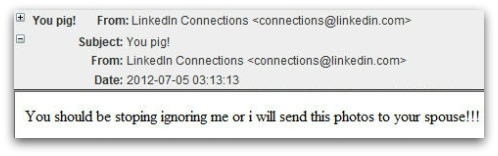
When I teach my computer security classes, I am often asked “why do they do it?” My answer is always “It’s the money.” Most of the computer and network malware exploits are making money for the perpetrators one way or another, and as more traditional criminal organizations move into cybercrime, we see more traditional criminal elements. In this case, spam email messages are sent out with a subject line of “You pig!” and a threatening note that the attached photograph will be sent to the spouse if a ransom is not forthcoming. While this looks like a straight extortion racket, the digital photograph, when clicked on, is in fact a malicious download of the Trojan horse variety. The guilty will want to click to see just how incriminating the picture is, and the innocent will click because they are curious what the picture may show. Either way you now have a nasty infection.
This Trojan allows the operators of this scam to send you advertising displays that they get paid to push to you. It may also be recording your keystrokes and stealing other data, and permits the attacker to remotely control your system.
ShareJUL




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com