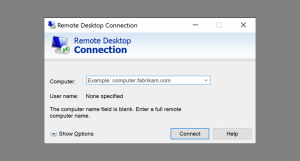
 Phishing for login credentials may still be the way most network breaches happen, but insecure use of remote desktop protocol is another favorite vulnerability used by attackers to enter a network.. Sophos Naked Security reported their findings on the use of RDP or the Remote Desktop Protocol as a launch vector for accessing and compromising entire networks. Their findings are sobering.
Phishing for login credentials may still be the way most network breaches happen, but insecure use of remote desktop protocol is another favorite vulnerability used by attackers to enter a network.. Sophos Naked Security reported their findings on the use of RDP or the Remote Desktop Protocol as a launch vector for accessing and compromising entire networks. Their findings are sobering.
Finding computers, servers, and other systems that are open to RDP connections is trivial. Search service Shodan.io lists over 3 million devices using the search parameters “remote desktop” and over 5 million devices running with port 3389, the default RDP port, open to the Internet. Due to the ease of finding targets using tools such as Shodan, and the persistence of easy to guess or crack passwords, finding an insecure RDP server is a bridgehead into a larger network comprised of hundreds or thousands of potential victims. Passwords are recovered using automated tool such as NLBrute, or lists of credentials can be purchased on the dark web.
RDP has been a top distribution vector for criminal groups running ransomware attacks using SAMSAM, DHARMA, MATRIX, BITPAYMER, and RYUK exploit kits.
Tactics used by attackers include slowly increasing the login rate of their automated tools to discover when the connection is throttled by rate-limiting settings used by the network defenders. Then they run their password cracking tools at a rate just below the threshold. Keeping the rate lower also with allow the attack to appear part of the normal background chatter of the network, and prevent SIEMs and other detection devices for registering the attack as a suspicious anomaly.
The top user names used in these attacks are Administrator, Admin, Test, User1, Support, SSM-User. Oddly enough, the names David and Jessica also appeared frequently in the test that Sophos ran, and their inclusion in the top user names was attributed to the higher frequency these actual names appear in the general population.
If you are a network administrator, cybersecurity blue-team member, or SOC analyst, the Sophos report needs to go to the top of your reading list. An internal and external vulnerability scan, and maybe a firewall rules audit looking for instances of remote desktop open to the Internet may be in order. Or take a look at your network using Shodan. Targeted ransomware attacks are on the rise again, with much larger extortion payment demands. You need to ensure that your company or organization is not the next victim.
More information:
Share
JUL




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com