 A quick Saturday digest of cybersecurity news articles from other sources.
A quick Saturday digest of cybersecurity news articles from other sources.
Keeping PowerShell: Measures to Use and Embrace
Original release date: June 22, 2022
Cybersecurity authorities from the United States, New Zealand, and the United Kingdom have released a joint Cybersecurity Information Sheet (CIS) on PowerShell. The CIS provides recommendations for proper configuration and monitoring of PowerShell, as opposed to removing or disabling it entirely due to its use by malicious actors after gaining access into victim networks. These recommendations will help defenders detect and prevent abuse by malicious cyber actors, while enabling legitimate use by administrators and defenders.
CISA urges organizations to review Keeping PowerShell: Measures to Use and Embrace and take actions to strengthen their defenses against malicious cyber activity.
[Bob’s comment: I have been recommending disabling or removing PowerShell when not required as a part of general device hardening.]
Capital One identity theft hacker finally gets convicted
It took three years, but the Capital One cracker was convicted in the end. Don’t get caught out in a data breach of your own!
Facebook Phishing Scam Steals Millions of Credentials
Researchers at PIXM have uncovered a major Facebook Messenger phishing scam that’s “potentially impacted hundreds of millions of Facebook users.” More than eight million people have visited just one of these phishing pages so far this year.
“While viewing the Yearly Views page, we see 2.7 million users visited one of their pages in 2021, and around 8.5 million so far in 2022,” the researchers write. “This represents tremendous growth in the campaign from 2021 to 2022.”
The threat actors used compromised Facebook accounts to spread the phishing pages through Facebook Messenger. More at Blog post with links: https://blog.knowbe4.com/facebook-phishing-scam-steals-millions-of-credentials
A Closer Look at HR Phishing: Does Niceness Have a Downside?
Threat actors are targeting HR employees who are looking to hire new people, according to Lisa Vaas at Contrast Security. As part of their job, HR employees frequently interact with people outside of the organization and are more likely to open external files. Attackers frequently take advantage of this by hiding malware within phony resumé files.
Vaas cites Dmitri Alperovitch, chairman of the Silverado Policy Accelerator, as saying in a talk at RSAC that North Korean threat actors are particularly fond of this technique. Blog post with links: https://blog.knowbe4.com/a-closer-look-at-hr-scams-does-niceness-have-a-downside
New Android banking malware disguises as crypto app to spread
A new banking Trojan dubbed “Malibot” pretends to be a cryptomining application to spread between Android phones. While only active now in Spain and Italy, it could begin targeting Americans.
CISA Releases Security Advisories Related to OT:ICEFALL (Insecure by Design) Report
Original release date: June 22, 2022
CISA is aware that Forescout researchers have released OT:ICEFALL, a report on 56 vulnerabilities caused by insecure-by-design practices in operational technology across multiple vendors. The vulnerabilities are divided into four main categories: insecure engineering protocols, weak cryptography or broken authentication schemes, insecure firmware updates and remote code execution via native functionality. More…
Malicious Cyber Actors Continue to Exploit Log4Shell in VMware Horizon Systems
Original release date: June 23, 2022
CISA and the United States Coast Guard Cyber Command (CGCYBER) have released a joint Cybersecurity Advisory (CSA) to warn network defenders that cyber threat actors, including state-sponsored advanced persistent threat (APT) actors, have continued to exploit CVE-2021-44228 (Log4Shell) in VMware Horizon® and Unified Access Gateway (UAG) servers to obtain initial access to organizations that did not apply available patches. The CSA provides information—including tactics, techniques, and procedures and indicators of compromise—derived from two related incident response engagements and malware analysis of samples discovered on the victims’ networks.
CISA and CGCYBER encourage users and administrators to update all affected VMware Horizon and UAG systems to the latest versions. If updates or workarounds were not promptly applied following VMware’s release of updates for Log4Shell, treat all affected VMware systems as compromised. See joint CSA Malicious Cyber Actors Continue to Exploit Log4Shell in VMware Horizon Systems for more information and additional recommendations.
On the Subversion of NIST by the NSA
Nadiya Kostyuk and Susan Landau wrote an interesting paper: “Dueling Over DUAL_EC_DRBG: The Consequences of Corrupting a Cryptographic Standardization Process“: More…
Citrix Releases Security Updates for Hypervisor
Original release date: June 24, 2022
Citrix has released security updates to address vulnerabilities that could affect Hypervisor. An attacker could exploit one of these vulnerabilities to take control of an affected system.
CISA encourages users and administrators to review Citrix Security Update CTX460064 and apply the necessary updates.
Black Basta may be an all-star ransomware gang made up of former Conti and REvil members
The group has targeted 50 businesses from English speaking countries since April 2022.
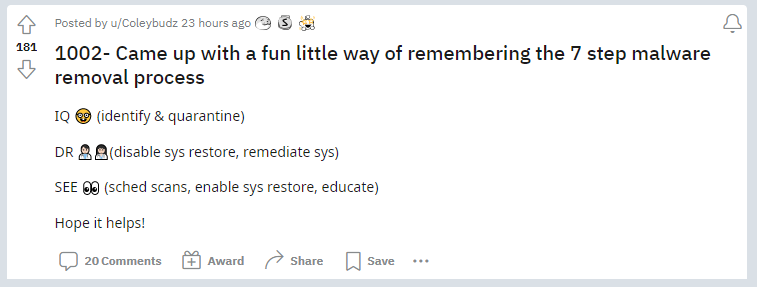
CompTIA 7 Step Malware Removal Process
When Security Locks You Out of Everything
Thought experiment story of someone who lost everything in a house fire, and now can’t log into anything:
JUL




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com