 If you bought a security camera, webcam, baby monitor, smart doorbell, digital video recorder or other IoT device manufactured in China, there is bad news. Security flaws have been discovered that can easily allow an attacker remote access, remote control, and password discovery on affected systems. These devices can also be hijacked to use in a variety exploits including eavesdropping through on-board microphones, image capture of what the camera can see, and inclusion in a botnet used for DDoS, crypto-mining, and other attacks.
If you bought a security camera, webcam, baby monitor, smart doorbell, digital video recorder or other IoT device manufactured in China, there is bad news. Security flaws have been discovered that can easily allow an attacker remote access, remote control, and password discovery on affected systems. These devices can also be hijacked to use in a variety exploits including eavesdropping through on-board microphones, image capture of what the camera can see, and inclusion in a botnet used for DDoS, crypto-mining, and other attacks.
There are problems in the iLnkP2P software that was developed by Chinese software developer Shenzhen Yunni Technology. According to security researcher Paul Marrapese, there are more than 2 million devices affected by this vulnerability.
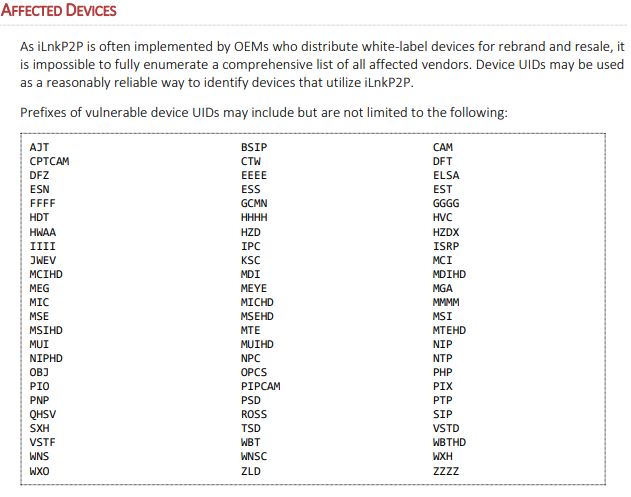
Unfortunately, this software is used by many equipment manufacturers (OEMs), so listing the affected brands is a difficult task, especially when considering that a single manufacturer may be white-labeling products for several different brands.
One way to determine if you device is affected is to look for the Unique Identifier number or UID on the device. This is how the software connects to the cloud controller and your online user account. Below is a list of most of the UID initial prefixes.
Many of these devices are also still using the manufacturer’s default administrative ID and default password. Default passwords for devices like this are available on the manufacturer’s website, as well as dozens of password aggregation sites. When you buy one of these devices, consumers are strongly urged to change these passwords. And store you passwords in a safe place such as a password manager program.
If you are joining the IoT revolution and creating a smart home full of smart devices, then actually be smart about it and take a few moments to properly secure all these smart appliances.
More information:
ShareMAY




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com