 A quick Saturday digest of cybersecurity news articles from other sources.
A quick Saturday digest of cybersecurity news articles from other sources.
Yes, There Really Is A Windows 11
Microsoft announces Windows 11, with a new design, Start menu, and more. A new version of Windows is officially on the way.
Urgent Alert – WD My Book Live users wake up to find their data deleted
Storage-device maker advises customers to unplug My Book Lives from the Internet ASAP.
Western Digital, maker of the popular My Disk external hard drives, is recommending customers unplug My Book Live storage devices from the Internet until further notice while company engineers investigate unexplained compromises that have completely wiped data from devices around the world.
The mass incidents of disk wiping came to light in this thread on Western Digital’s support forum. So far, there are no reports of deleted data later being restored.
The First Mobile Phone Call Was Made 75 Years Ago
The first mobile phone service, for 80-pound telephones installed in cars, was demonstrated on June 17, 1946, 75 years ago. The evolution of the cell phone illustrates what it takes for technologies to go from breakthrough to big time
This week, a lot from Bruce Schneier
Is 85% of US Critical Infrastructure in Private Hands?
Most US critical infrastructure is run by private corporations. This has major security implications, because it’s putting a random power company in — say — Ohio — up against the Russian cybercommand, which isn’t a fair fight.
When this problem is discussed, people regularly quote the statistic that 85% of US critical infrastructure is in private hands. It’s a handy number, and matches our intuition. Still, I have never been able to find a factual basis, or anyone who knows where the number comes from. Paul Rosenzweig investigates, and reaches the same conclusion.
So we don’t know the percentage, but I think we can safely say that it’s a lot.
Adding a Russian Keyboard to Protect against Ransomware
A lot of Russian malware — the malware that targeted the Colonial Pipeline, for example — won’t install on computers with a Cyrillic keyboard installed. Brian Krebs wonders if this could be a useful defense. (Bob’s Note – I did this myself, it is quick and easy.)
Try This One Weird Trick Russian Hackers Hate
In a Twitter discussion last week on ransomware attacks, KrebsOnSecurity noted that virtually all ransomware strains have a built-in failsafe designed to cover the backsides of the malware purveyors: They simply will not install on a Microsoft Windows computer that already has one of many types of virtual keyboards installed — such as Russian or Ukrainian. So many readers had questions in response to the tweet that I thought it was worth a blog post exploring this one weird cyber defense trick. More...
Apple Censorship and Surveillance in China
Good investigative reporting on how Apple is participating in and assisting with Chinese censorship and surveillance.
Bizarro Banking Trojan
Bizarro is a new banking trojan that is stealing financial information and crypto wallets.
Research report.
Double-Encrypting Ransomware
This seems to be a new tactic:
Emsisoft has identified two distinct tactics. In the first, hackers encrypt data with ransomware A and then re-encrypt that data with ransomware B. The other path involves what Emsisoft calls a “side-by-side encryption” attack, in which attacks encrypt some of an organization’s systems with ransomware A and others with ransomware B. In that case, data is only encrypted once, but a victim would need both decryption keys to unlock everything. The researchers also note that in this side-by-side scenario, attackers take steps to make the two distinct strains of ransomware look as similar as possible, so it’s more difficult for incident responders to sort out what’s going on.
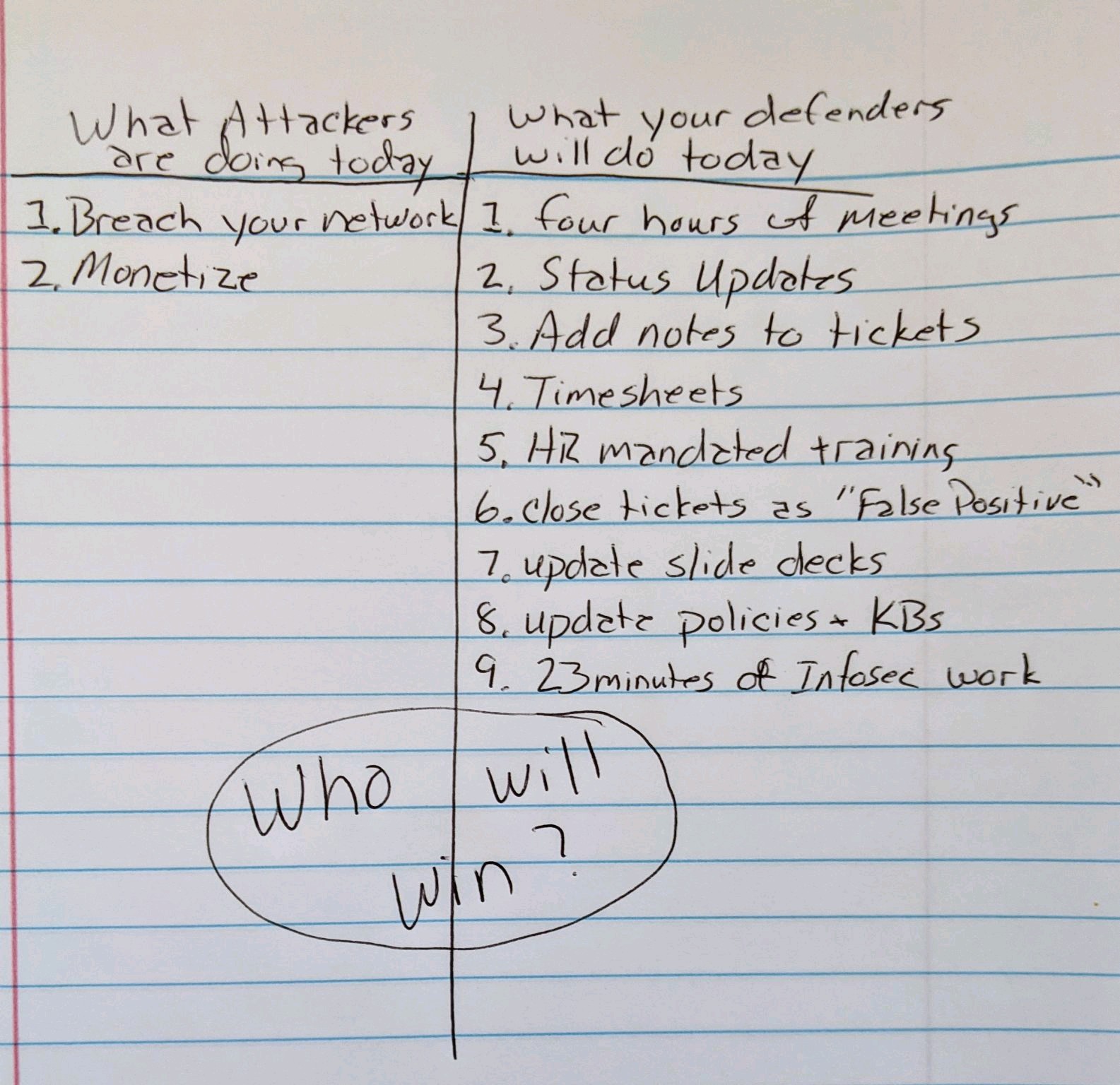
Why Your Infosec Team Can’t Win
The many ways a ransomware attack can hurt your organization
Loss of revenue, brand and reputation damage, employee layoffs and business closures were some of the effects of a ransomware attack, according to Cybereason.
Why Kubernetes is our modern-day COBOL, says a tech expert
Commentary: Today’s infrastructure becomes tomorrow’s legacy, but there are ways to build that avoid pitfalls.
Clop ransomware suspects busted in Ukraine, money and motors seized
Victims in South Korea and the USA, suspects busted in Ukraine.
IcedID: From Word to Lateral Movement in 1 Hour
In May 2021, we observed a threat actor conducting an intrusion utilizing the IcedID payloads for initial access. They later performed a number of techniques from host discovery to lateral movement, using RDP and SMB to access the file servers within an enterprise domain.
IcedID (known as BokBot) first observed in 2017, continues to be an active and capable threat against both individuals and organizations. The IcedID malware utilizes a modular malware framework and incorporates a number of anti-forensic and defense evasion capabilities. This malware has like others before it moved into the initial access broker market being used as an entry point for follow on activity like Cobalt Strike, and has lead to multiple domain wide ransomware deployments such as Revil and Conti. More..
Cobalt Strike – When Good Tools Go Bad
This article describes how the popular Cobalt Strike penetration testing tool is being abused by cybercriminals. Cobalt Strike is a popular tool with cybersecurity professionals. Unfortunately, it’s also utilized by threat actors. New research shows how Cobalt Strike is being weaponized in campaigns deploying malware ranging from the Trickbot banking Trojan to Bazar.
Share
JUN




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com