 Is your company moving operations to the cloud? What about the cybersecurity aspects of protecting your data assets in the cloud? Are you relying on your partner/vendor to take care of securing your information? In light of the Paige Thompson indictment, it is apparent that relying too heavily on your vendor’s expertise and staff can open you up to an insider based attack.
Is your company moving operations to the cloud? What about the cybersecurity aspects of protecting your data assets in the cloud? Are you relying on your partner/vendor to take care of securing your information? In light of the Paige Thompson indictment, it is apparent that relying too heavily on your vendor’s expertise and staff can open you up to an insider based attack.
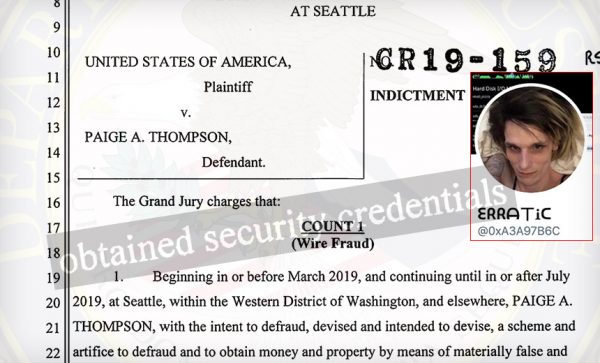
And who is Paige Thompson? She goes by the Twitter and hacker handle “erratic.” If you remember the press about the Capital One breach from a couple weeks ago, Thompson is the transgender ex- AWS employee who allegedly was behind the theft of data from Capital One. Last week she was indicted by a federal grand jury for stealing the data of over 30 companies that was stored on Amazon Web Services (AWS), between March and July 2019.
Based on the indictment, Paige chose targets in the education, telecommunications, financial, and government sectors. The indictment says she used her Amazon credentials to gain access to the cloud services of her targets. She stole information and data from over 30 victim companies, by using automated scanning software, and looking for security misconfigurations. She often used a VPN to hide her identity and her source IP address when she was engaged in reconnaissance or actual attacks.
She is also charged with using her access to engaging in Bitcoin mining, commonly called “crypto-jacking.” This is a very processor intensive operation that would increase costs for her victims.
As a result of these breaches, Amazon has tightened up their security practices, and is proactively scanning customers to discover any other security misconfigurations. If you set up services in the Amazon cloud, or frankly any other cloud (Rackspace, Microsoft Azure, IBM, Google Cloud, Oracle Cloud) and thought you might be getting security practices like this, you might want to take a closer look.
Well-known and well-regarded technology service providers such as Amazon, Microsoft, IBM, and Google are able to hire the best an brightest talents. This would apply to their cybersecurity operations teams as well. Consequently your expectations may be that they ought to do a better job at securing your assets than you and your team can do on your own.
This may be true. Nevertheless, the responsibility to ensure that you are properly secured in your cloud operations still remains with you, the data owner and creator. Make sure you understand exactly what does and doesn’t come with your Cloud Services Agreement.
And don’t overlook the danger of an insider threat inside your own operations. Sure, you have known these people for a long time, and everyone at your company is “like family.” You mean like that goofy family that shows up for Thanksgiving and Christmas? Do you get my drift? Someone in your organization may not share your “family values” and my be exploiting your hopeful naivete. Make no assumptions, trust nothing and no one, and lock down everything.
ShareSEP




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com