Bad actors are using compromised WordPress.com accounts and the popular Jetpack plugin to add a malicious plug-in of their own that turns compromised websites into a vehicle for perpetrating a fake tech support scam. Attackers are using stolen user names and passwords from other breaches and trying these credentials on WordPress.com to find accounts. They are even searching whois records for website domain names registered with the same email account as the stolen user name.
For this attack to work certain conditions need to exist.
- You need to have a WordPress.com account.
- You need to have JetPack installed on your website.
- JetPack must be configured to allow management from a WordPress.com account.
- The WordPress.com account credentials must be compromised.
- The WordPress.com account does not have two-factor authentication activated.
Here is what’s happening:
- An attacker signs into a WordPress.com account using a stolen user name and password.
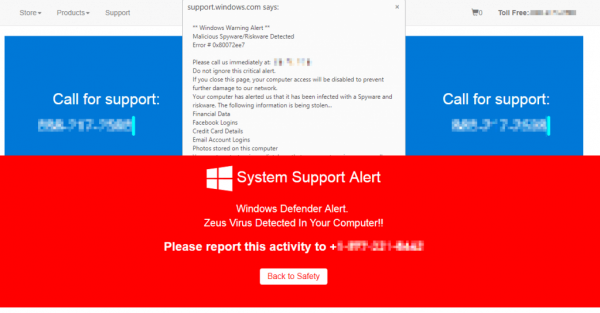
- If the WordPress.com account is configured to use JetPack for administration, the attacker will install a malicious plug-in named “pluginsamonsters.”
- The plugin gives the attacker unfettered administrative access of the targeted website, allowing them to install the tech support pop-up exploit code, or potentially other exploit code.
- The “pluginsamonsters” plug-in is visible on the WordPress.com dashboard, but not the affected site’s plug-ins dashboard.
To prevent this attack from working:
- Change your WordPress.com password and make sure to use a password longer than 12 characters.
- Enable two-factor authentication on your WordPress.com account.
Here is another example of how one of my favorite security options, two-factor authentication, can prevent unauthorized access of an import web resource, this time your web site. To remove this malicious plugin and any associated malicious code that may have already been installed, use the free version of Wordfence security.
More information:
ShareJUL




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com