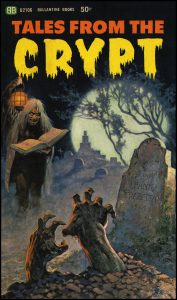
 Tales from the Crypt was the name of a series of E.C. Comics in the 1950s. They were the inspiration for a TV show of the same name that ran for 7 seasons and 93 episodes on HBO from 1989 to 1996. In 2018, the new tales of the crypt involve weird sounding terms such as crypto-currency, crypto-mining, and crypto-jacking. Today we will open and explore this crypt.
Tales from the Crypt was the name of a series of E.C. Comics in the 1950s. They were the inspiration for a TV show of the same name that ran for 7 seasons and 93 episodes on HBO from 1989 to 1996. In 2018, the new tales of the crypt involve weird sounding terms such as crypto-currency, crypto-mining, and crypto-jacking. Today we will open and explore this crypt.
The “crypto” part of these terms refers to “encryption.” The root word “crypt” means “a hidden place.” The process of data encryption turns plain text or clear text or regular readable words, into highly obfuscated or hidden “cipher text” through the use of very large prime numbers and some impressive mathematical computations known as “algorithms.”
Crypto-currency and blockchain. In 2008, Satoshi Nakamoto invented an encrypted distributed public ledger system called “blockchain” to keep track of transactions in the electronic payment currency called Bitcoin. We have all heard of Bitcoin, and other crypto-currencies such as Monero and Etherium. Many of us know that Bitcoin is somehow magically created out if thin air by computers, using a process known as “bitcoin mining or crypto-mining.” More on that later. These electronically derived currencies have become an accepted medium for exchange of value on the Internet. The value of crypto-currencies are not tied to the value of a physical substance such as gold, and is not regulated by any banks or governments. It’s value floats in the open market, and recently there has been a staggering rise in value, from when Satoshi Nakamoto mined the first block of bitcoins ever (the genesis block), which had a reward of 50 bitcoins. In 2010 a bitcoin was worth about $18. In 2017 the value of bitcoin went from about $2500 to over $19,000. Lately that value has dropped to just under $10,000. As of the end of June 2018 the value of a Bitcoin is 6,087.87.
Crypto-mining. Because the ledger is public, anyone can view and verify the contents of the ledger and the accuracy of the transactions. Transactions in crypto-currency are reviewed and encrypted by the public members who maintain the blockchain. These volunteers use software to encrypt the most recent transactions and add the to the blockchain. There is in reality a competition between these volunteers to be the first to create a new verified block and add it to the blockchain ledger. The winner of this competition is awarded a certain amount in bitcoin for the effort. This is called crypto-mining. To be able to create a new block, you need a computer that is computationally very powerful, and these sorts of machines are expensive to buy or rent. Becoming a bit-coin miner is not a guarantee of instant wealth. The current reward per block is only a small fraction of a bitcoin. It is becoming economically challenging to break even or profit in crypto-mining activities.
Crypto-jacking. This brings us to the latest popular cyber-exploit, crypto-jacking. One way to reduce the cost of the equipment needed for crypto-mining is to steal the machine resources of other people. I have written about some of the machine hijacking methods previously. These include “borrowing” a machine for 10 seconds when logging into a coffee shop WiFi network, server hijacking, web server hijacking, browser based exploits, smartphone exploits, and “borrowing” a supercomputer used to calculate nuclear missile trajectories, and others. The problems that will manifest themselves if your systems are crypto-jacked include:
- Loss of system performance. Your computer or other device is running extremely slowly, yet appears to be fully engaged in some sort of activity.
- Increases in power consumption. All this processing takes processor cycles, and this will increase your electric bill.
- System crashes and physical damage. Affected systems will run at full capacity, processors will overheat, fans will be running full blast, network traffic increases. Devices become hot, batteries become hot enough to fail or burst, and system crashes and physical damage are possible and common.
- Operational and financial losses. Affected systems become unavailable for their regular operations, resulting in a denial-of-service condition, and financial losses due to reductions in system availability.
In our next post we will continue exploring this topic, discussing what systems are at risk, and how to protect yourself and your business from crypto-jacking.
More information:
- Wikipedia – Tales from the Crypt
- Wikipedia – Blockchain
- ST18-002: Defending Against Illicit Cryptocurrency Mining Activity
- Wyzguys – Crypto-mining on the rise
JUL




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com