Catch of the Day: Human Resources Phish
Chef’s Special: E-Fax Phish
Examples of clever phish that made it past my spam filters and into my inbox. Some are sent by clients or readers like you, and other reliable sources on the Internet.
You can send phishing samples to me at phish@wyzguys.com.
My intention is to provide a warning and show current examples of phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your inbox. If the pictures are too small or extend off the page, double clicking the image will display them in a photo viewer app.
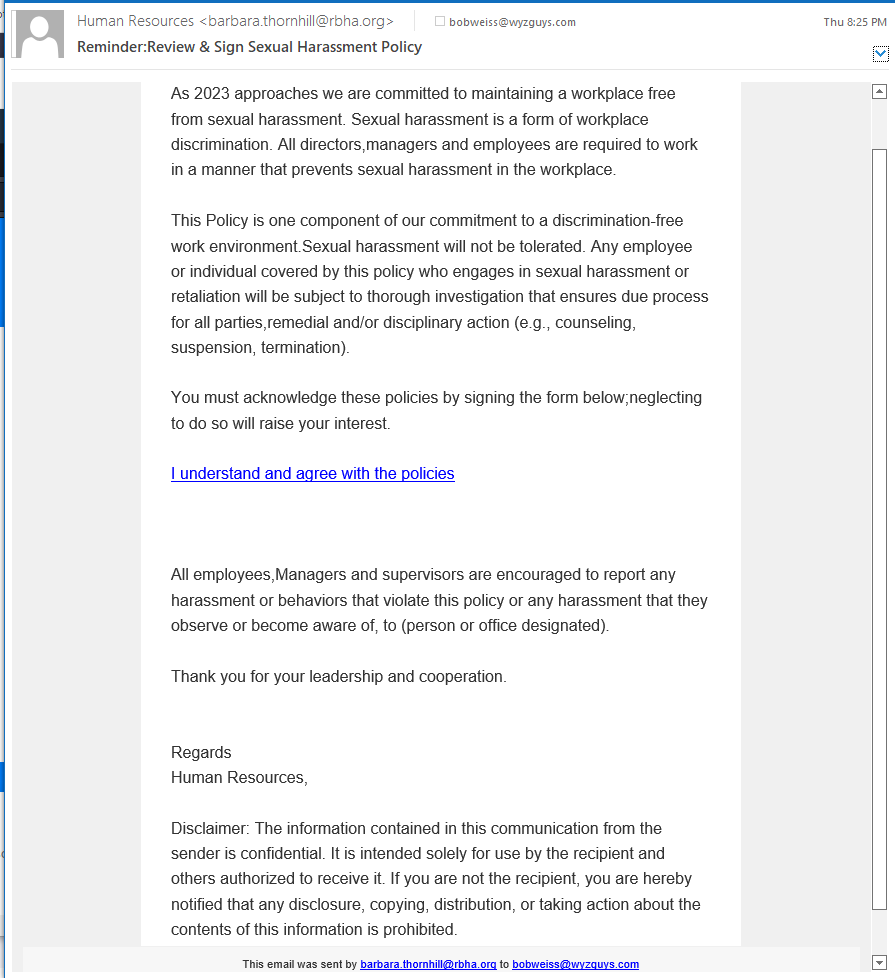
Human Resource Phish
These are two examples of emails sent from my “HR Department.” One deals with the sexual harassment policy. The other with face mask policy. My business, of course, is too small to have an HR Department, so I knew these were fake.
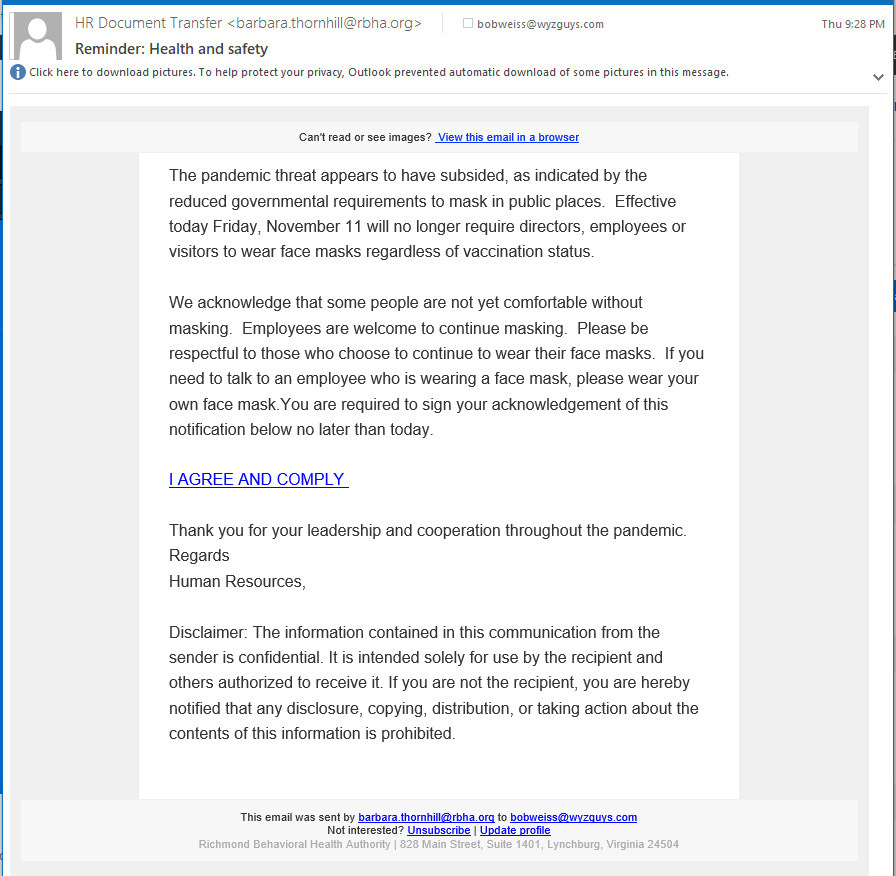
I checked the sender’s domain rbha.org it it just seems like it was chosen to spoof the sender of these messages. The link resolves to https://ljfkd-zgpm.maillist-manage.com/click.zc?m=1&mrd=1e42b379a38b3e4e&od=3zead19ed0427cf0ac735f16982b21162e552fa368dd77686732bd35a2e282bfe4&linkDgs=1e42b379a2f17e57&repDgs=1e42b379a3ae6771 which is then redirected to https://youengage.me/p/636b90c28cc3bc010004fa47. This returns a blank page. The domain https://youengage.me/ displays the following home page.
I am not exactly sure what the end game was for this, may just credential stealing again. The part of the exploit that used the public service youengage appears to have been taken down by the service provider. This is all speculation on my part.
Nevertheless, keep an eye out for bogus HR messages like this one, and never click on a link or open an attachment, or call that convenient toll-free number without verifying the validity of the source.
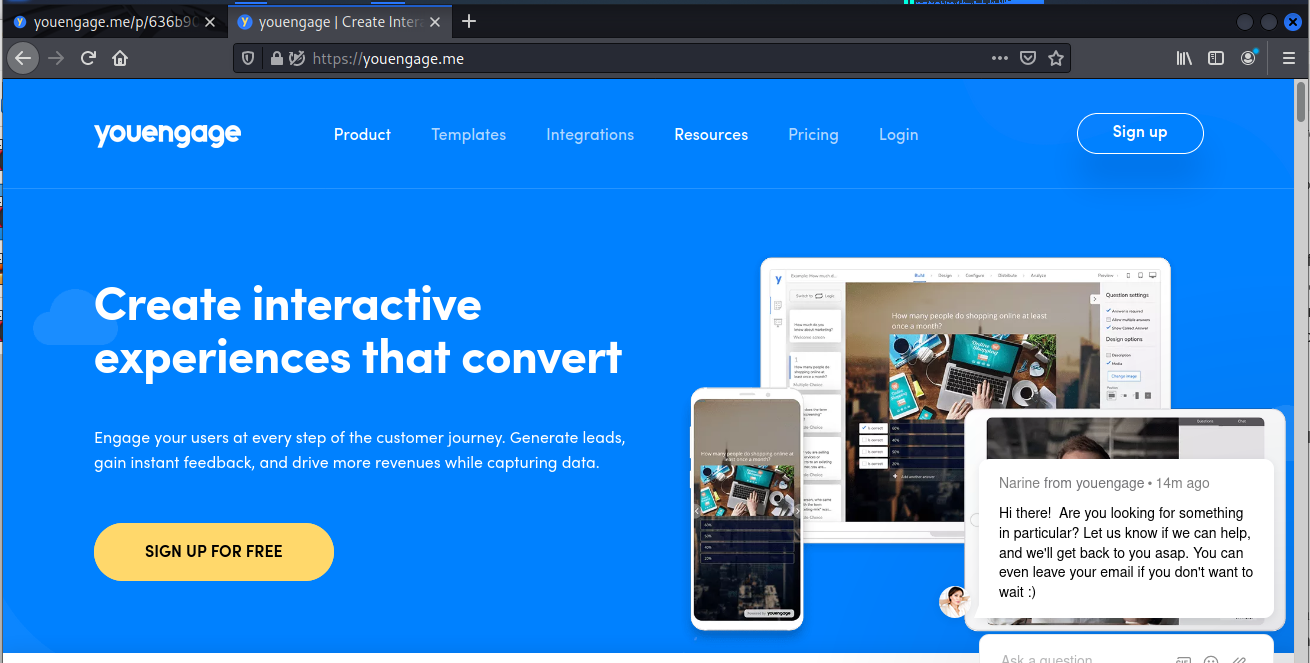
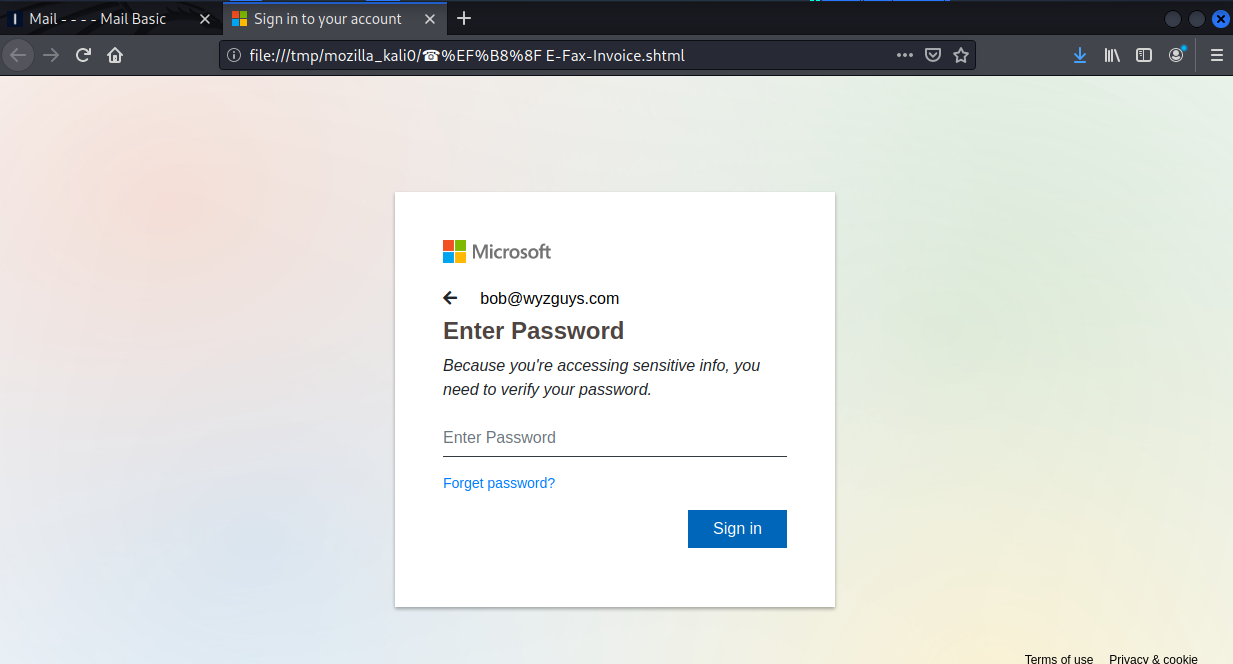
E-Fax Phish
Another phishing exploit with a locally hosted landing page. This is looking for your Microsoft account credentials.
Share
NOV





About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com