 Today we wrap up our review of the new password document from the GCHQ, Password Guidance: Simplifying Your Approach.
Today we wrap up our review of the new password document from the GCHQ, Password Guidance: Simplifying Your Approach.
Administrator and Remote User Accounts
These two classes of user accounts represent the gold standard for attackers, the administrator account for a system, server, or network, and a remote access account.
Administrator accounts grant the user total authority to a device or network. Administrator accounts should not be used for standard user activities. Daily log-ins should happen on another type of account with more restrictive permissions. For instance, Windows computers user accounts can be set up as a “Standard User” and this restricts the user’s ability to install programs (or malware) and make significant changes to the system. In a Windows Domain there are many other options to choose from. Administrator should be the last choice.
Remote users are another matter. This may include something as simple as the remote control service Log Me In, to VPNs and email server connection for home based employees, vendors, or travelers. If an attacker is able to compromise a remote user account, they can then use privilege escalation to achieve administrative rights, and own your network.
In both cases, creation and deployment of administrator accounts and remote user accounts should be closely managed, limited to by necessity and not convenience, and taken down, disabled, or changed when an employee or other user is no longer using the credential.
Account Lockout and Monitoring
We touch on this briefly already, but it bears repeating. Your systems should be using account lock-out features that are probably built into the operating system. That way if an attacker fails to guess the password in a certain number of tries, they are locked out of the system for a period of time. Some products can permanently block an attacker by their IP address.
And someone in your IT group should be monitoring the logs for log-in failures, or other unusual log-in activity.
Encryption
Never store passwords as plain text. This includes the “handy” documents some users and even IT departments create for their own internal use. If an attacker gets on your system, this will be a gift for them.
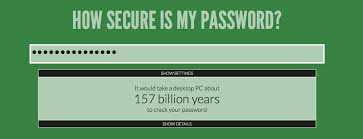
If you are storing passwords on a server, and especially if these are customer passwords on a web service you maintain, be certain the the passwords are properly encrypted. Establishing useful password length and complexity requirements are an important defense against attacks where the entire encrypted database of passwords is exfiltrated and later subjected to automated brute force password cracking techniques. Short password under 10 characters can be solved for in times under a week, which is a trivial amount of time for a cyber-criminal.
So that wraps up our series. I strongly recommend that you take a look at the original document. There will be at least two or three actionable items for your organization to implement, and while passwords may not be perfect, we are stuck with them for now. Using a strong password strategy will help keep your business out of the hands of intruders.
Share
OCT




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com