 A “bot-net” is a robot network comprised of hundreds, thousands, or even millions of “zombie hosts,” as computers that are infected with bot malware are called. Botnets are created by a type of professional cyber-criminal known as a “bot-herder,” and generally rented out to other criminals for sending millions of spam messages daily, running huge parallel processing tasks such as password cracking operation, or used by extortionists, hacktivists, and government sponsored or terrorist cyber-warriors for running distributed denial of service (DDOS) attacks. Your computer could be part of one of these botnets. How can you tell?
A “bot-net” is a robot network comprised of hundreds, thousands, or even millions of “zombie hosts,” as computers that are infected with bot malware are called. Botnets are created by a type of professional cyber-criminal known as a “bot-herder,” and generally rented out to other criminals for sending millions of spam messages daily, running huge parallel processing tasks such as password cracking operation, or used by extortionists, hacktivists, and government sponsored or terrorist cyber-warriors for running distributed denial of service (DDOS) attacks. Your computer could be part of one of these botnets. How can you tell?
If the hard drive light is flickering when you are not actually working at the computer, this may be a sign. But this kind of activity is also present if windows is running automatic updates, or your on-line backup program is uploading files to the cloud, or if your email program (Outlook, Thunderbird) is checking your mail server for new emails. When you are connected to the Internet and browsing websites, searching, or reading email, if it seems that your computer is very slow, or that the progress icon circles the drain endlessly, or your computer freezes up or crashes, there is a good probability that your computer may be doing work for another.
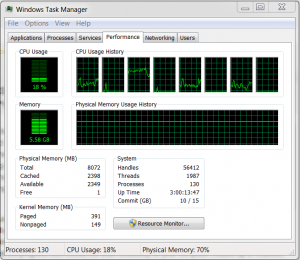 Another way is to open the Task Manager, but right clicking on the Task Bar and selecting it from the context menu. First check the Processes tab, click on the CPU label at the top of the column, and look to see if any process is consuming a large percentage of the processor cycles. The check the Performance tab to see how much over the CPU and memory are being consumed. If either of these are approaching 100% utilization, there may be a malware problem with your computer. Then open the Networking tab. If your network connect is pegged near the top of the graph, this indicates that there is an unusually high amount of traffic going out to your network or your Internet connect. High utilization on any of these tabs would warrant an inspection for botnet or other malware.
Another way is to open the Task Manager, but right clicking on the Task Bar and selecting it from the context menu. First check the Processes tab, click on the CPU label at the top of the column, and look to see if any process is consuming a large percentage of the processor cycles. The check the Performance tab to see how much over the CPU and memory are being consumed. If either of these are approaching 100% utilization, there may be a malware problem with your computer. Then open the Networking tab. If your network connect is pegged near the top of the graph, this indicates that there is an unusually high amount of traffic going out to your network or your Internet connect. High utilization on any of these tabs would warrant an inspection for botnet or other malware.
You can download software to detect and remove bot malware. A good option for individual computers is RUBotted from Trend Micro. This nifty free application runs in the background and runs WinPCAP, a packet capture software that is used to analyze your traffic for abnormalities. Another network based option is BotHunter from SRI International. While this is not a free application in the implementations I saw, if you are running a small to medium sized business network it would probably be worth the investment.
You may have read that President Obama is trying to get current computer crime laws changed to make it easier for the government to take down a botnet. Sounds great, but I am always reluctant to put anything into the hands of the same people who brought us crumbling highways and bridges, the federal Income Tax code, and the Unaffordable Care Act. But let’s remember that what they are talking about is taking your computer down, if it is part of that botnet. It would just be better for us to make sure that we are not “botted” on our own, and using the techniques and tools listed about can help you do just that.
Share
APR




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com