As reported by Symantec on June 30, and covered by the New York Times and SiliconBeat, there is a active exploit running against U.S. and European energy firms using the Dragonfly or Energetic Bear exploit kit. Similar to Stuxnet, this exploit seeks to gain access and control of the industrial control systems that manage the flow of electricity. oil, and gas. The article on Symantec is very through and gives a pretty technical readout, as well as the historical background of this exploit.
Their conclusions are disturbing, in that the perceive this to be a state sponsored threat, and that the attackers are based in eastern Europe. In addition to direct system and network hacking, it appears that the group used phishing emails targeted at senior employees at energy companies. These emails contained a malicious PDF attachment, and a subject line of “The Account” or “settlement of delivery problem.” Opening the attachment would install a remote access Trojan (RAT) which would allow the attacker full access to the compromised computer and allow for the installation of other malware and hacking tools. This allowed the attackers deeper access into the network of the utility company. These breaches, and there have been many (see chart below) could allow the sponsoring country to interfere with the delivery of electricity, oil, and gas.
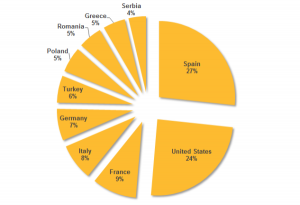
Figure. Top 10 countries by active infections (where attackers stole information from infected computers) – as shown on Symantec website
ShareJUL




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com