I have said it before, and I will repeat it now: passwords by themselves are no longer a useful form of security. The only option that makes passwords secure is two-factor authentication. Today we embark on a two week investigation into passwords, why they are so easy to break, how your password might be compromised, and how to create a password system that is less vulnerable to exploitation.
Why are passwords so easy to crack? Some of the answers we have discussed before, but bear repeating.
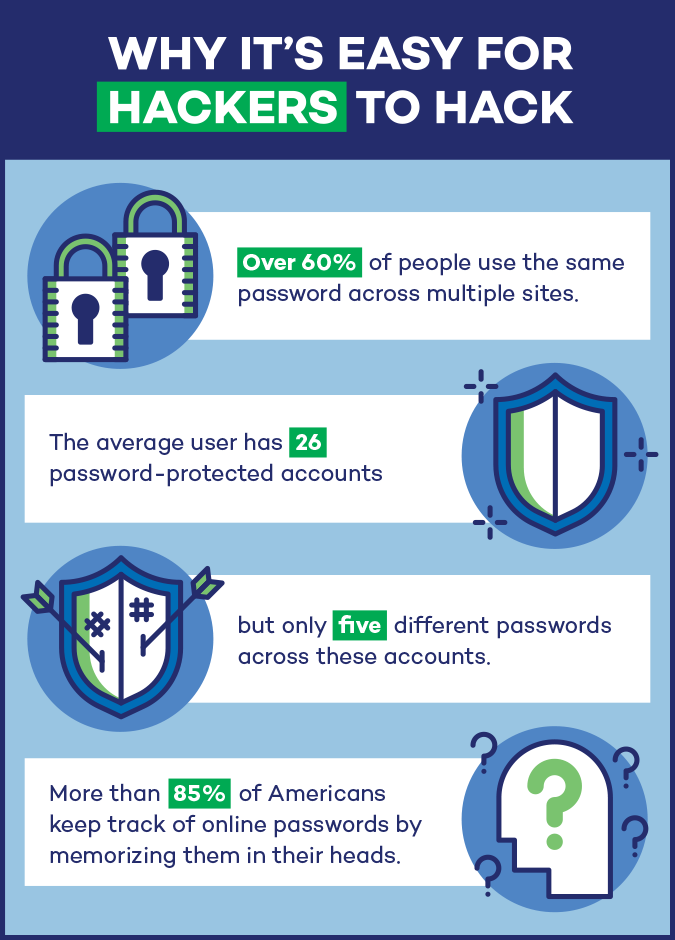
- Reusing passwords – 60% of people use the same password on more than one site. The average user has 26 password protected site, but is using only 5 passwords to protect them.
- Human predictability – We tend to use passwords and phrases that are memorable to us, such as family names, street address, birth date, anniversaries, and pet names. Combining these ideas to create “difficult” passwords does not keep a skilled hacker from guessing your password. In business environments that enforce regular password changes, it is common to use month and year combinations such as May2018! as a password
- Memorization – 85% of people keep track of passwords through memorization. Another 7% write them down in lists or spiral notebooks. Only 8% use a password manager to keep track of passwords.
- Weak by design – We continue to see the same weak passwords in the each year in the top 25 worst passwords list. Qwerty and 12345678 are not strong passwords but continue to show up at the top of the list. Short passwords can be cracked quickly using automated tools, by 8 characters continues to be the recommended minimum length of most password policies.
Tomorrow we will look at how long it takes for an attacker to compromise your password.
A special thanks to Panda Security for inspiring the content of this series and providing us with the infographics used in this series.
ShareJUN




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com