Phishing Email Alerts
Catch of the Day: Office365 Phish
Chef’s Special: Ionos Blocked Messages Phish
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources on the Internet.
I would be delighted to accept suspicious phishing examples from you. Please forward your email to phish@wyzguys.com.
My intention is to provide a warning, examples of current phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your own inbox. If the pictures are too small or extend off the page, double-clicking on them will open them up in a photo viewer app.
Ionos Blocked Messages Phish
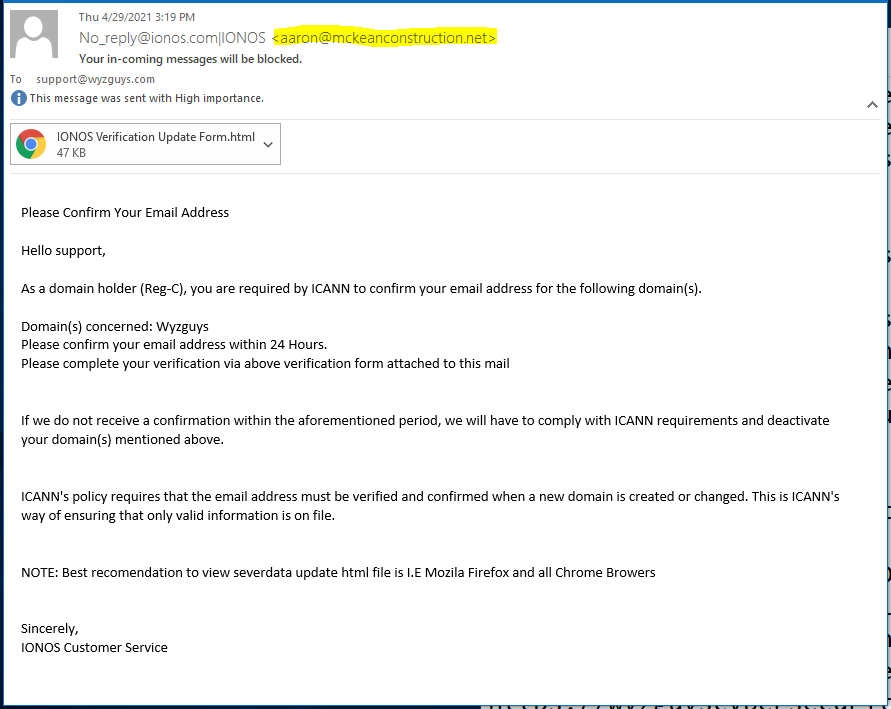
Here’s another credential stealing phish that uses an HTML attachment, which creates a landing page that is actually generated locally, and hosted in the victims computer. The email address of the sender is the first tip this is a scam.
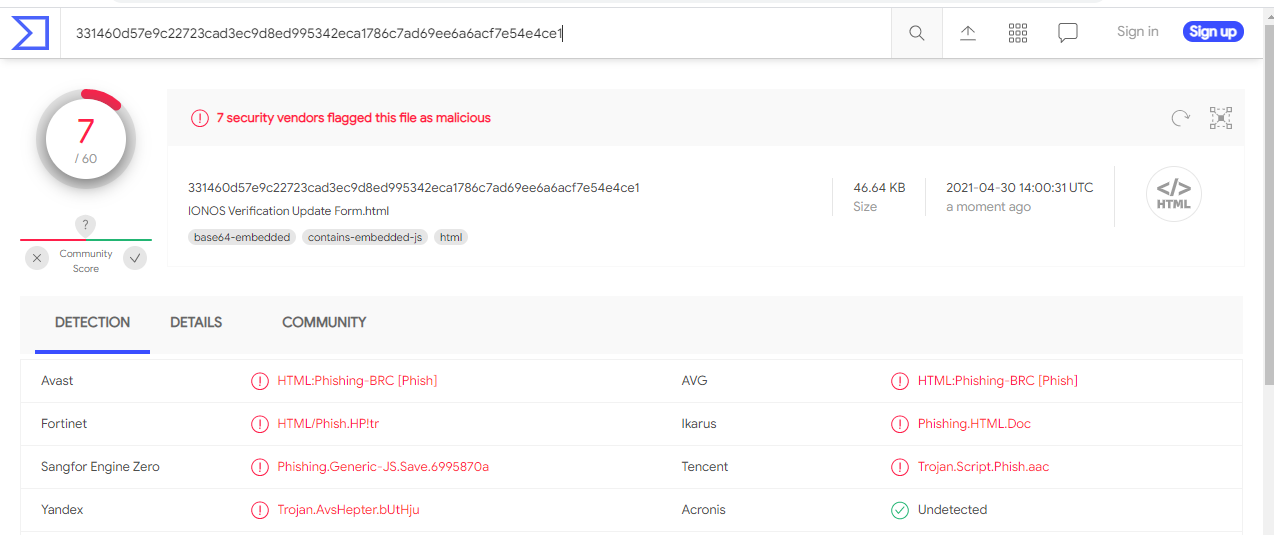
I tested the attachment on VirusTotal, and it was identified as a phishing Trojan.
I downloaded the file in Kali Linux, and then opened the attachment.
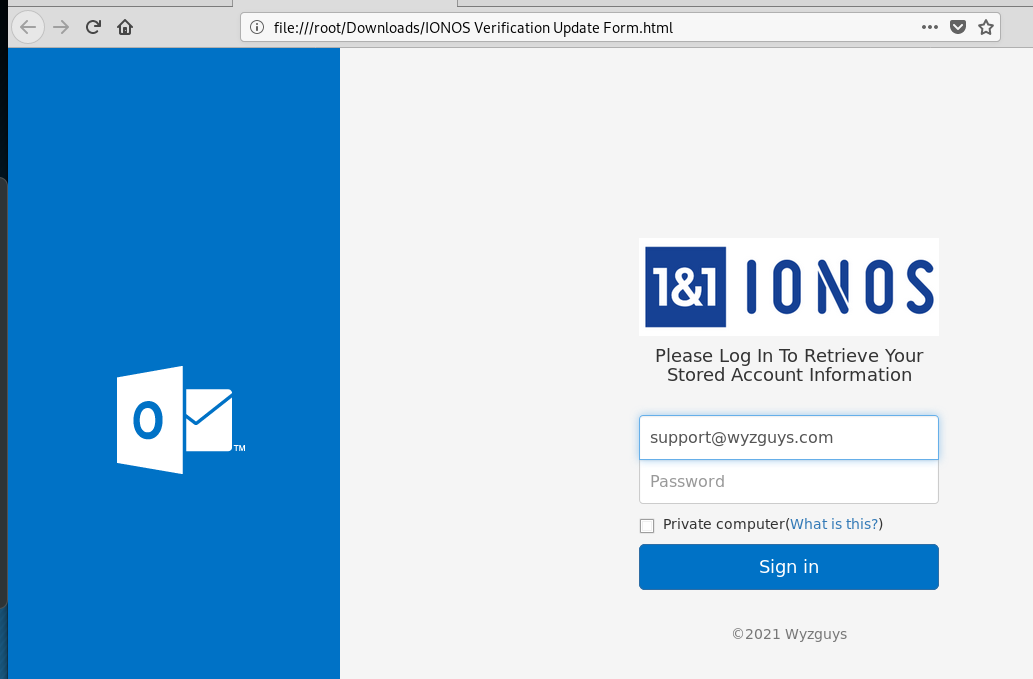
The HTML landing page was nicely done, but notice the URL in the address bar. This file opened in my computer, so my computer was acting as the “web Host.”
Be careful of these types of phish. I am seeing an increased use of HTML, PDF, and ZIP file attachments, and these can be very dangerous because oftern they contain malicious code that installs itself when you open the attachment.
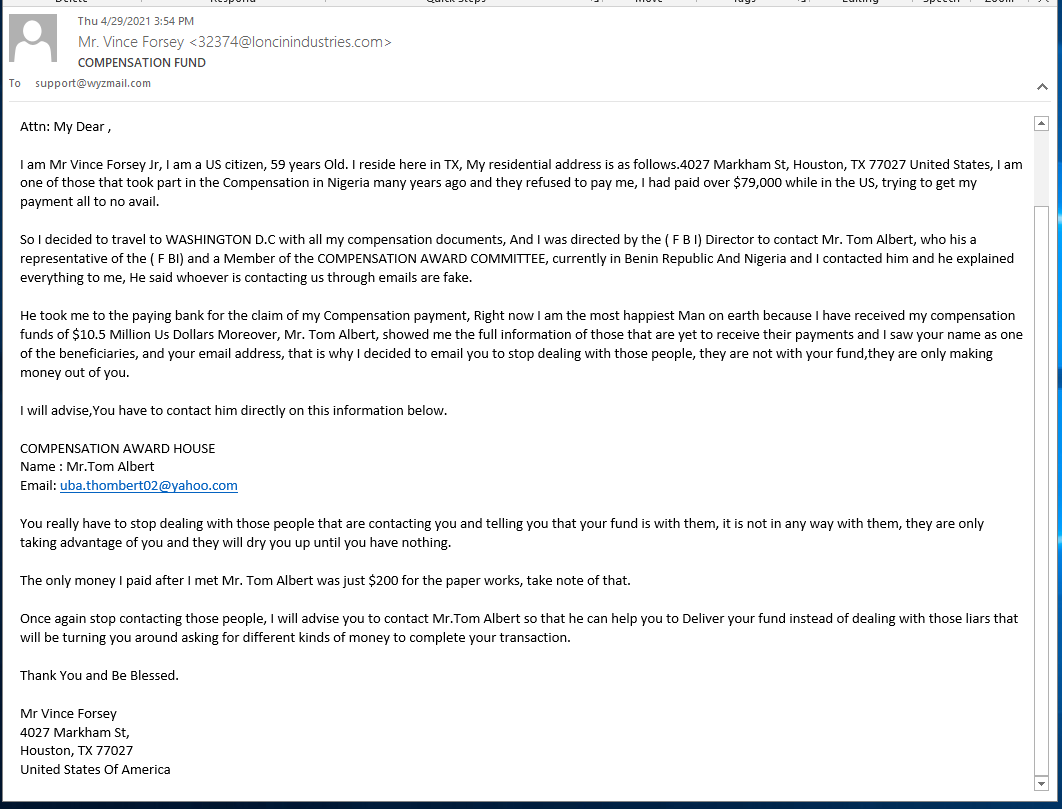
My Nigerian Prince Lives in Texas!
Please IGNORE these long and overly complex schemes that promise you millions that are hiding in African banks. Based on the language, grammar, and syntax of the message, this guy is foreign born. Hey his English is way better than my Nigerian, but you can tell this message is not from a US native.
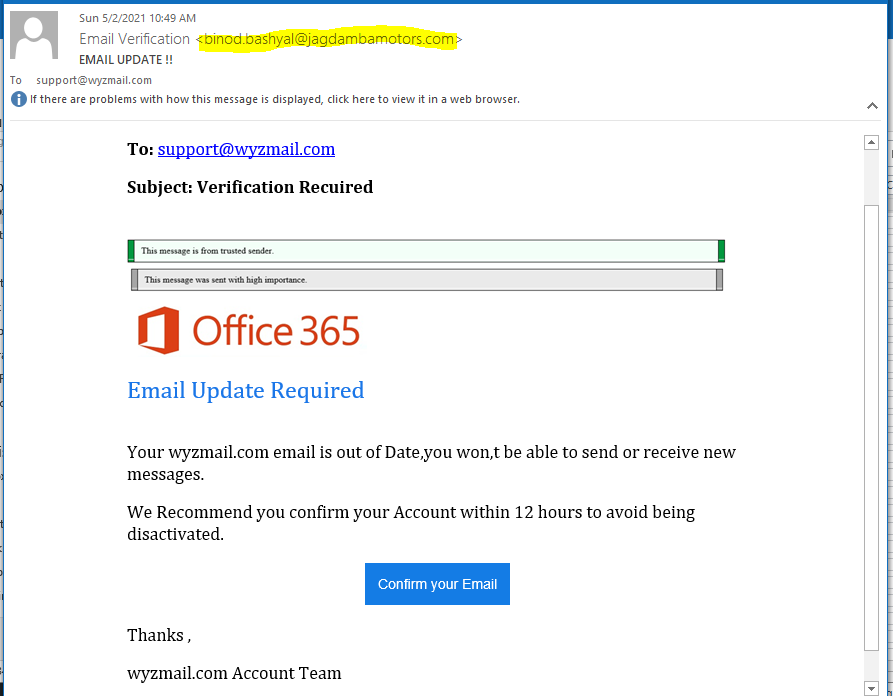
Office365 Phish
This stands out as an obvious phish due to the misspellings found at “Subject: Verification Recuired” and “avoid being disactivated.” The spoofed sender email is also a clear sign.
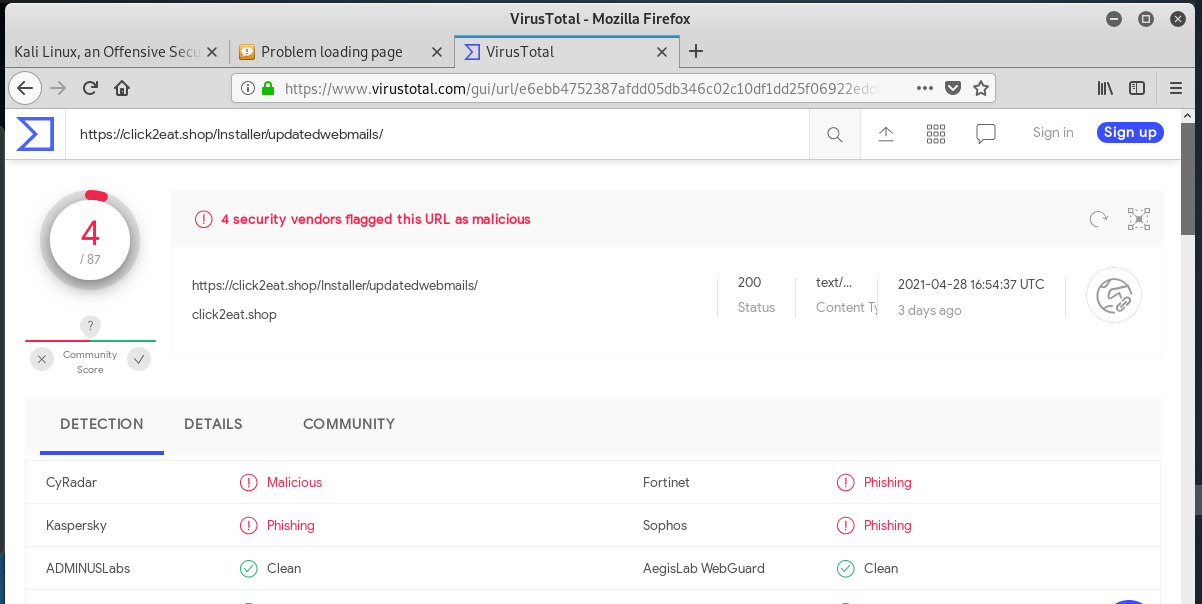
The Confirm Your Email button resolves to https://click2eat.shop/Installer/updatedwebmails//#support@wyzmail.com, but my attempts to connect were met with an error
A quick test of the link at VirusTotal shows it to be a known malicious phishing link.
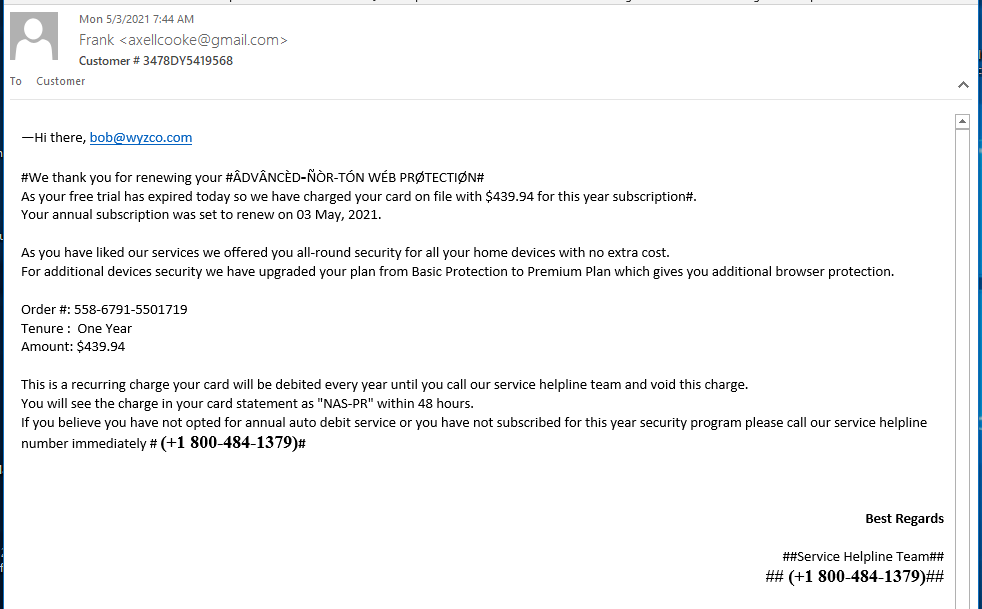
Norton Renewal Phish
I’ve been getting more of these call 800-number scams than usual. These scams depend on getting you angry enough about the “automatic renewal” charges to call the toll free number. Somewhere along that journey, you are separated from your money by a skilled social engineer posing as a “customer service rep.” The funny diacritical marks over some of the letters are designed to get this email past your spam and phish filtering. Most have worked, it got past all three of mine.
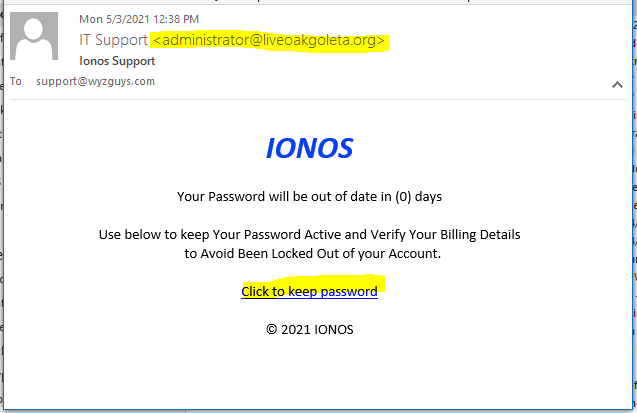
IONOS Password Phish
Here is another IONOS credential stealing exploit. The link resolves to https://s.id/kayop and is redirected to https://stevewoda.org/inonos-login-aspx/ionosmm/login.html. Here’s the email:
The landing page provided a log in form.
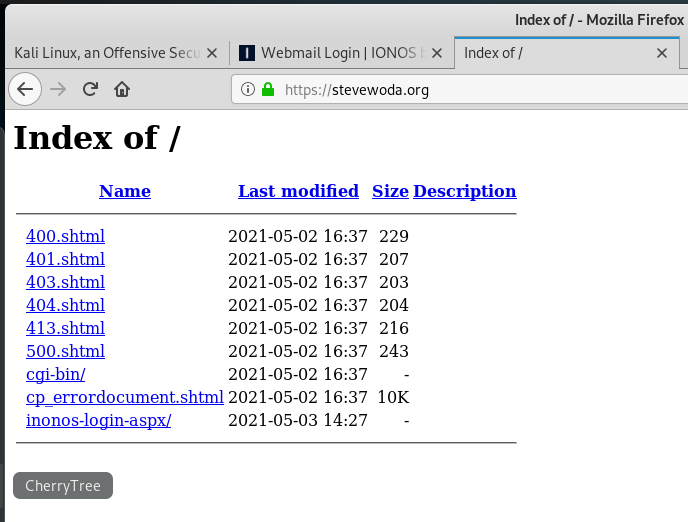
I checked out the URL to see if this was a hijacked web site and got this interesting index page.
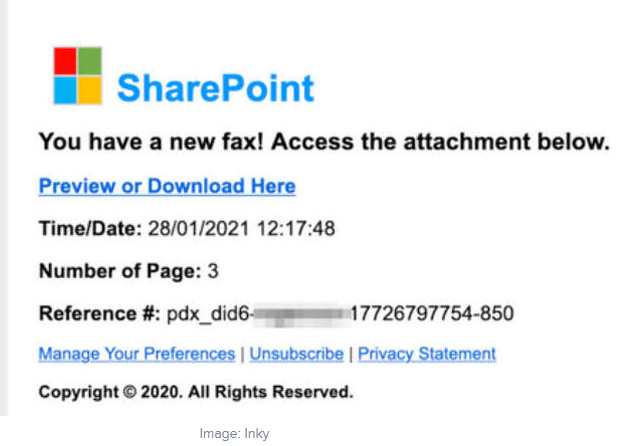
How phishing attacks spoofing Microsoft are evading security detection
The phishing emails use a Microsoft logo within an HTML table, which is not analyzed by security programs, says Inky. These phish typically redirect victims to a legitimate site, and then to a code repository which downloads and installs malware. Click here for the full story and more examples.
Share
MAY







About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com