 Today we start a three article series on developing good password strategy for you small business. As it happens, there is a great resource available courtesy of Her Majesty’s Government. The British signals intelligence department, GCHQ, has published a guide to password policy entitled Password Guidance: Simplifying Your Approach. This 12 page guide offers password advise in seven sections. They are:
Today we start a three article series on developing good password strategy for you small business. As it happens, there is a great resource available courtesy of Her Majesty’s Government. The British signals intelligence department, GCHQ, has published a guide to password policy entitled Password Guidance: Simplifying Your Approach. This 12 page guide offers password advise in seven sections. They are:
- Change all default passwords on devices that you deploy on your network.
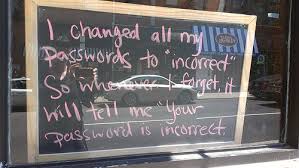
- Help your user group cope with password overload by creating simple policies that are easy to follow.
- Understand the limitations of user created passwords.
- Understand the limitations of machine generated passwords
- Take extra care with administrator and remote user accounts.
- Use account lockout policies and proactive authentication log monitoring.
- Do not store passwords anywhere in plain text.
In the introduction they cover the ways that passwords are discovered by cyber-criminals, including:
- social engineering, phishing, coercion
- manual password guessing, perhaps using personal information such as name, date of birth, or pet names
- intercepting a password as it is transmitted over a network
- ‘shoulder surfing’, observing someone typing in their password at their desk
- installing a keylogger to intercept passwords when they are entered into a device
- searching an enterprise’s IT infrastructure for electronically stored password information
- brute-force attacks; the automated guessing of large numbers of passwords until the correct one is found
- finding passwords which have been stored insecurely, such as handwritten on paper and hidden close to a device
- compromising databases containing large numbers of user passwords, then using this information to attack other systems where users have re-used these passwords
Surprisingly, they put to rest some of the hoary old chestnuts of corporate authentication, like the requirement to change passwords periodically. If you are looking at creating a password policy for your organization that has a better chance of really working, you will want to take a look at this document.
ShareSEP




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com