 When I am doing a cybersecurity presentation, someone is bound to ask about the Dark Web. What is it, exactly, and how does someone get there? The how part we discussed on Friday. Linux Tails is a great tool for accessing and browsing the Dark Web, should you be so inclined. Before we delve into the Dark Web, let’s talk about the different parts of the web.
When I am doing a cybersecurity presentation, someone is bound to ask about the Dark Web. What is it, exactly, and how does someone get there? The how part we discussed on Friday. Linux Tails is a great tool for accessing and browsing the Dark Web, should you be so inclined. Before we delve into the Dark Web, let’s talk about the different parts of the web.
- The Clear Web – This is the Internet that we all know and use every day. The normal web, full of websites to communicate, entertain, shop, and join. The clear web is Google searchable for the most part. Google, Facebook, YouTube, Twitter, Amazon, your website, and my website are all part of the clear web.
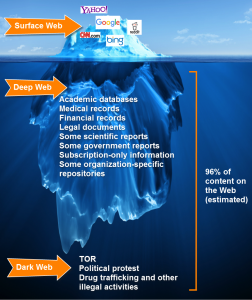 The Deep Web – This is the part of the Internet is is not publicly accessible. Usually there is a user ID and password that is required to access resources on the deep web. These resources include things such as subscription-based searchable databases such as LexisNexis, or Dunn and Bradstreet. Company-owned and provided SharePoint sites are considered deep web. These locations generally have not been searched and indexed by Google or the other search engines since search spiders cannot get past the logon screen. But if you have the right credentials and permissions, you can access deep web sites using a standard computer and any web browser such as Chrome, Edge, Firefox, or Safari.
The Deep Web – This is the part of the Internet is is not publicly accessible. Usually there is a user ID and password that is required to access resources on the deep web. These resources include things such as subscription-based searchable databases such as LexisNexis, or Dunn and Bradstreet. Company-owned and provided SharePoint sites are considered deep web. These locations generally have not been searched and indexed by Google or the other search engines since search spiders cannot get past the logon screen. But if you have the right credentials and permissions, you can access deep web sites using a standard computer and any web browser such as Chrome, Edge, Firefox, or Safari.- The Dark Web – The Dark Web is composed of websites where encryption is always used, and where the user community has set up shop to avoid be part of the public Internet. This includes legitimate mainstream organizations such as the US State Department, the Defense Department (the US Navy created TOR), the Electronic Frontier Foundation, and the United Nations. It is also used by many spy agencies, journalists and freedom fighters who work in countries where their life or liberty are at risk. You can find extremist groups of all stripes including Al-Qaeda, Daesh (ISIL), Neo-Nazi, White Supremacist, and others. Of course the Dark Web has attracted a large number of criminal organizations because its inherently private and secure nature makes it a great place to sell stolen software, exploit kits, botnets, lists of stolen passwords, stolen credit cards, prescription and illegal drugs, weapons and munitions, pornography of all kinds, and engage in human trafficking.
The best way to get on the Dark Web is using a tool like TOR, and Linux Tails. Many web addresses on the Dark web end with a .onion TLD. You can get a list of TOR hidden websites from Wikipedia. Just be aware that you are definitely going into no-man’s land, and the other people you find on the Dark Web may not be the someone you would like to meet on the street. If you are looking to poke around in the Dark Web, it makes sense to use a sacrificial system, one that you don’t mind replacing or restoring. Of course Tails, since it lives on a USB drive, fits that requirement. If you decide to walk on the Dark side, just be careful, and make sure you reveal nothing about your real identity.
More information – Dark Web Search Engines. Remember, you need to be using TOR to navigate to a .onion web site.
- Torch – http://xmh57jrzrnw6insl.onion/
- The Hidden Wiki – http://zqktlwi4fecvo6ri.onion/wiki/index.php/Main_Page
- Ahmia – http://Ahmia.fi
- Grams – http://grams7enufi7jmdl.onion/helix/light
- AlphaBay – http://pwoah7foa6au2pul.onion/
- StartPage – https://startpage.com
- Candle – http://gjobqjj7wyczbqie.onion/
- notEvil – https://hss3uro2hsxfogfq.onion.to/
- DuckDuckGo – http://duckduckgo.com
- Memex – http://www.darpa.mil/program/memex
OCT




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com