Microsoft Office VBA macro viruses were a pretty powerful exploit back in the 1990’s, but security changes by Microsoft and other security software vendors had pretty much made them moot by 2000. Surprisingly enough malware writes are giving them a new life by tricking users into disabling macro protection. Here is how it works:
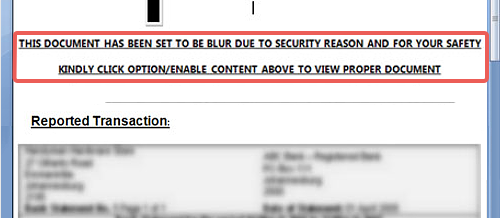
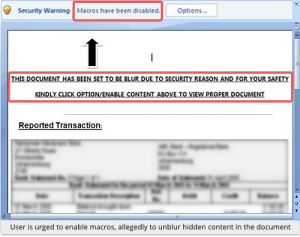
VBA or Visual Basic for Applications is a software language created by Microsoft to allow advanced users to write bits of code called “macros.” Macros allow a document created in Word, Excel or other Office applications to contain little bits of software code that turn a DOCUMENT into a light weight APPLICATION, which can allow the document to do some pretty cool and amazing things for the creator of the document. Or it allows a document, like a Word or Excel file, to carry a hidden payload of malware. Sent as an attachment to a spam, phishing, or spearphishing email, if the macro is enabled, it will quietly begin to install the malware application without any further notice to the recipient. What is different this time, is the recipient has to allow the macros to run. What the scammers do, is tell you that the macro warning is a special form of security and enabling it will allow you to read the entire message, some of which has been obscured. If you receive an email with a Word, Excel, or other Office document attachment,and it requires that you enable macros, the chances are that you are about to be attacked.
My rule of thumb is NEVER open an attachment unless you are expecting it, you know who it is from, and you know why they sent it. There is nothing wrong with replying to or calling the sender to confirm the authenticity of the email and attachment.
When in doubt, you can upload the file attachment to the VirusTotal website to have it verified.
This was reported by Sophos and a full article can be read in Virus Bulletin.
ShareSEP




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com