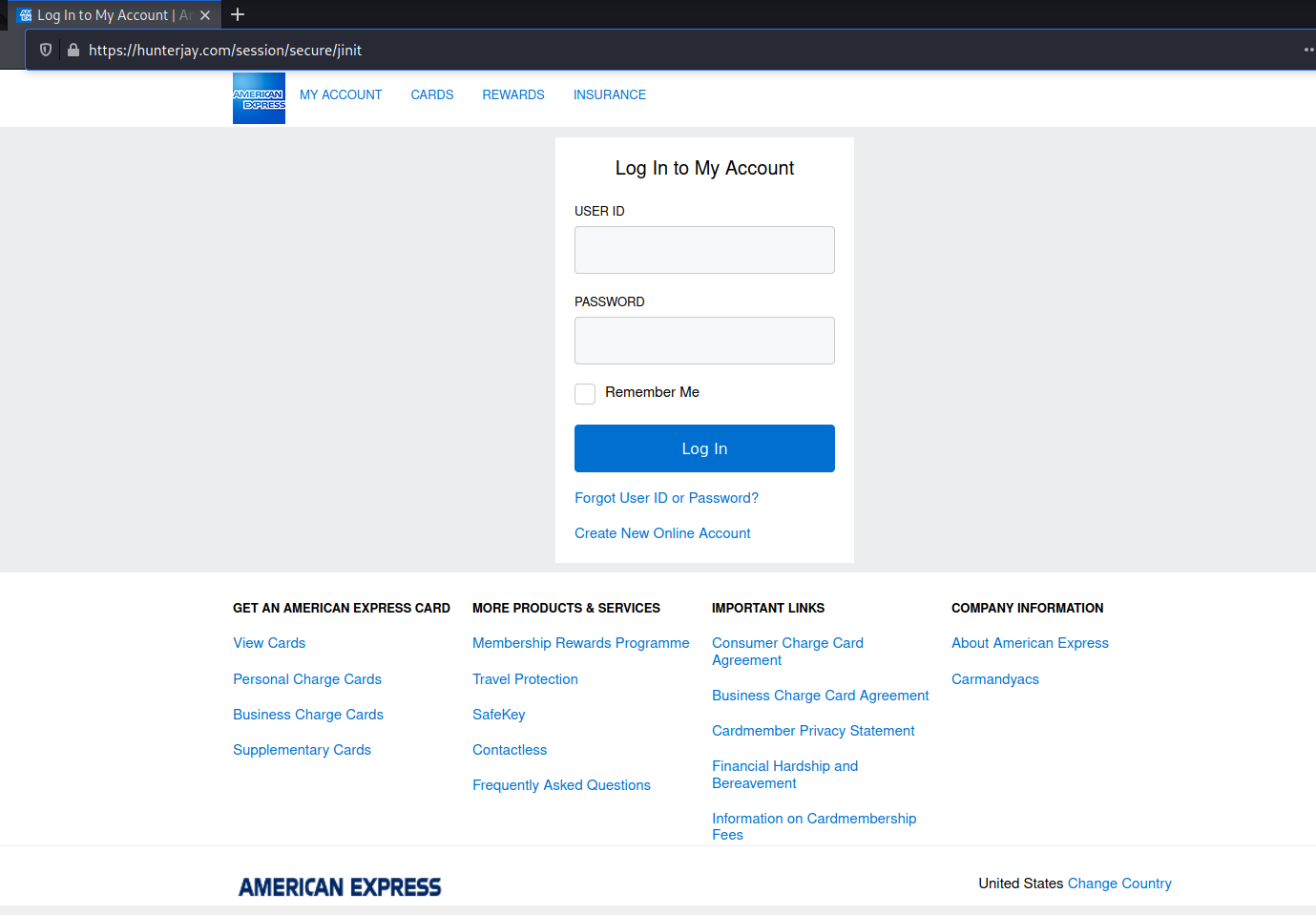
The Update Now button resolves to http://76996.stbarbaraparish.com/ then is redirected to https://hunterjay.com/session/secure/jinit. The stbarbaraparish domain is just parked at GoDaddy. Not sure if it has been hijacked, or has been registered by the attacker. The sending email domain greenru@kean.edu is not right for an email coming from Amex.
This appears to be another credential stealing phish. Since I do not carry an American Express card, this was easy for me to spot and avoid.
World Cup Phishing Attacks Doubled and Will Increase
Researchers at Trellix revealed that phishing email attacks targeting users in the Middle East doubled in October 2022 ahead of the World Cup in Qatar, as reported by The Record.
The end game of these attacks includes financial fraud, credential harvesting, data exfiltration, surveillance and damage to a country or organization’s reputation.
The rest of the world will soon follow.
The emails vary in subject matter. Here are a few examples provided by Trellix:
- Fake FIFA help desk emails warning of two-factor authentication deactivation
- Emails impersonating a team manager with a supposed payment confirmation phishing link
- Fake FIFA ticketing office emails warning of a payment issue
- Bogus legal notifications of a ban implemented by FIFA from registering new players
- Impersonated Players Status Department emails notifying users of delayed legal fees using WeTransfer’s template
- Spoofed emails from Snoonu, the official food delivery partner of the World Cup, offering fake free tickets to those who register
John Fokker, head of threat intelligence and principal engineer at Trellix, told The Record that they anticipate these attacks to continue through January 2023. “In this instance, we found the attention to the details incorporated into the malicious URLs and customized web pages to be notable, allowing cybercriminals to successfully impersonate league staff and team managers,” he explained.
Trellix said the top five malware families it found targeting Middle Eastern countries right now included Qakbot, Emotet, Formbook, Remcos and QuadAgent. These malware strains typically intend to steal confidential data or info, credentials or gain remote control of a device.
Jeremy Fuchs, a cybersecurity research analyst at Avanan, confirmed that they have also seen an influx of phishing emails related to the World Cup in a variety of different languages. “One common thread is related to betting on the World Cup, trying to entice end-users to wager. Instead, the email and resulting link steals credentials,” he said.
[CONTINUED] at KnowBe4 blog with links:
https://blog.knowbe4.com/world-cup-phishing-attacks-doubled-and-will-increase
Share
DEC





About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com