 Phishing Email Alerts
Phishing Email Alerts
Catch of the Day: 419 Phish
Chef’s Special: Malware, Malicious Domains, and More
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources on the Internet.
I would be delighted to accept suspicious phishing examples from you. Please forward your email to phish@wyzguys.com.
My intention is to provide a warning, examples of current phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your own inbox. If the pictures are too small or extend off the page, double-clicking on them will open them up in a photo viewer app.
Slim pickings this week, only 2 phish
Hopefully our catch with be better next week.
419 Phish
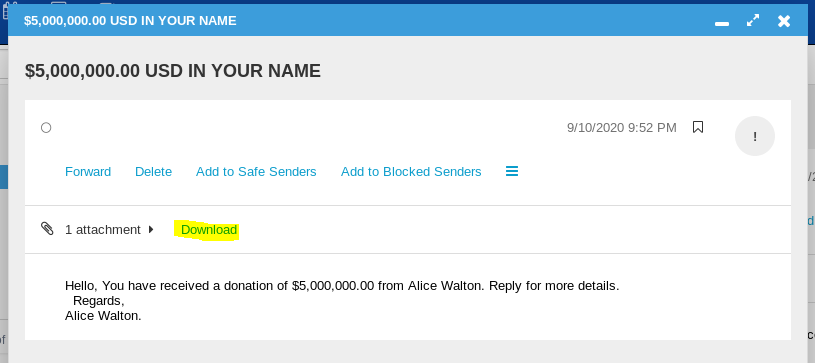
More “free money” offers from my email. Alice has sent me an email attachment. I wonder what it could be? Don’t try this at home, I am using my Kali Linux virtual machine for this investigation.
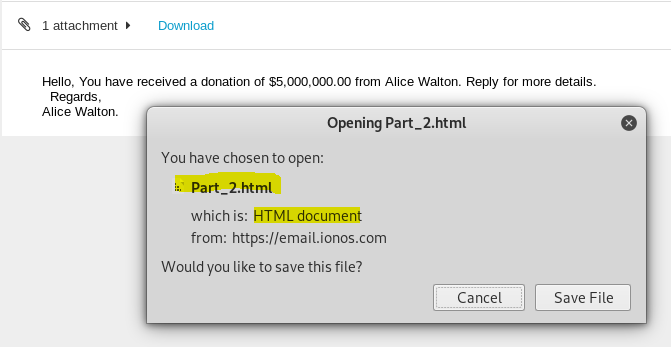
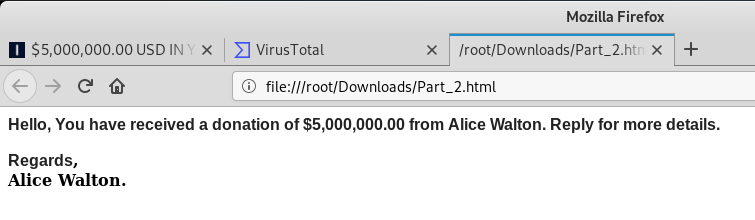
This is an HTML attachment, basically an un-hosted web page. Opening the attachment makes your computer the host. A quick analysis by Virustotal gave us no results. Let’s open it up and take a look
Nothing much to see here, it basically is a copy of the email message. I’d have to reply to play along.
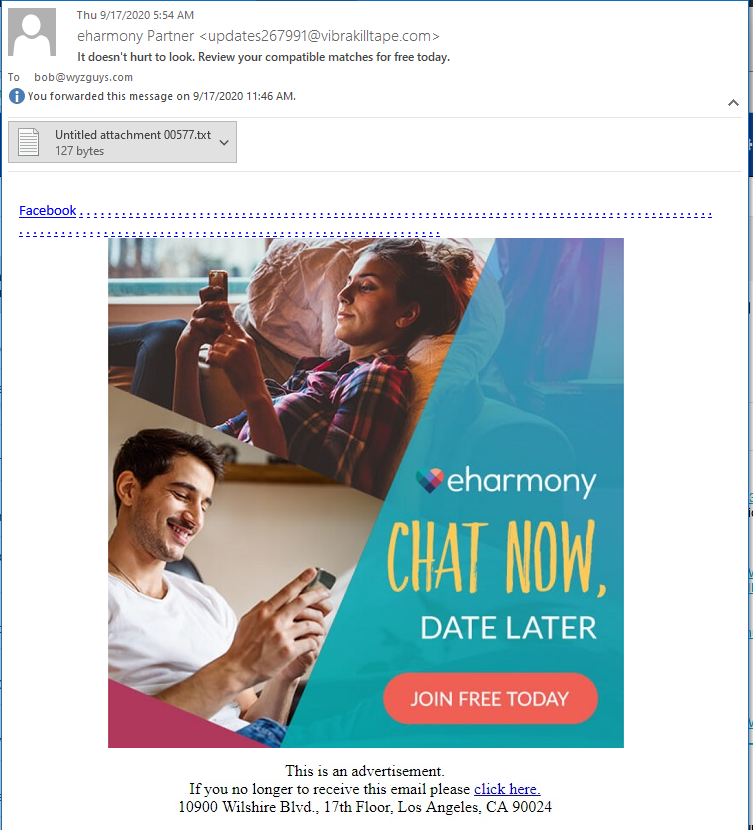
eHarmony Phish
Caught this email this week, too. Has a TXT attachment I am checking out on Virustotal. Virustoal found nothing int his attachment.
The picture hyperlink resolves to https://cdn.vibrakilltape.com/s-nKH[truncated]
This redirects to eHarmony after jumping through an affiliate marketing link. Not much of a phish. Throwing this one back.
Malware, Malicious Domains, and More: How Cybercriminals Attack SLTT Organizations
Vol. 15 / Issue 9 / September 2020
Cybercriminals continue to target U.S. State, Local, Tribal, and Territorial (SLTT) government organizations at an alarming rate. Attackers often target SLTT organizations because they know their security teams need to run complex networks, as well as deal with numerous third-party systems and services. Many SLTT cybersecurity teams are also struggling with reduced security budgets and a well-documented shortage of skilled cybersecurity and networking professionals to fill open positions. COVID-19, and the subsequent increase in remote working by government employees and online accessibility requests for government resources by citizens, has only added to their security challenges. continue reading →
Share
SEP




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com