“Give a man a Phish and he eats for a day, teach a man to Phish and he eats for a lifetime.”
When you get an email that is spoofed as the example below has been, this is called a Phishing email. The object is to “hook” the recipient into doing something that will be harmful to their wealth. I got one just this morning that for me was a new look, and included the threat of legal action. If you see something like this – DON’T CLICK THE LINK. Here’s why:
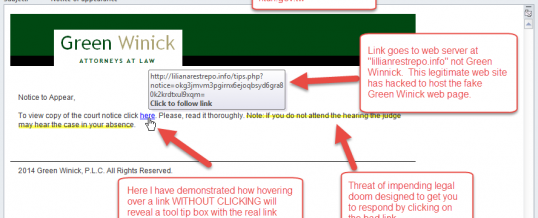
From the top, first notice that the return email address has nothing to do with the alleged sender Green Winick Attorneys at Law. The email address is spoofed from a Taiwanese government email domain “lichao@ntuh.gov.tw” The TW at the end is the country code domain for Taiwan. How do I know that? I looked it up in Google. You can too.
Lower right – the message in the email is brief (a legal brief? LOL sorry for the lame pun) but the threat is obvious – if you don’t click “here” a judge (Ooooo – scary) will rule on my “case” in absentia. Then the jury will award a multi-million dollar Judgment for the plaintiff, and you will be RUINED!! Resist the urge to click on the link. The only way you can be ruined is by clicking the link.
Next, (lower left) hovering over the link in an email will usually reveal a “tool tip” box that displays the actual destination of the offered link. Another method to use, if this one doesn’t work for you, is to RIGHT CLICK on the link, select Properties from the context menu, and find the destination URL. In any event, DO NOT LEFT CLICK ON THE LINK.
The link actually goes to the web site “lillianarestrepo.info” which was undoubtedly a legitimate website, possibly a WordPress site, that has been hacked and was hosting the fake Green Winick landing page for this exploit. My attempts to go to this site using a sacrificial Ubuntu Linux box found that the site had been taken down, so this particular scam seems to have been undone by the someone working this particular exploit, possibly some branch of our government such as the FBI. Anyway, here’s a fine example of your tax dollars at work. Or perhaps an observant web host noticed the spike in traffic on this web site and took it down on their own. WordPress sites have been a favorite target of cyber-criminals lately, due to the DIY nature of the platform, and the probably easy to guess, hack, or phish administrative passwords. If you have a WordPress site, you might want to change and improve (lengthen) your password.
Since I could not visit the site I was unable to capture a screen shot of the the landing page, but I bet it would have been a great copy of the Green Winick web site, with all the corporate colors, trade dress, and typography. There would have been some sort of blather about the fictitious case, and a web form where they would have harvested whatever information they wanted from you: name, address, phone, perhaps a credit card number, bank routing number, or social security number. If it had turned out that you were the plaintiff and not the defendant, the bank routing number request would be so that they could send you your “settlement.”
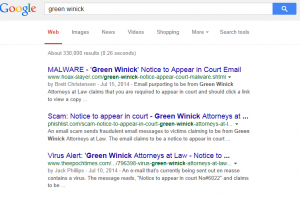
Again Bob’s Rule #1 is: Never click on a link in an email without knowing for sure who the email is from, and where the link is going to take you. In this case, Googling to the Green Winick web site, would have told me all I need to know. See below:
ShareAUG




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com