 Catch of the Day: DHL Phish
Catch of the Day: DHL Phish
Chef’s Special: UN Phish
Also serving: History Phish
Examples of clever phish that made it past my anti-spam nets and into my inbox. Some are contributed by clients or readers like you, and other reliable sources on the Internet.
You can send phishing samples to me at phish@wyzguys.com.
My intention is to provide a warning and show current examples of phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your inbox. If the pictures are too small or extend off the page, double clicking the image will display them in a photo viewer app.
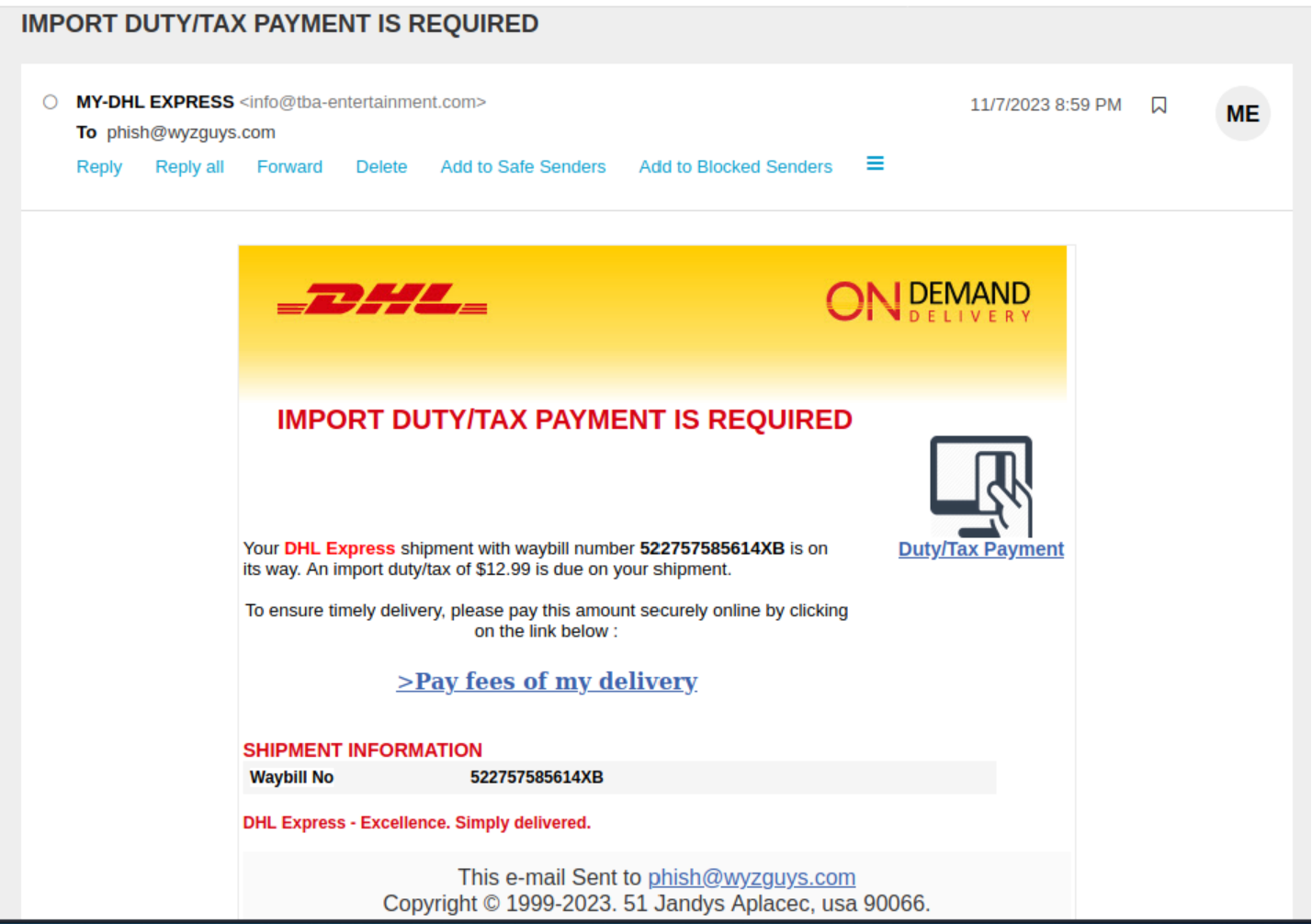
DHL Phish
I received this on Tuesday 2023-11-07, but failed to investigate this before the site was taken down. The link resolved to https://fotocuadros.com/New_Newsletters_Offers/ which most certainly is not DHL. Watch out for emails like this one. It looks like this was an attempt to get victims to pay “import duties” to the attackers.
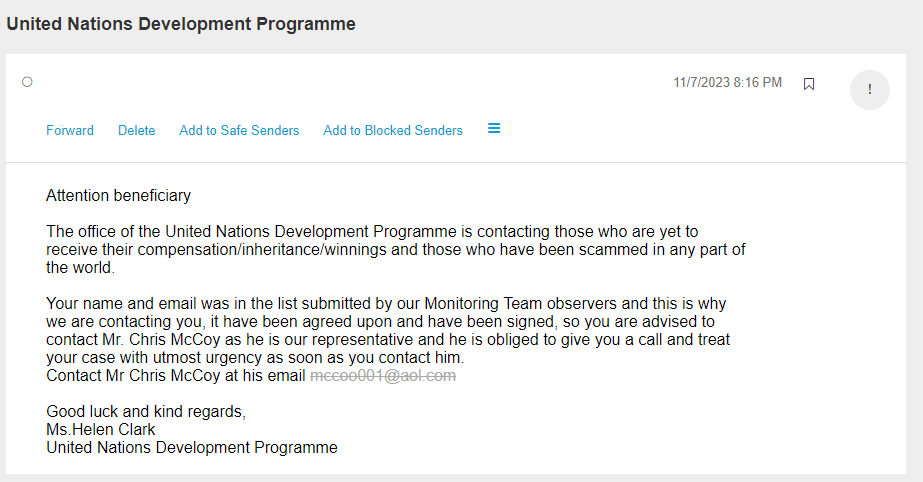
UN Phish
Occasionally I get emails from the United Nations. These are always scams, as is this one. Like anyone at the UN is using AOL email addresses!
[Don’t Get Trapped] The Dark History of Phishing and More Social Engineering
Social engineering attacks have a very long history, though the Internet has made it easier to launch these attacks en masse, according to Sean McNee at DomainTools. McNee points to an advance-fee scam from 1924, in which a crook sent a letter pretending to be trapped in a Spanish debtors’ prison.
The sender requested that the recipient send a check for $36,000 to pay off his debt. After the sender is freed, he promises to pay the recipient back, with an extra $12,000 for the trouble. Criminals still use this scam today, often posing as Nigerian princes.
Here are some best practice DomainTools offers to help users avoid falling for social engineering attacks:
- “Look out for unsolicited emails, messages, or phone calls, especially if they request sensitive information or immediate action. Phishing messages can create a sense of urgency or fear to pressure recipients into quick responses.”
- “If an offer seems too good to be true, it most likely is. Scammers use enticing offers to lure victims.”
- “Ask someone else for their opinions on a specific email or interaction. Sometimes a second review on a suspicious interaction can help you see the scam for what it is.”
- “Use multifactor authentication (MFA) for your accounts online, especially accounts with sensitive personal information such as your finances or email. Never give your MFA code to anyone who asks for it, only to the service webpage you are actively logging into.”
- “If you’re part of a critical business process, such as approving wire transfers, establish a secondary out-of-band process to validate these transactions. If you are in the same physical office, for example, agree to talk to the other approver face-to-face. If you’re remote, create a second communications channel, like text messaging, phone calls, or Slack, for approvals.”
Blog post with links:
https://blog.knowbe4.com/brief-history-phishing-social-engineering
And then there is the article at CNBC about how a 77-year-old widow lost $661,000 in a common tech scam: ‘I realized I had been defrauded of everything’. Share this:
https://www.cnbc.com/2023/10/08/how-one-retired-woman-lost-her-life-savings-in-a-common-elder-fraud-scheme.html
Share
NOV




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com