A recent article in Naked Security caught my eye the other day about a new web site vulnerability called HTTPoxy. This stands for HTTP requests and poisoned proxy settings. Most web site use a technology called Common Gateway Interface (CGI) to run applications such as site search, collect information submitted on web forms, display comments, run a forum, or to display database queries such as pricing in a usable form on a web page.
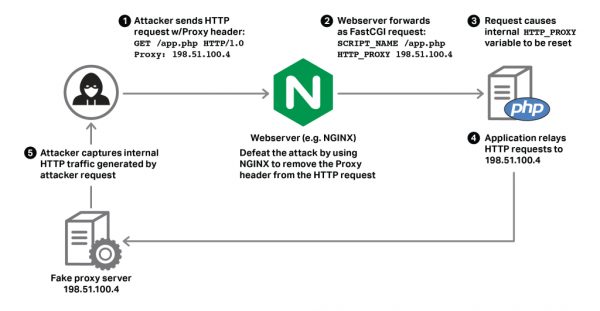 The technical details of this vulnerability are explained in the Naked Security article, so I won’t repeat them here. According to the HTTPoxy website, the solution is to block HTTP proxy requests before they run in the web application, and they have instructions on how to accomplish that on their site.
The technical details of this vulnerability are explained in the Naked Security article, so I won’t repeat them here. According to the HTTPoxy website, the solution is to block HTTP proxy requests before they run in the web application, and they have instructions on how to accomplish that on their site.
The best and easiest solution is to run your website under HTTPS. This requires the installation of an SSL security certificate to your website. We just did this for a website we manage, and it was easily accomplished through the host, GoDaddy, for about $60 per year. Or if you are frugal and technically savvy, LetsEncrypt or FreeSSL may be the solution you prefer. This exploit will not work on an HTTPS website.
One of my current recommendations is to encrypt everything. Any website owner ought to convert their site to HTTPS. The added benefit to your web site visitors is that their session is encrypted and protected from prying eyes and man-in-the-middle exploits, so this is basically just good operational security and great customer service.
ShareAUG




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com