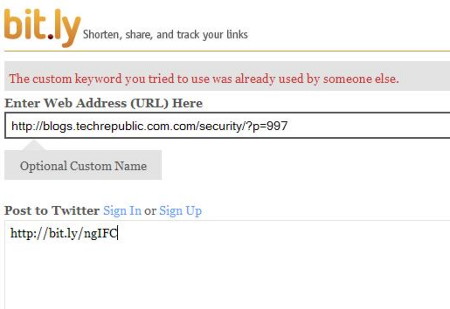
I never liked the shortened URLs provided by services such as TinyURL, Bit.Ly, Google, and Microsoft. Part of my security mantra in every cybersecurity awareness training session I have given since I started training in 2002 is: never, ever click on a link in an email unless you know where it is going. Most of the time you can see the actual destination URL of a hyperlink by simply hovering the cursor over the link until the tool tip box opens. URL shortening services make this difficult.
 Fortunately, there is a site called GetLinkInfo.com that will reveal the destination of shortened URLs safely. Bookmark this site for the next time you need it.
Fortunately, there is a site called GetLinkInfo.com that will reveal the destination of shortened URLs safely. Bookmark this site for the next time you need it.
Additional issues have been reported recently by Bruce Schneier in his blog, and Lisa Vaas in Naked Security. It turns out the short keyspace of these shortened URLs make them easy to brute force, especially if you have a botnet laying around. What this means is if you posted something semi-private online and send the permitted viewers a shortened URL link, someone running this type of brute force attack will eventually find your “secret” information. (Wait – you can’t post something online and keep it private!) This exploit can reveal shortened links to Google Docs and MS OneDrive files or pictures that may not have any permissions set, and are therefore vulnerable to casual view by the attackers.
So both giving and receiving shortened URLs have their respective risks. Bear this in mind when you opt for the convenience of the shortened URL.
More information:
ShareMAY




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com