 Let’s say I just hijacked your email account. What can I do with it?
Let’s say I just hijacked your email account. What can I do with it?
First thing, a hijacker would not announce his or her presence in your account. Staying undetected is important so you do not change your password. Depending on what the attacker is doing with your email account, there is a significant probability that you would not know your account was compromised for several days, weeks, or even years!
In order to take control of your email account, an attacker would need your user ID and password. Typically, this is achieved through the use of a phishing email designed to look like it came from your email service provider. See the examples and landing page below. Or the attacker may purchase a list of email user names an passwords on the Dark Web.
And an example of a Gmail account phishing email.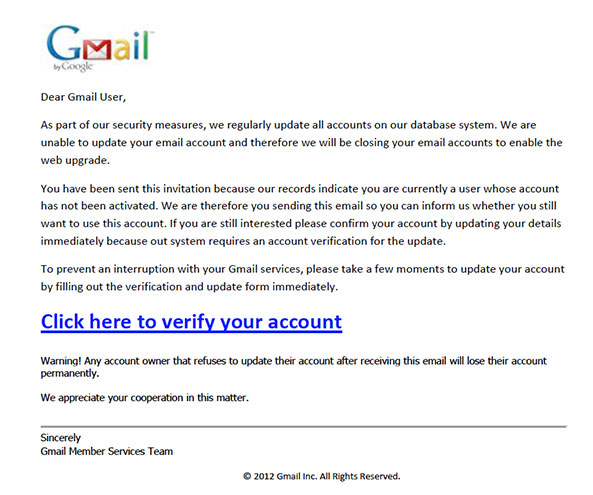
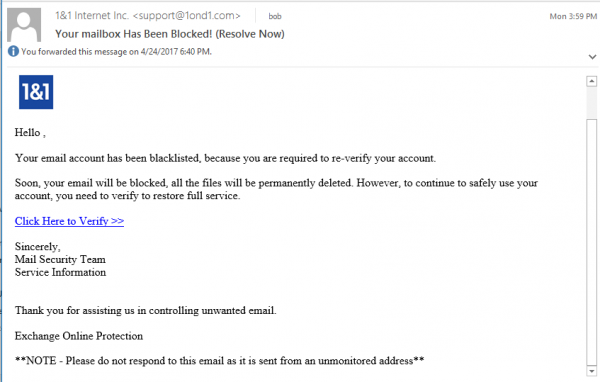
Here is an example of an email account hijack phishing email that I received and the landing page. The sender email address has been spoofed using a near misspelling – support@1ond1.com instead of support@1and1.com.
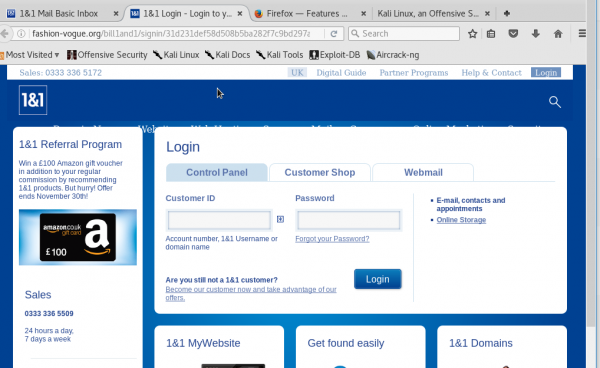
 Notice the web address in the address bar – fashion-vogue.org not 1and1.com. This is an important clue that this page is a fake.
Notice the web address in the address bar – fashion-vogue.org not 1and1.com. This is an important clue that this page is a fake.
According to the 2016 Internet Crime Report that was recently released by the Internet Crime Complaint Center (IC3), email account compromise is the number 1 cyber crime by dollar losses to victims. The amount lost was over $360 million. So just what kind of malicious uses could a comprised email account provide? We will have the answers to that question on Wednesday.
ShareJUL




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com