 Phishing Email Alerts
Phishing Email Alerts
Catch of the Day: Code of Conduct Phish
Chef’s Special: Invoice Phish
Examples of clever phish that made it past my spam filters and into my inbox. Some are send by clients or readers like you, and other reliable sources on the Internet.
You can send phishing samples to me at phish@wyzguys.com.
My intention is to provide a warning and show current examples of phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your inbox. If the pictures are too small or extend off the page, double clicking the image will display them in a photo viewer app.
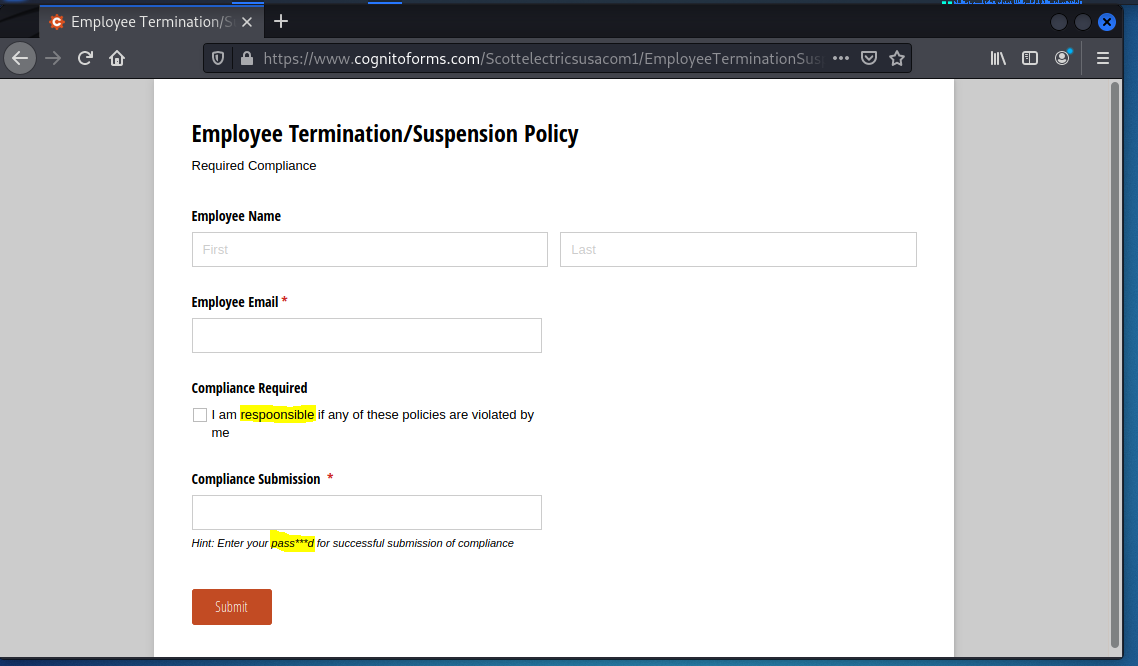
Code of Conduct Review
I received a similar email from “Human Resources” a couple weeks ago, and this one uses the same template. Again, the goal is to get employees to part with their email address and password.
The email uses some language which is not normal for business communications (I agree to be obediant..) The links work the same as they did two weeks ago.
In the following landing page we have a funny typo (respoonsible) and an entirely unnecessary obfuscation of the word password with pass***d.
So this looks like perhaps a different crew who is using the same “cybercrime as a service” as the previous crew did, with a few more noticeable errors.
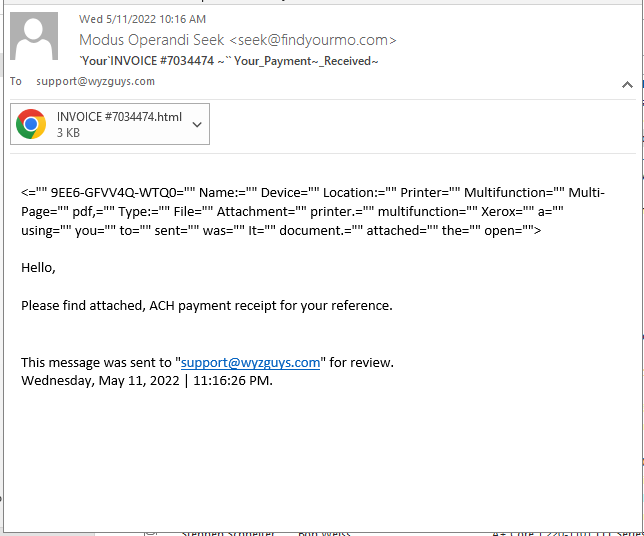
Invoice Phish
This one uses an HTML attachment to spawn the landing page. The goal of this exploit is also to capture the email address and email password. This kind of attack leads to email account hijacking, and business email compromise. Possibly leading to wire transfer fraud. Or maybe just a good way to get on your network.
Here’s the email. Not sure what to make of the code snippet that starts the email. It looks like a list of filed attributes in a database table. Is this some sort of SQL injection attack? If yo know what this is please comment at the bottom of the email. I’ll be sure to post it to this article.
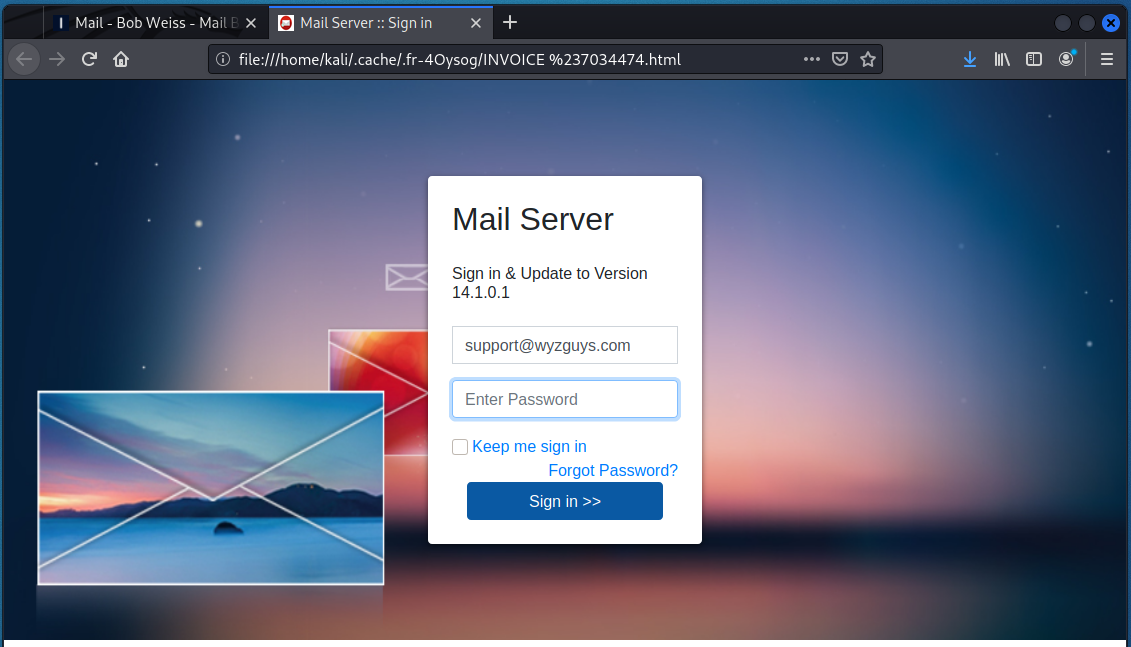
Here is the attachment
And finally the landing page. Nice work on the graphics, a plausible email login screen.
There is a New Type of Phishing Campaign Using Simple Email Templates
A phishing campaign is using short, terse emails to trick people into visiting a credential-harvesting site, according to Paul Ducklin at Naked Security. The email informs recipients that two incoming messages were returned to the sender and directs the user to visit a link in order to view the messages. Since the emails are so short, the scammers avoid risking typos or grammatical errors that could have tipped off the recipient.
The phishing link has the appearance of a direct URL to sophos[dot]com, but it’s actually a hyperlink that leads to a different site. The phishing site is also very simple, with just a login prompt and a title that says “User Control Panel.”
Ducklin notes that the scammers may have taken the simplicity too far at this point, as the phishing site doesn’t attempt to impersonate any brand. Ducklin offers the following advice to help people avoid falling for these attacks:
- “Don’t click ‘helpful’ links in emails or other messages. Learn in advance how to find error messages and other mail delivery information in your webmail service via the webmail interface itself, so you can simply login as usual and then access the needed pages directly. Do the same for the social networks and content delivery sites you use. If you already know the right URL to use, you never need to rely on any links in emails, whether those emails are real or fake.
- “Think before you click. The email above isn’t glaringly false, so you might be inclined to click the link, especially if you’re in a hurry (though see point 1 about learning how to avoid click-throughs in the first place). But if you do click through by mistake, take a few seconds to stop and double-check the site details, which would make it clear you were in the wrong place.
- Use a password manager if you can. Password managers prevent you from putting the right password into the wrong site, because they can’t suggest a password for a site they’ve never seen before.
- “Report suspicious emails to your own IT team. Even if you’re a small business, make sure all your staff know where to submit suspicious email samples (e.g. cybersec911@example[.]com). Crooks rarely send just one phishing email to one employee, and they rarely give up if their first attempt fails. The sooner someone raises the alarm, the sooner you can warn everyone else.”
New-school security awareness training teaches your employees to follow security best practices so they can avoid falling for phishing attacks.
Blog post with links:
https://blog.knowbe4.com/phishing-campaign-simple-email-templates
Now This Is a Tricky SMTP Relay Email Spoofing Technique
Researchers at Avanan have observed a surge in phishing emails that abuse a flaw in SMTP relay services to bypass email security filters.
“An SMTP relay service can be a valuable service for organizations that like to send out mass emails,” the researchers explain. “Essentially, businesses use SMTP relay services–of which there are many– to send marketing messages to a vast database of users without being blocklisted.
“Utilizing trusted SMTP relay services ensures messages get delivered. Many organizations offer this service. Gmail does as well, with the ability to route outgoing non-Gmail messages through Google.”
Attackers can use this feature in Gmail to impersonate legitimate Gmail tenants, making their phishing emails more likely to go undetected by security technologies.
“However, these relay services have a flaw,” Avanan says. “Within Gmail, any Gmail tenant can use it to spoof any other Gmail tenant. That means that a hacker can use the service to easily spoof legitimate brands and send out phishing and malware campaigns.
“When the security service sees avanan[.]com coming into the inbox, and it’s a real IP address from Gmail’s IP, it starts to look more legitimate…. Phishingemail@phishing[.]com wouldn’t want to send their email from that domain.
“They would want the legitimacy of a major brand. So, using this service, they instead send their email from, say, paypal[.]com (assuming paypal uses Gmail). Email scanners see that it’s coming from Gmail’s trusted relay service–and for good measure, often a trusted brand–and it sails right through to the inbox.”
The researchers warn that attackers have increasingly adopted this technique over the past month. “Starting in April 2022, Avanan researchers have seen a massive uptick of these SMTP Relay Service Exploit attacks in the wild, as threat actors use this service to spoof any other Gmail tenant and begin sending out phishing emails that look legitimate,” Avanan says.
Blog post with links:
https://blog.knowbe4.com/smtp-relay-email-spoofing-technique
Man Convicted for $23 Million Phishing Scam Against the U.S. DoD
A man in California has been convicted for stealing $23.5 million from the U.S. Department of Defense in a phishing attack. The Justice Department explained in a press release that the man, Sercan Oyuntur, hijacked payments meant for a jet fuel supplier.
“A corporation that had a contract with the DoD to supply jet fuel to troops operating in southeast Asia employed an individual in New Jersey, who was responsible for communicating with the federal government on behalf of the corporation through a government computer system,” the Justice Department says.
“Through a complex phishing scheme, Oyuntur and criminal conspirators in Germany, Turkey, and New Jersey targeted the corporation and the individual so that the conspirators could steal money that DoD intended to pay to the corporation for providing jet fuel.”
Oyuntur worked with others to set up a complex phishing operation to steal the funds.
CONTINUED:
https://blog.knowbe4.com/man-convicted-for-dod-phishing-scam
MAY






About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com