In June major parts of the GameOver botnet including the command and control servers, were taken down by police. There was a brief respite in the distribution of the CryptoLocker ransomware exploit, but it looks like the cybercriminals are back in action.
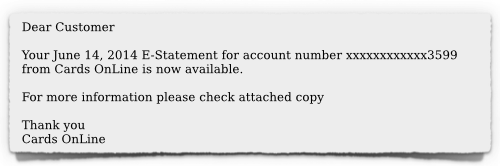
As reported by Sophos, the GameOver crew is back in action as of last week, sending out a spam barrage to trick the unwary into downloading the CryptoLocker ransomware. It appears that the email is designed to look like a dunning notice on a past due invoice. The unwitting victim, knowing that this notice is mistaken, then clicks on the ZIP attachment in order to see the invoice, and in doing so completes the download and installation of the exploit. Be on your guard for emails that look similar to the one pictured below:
We have also seen previous phishing spam from this group that looks like UPS or FedEx delivery failure notices. The notable feature is the presence of a file attachment using the .zip extension. Be wary of any emails you get with ZIP file attachments. When in doubt, you can upload the file attachment to the VirusTotal website to have it verified.
If you haven’t geared up to prevent this exploit from hijacking all your personal or business files and holding them for ransom, you may want to check out a couple of previous articles of mine on CryptoLocker, and how to prevent it from damaging your network.
ShareJUL




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com