 Catch of the Day: Docusign Fax Phish
Catch of the Day: Docusign Fax Phish
Chef’s Special: Magecart Phish
Also serving: EvilProxy Phish, Obfuscation Phish
Examples of clever phish that made it past my anti-spam nets and into my inbox. Some are contributed by clients or readers like you, and other reliable sources on the Internet.
You can send phishing samples to me at phish@wyzguys.com.
My intention is to provide a warning and show current examples of phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your inbox. If the pictures are too small or extend off the page, double clicking the image will display them in a photo viewer app.
Docusign Fax Phish
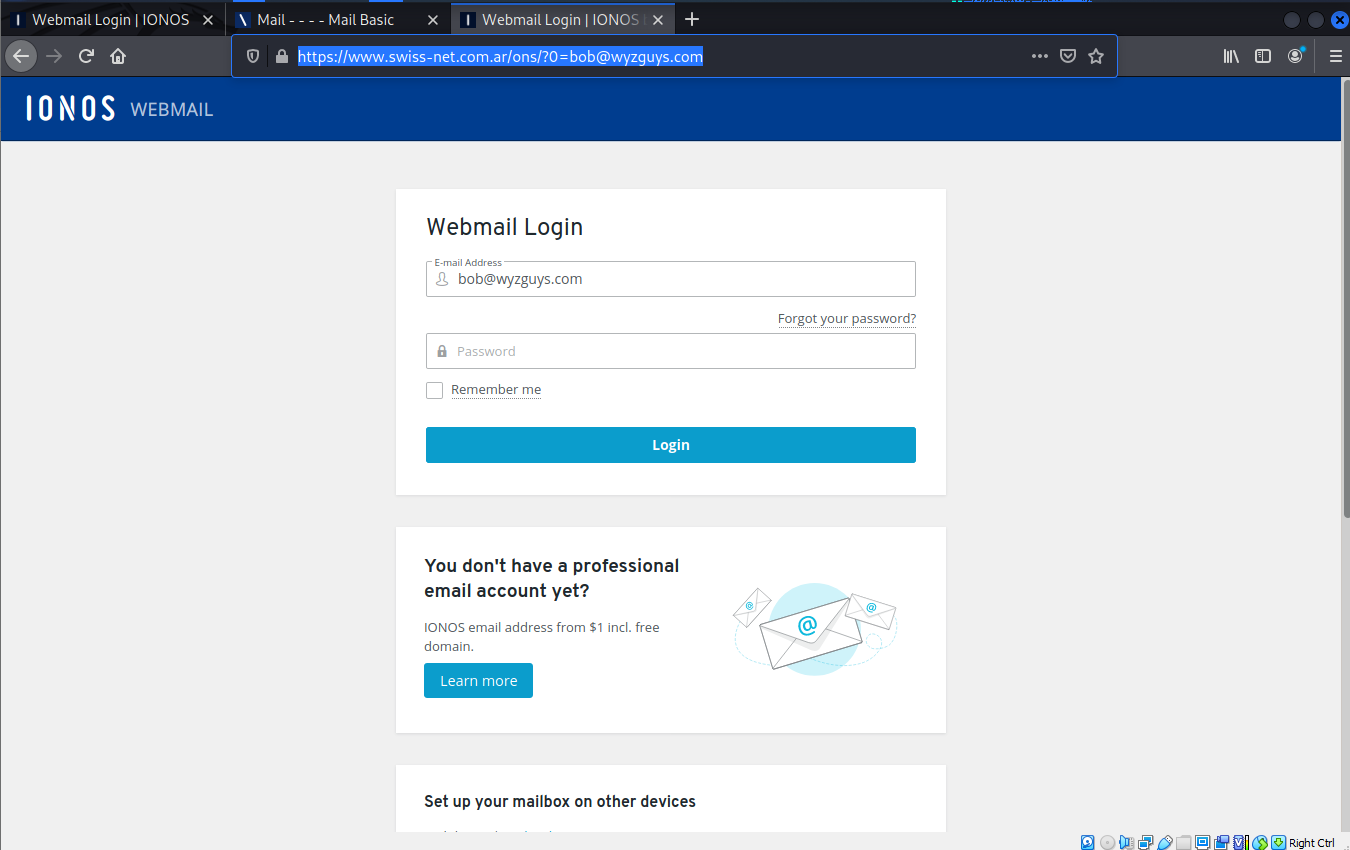
I received this email on Thursday 2023-10-12. This is a pretty standard credential stealing exploit. The Review Document link resolved to https://r20.rs6.net/tn.jsp?f=001Ve7A96wMMi_aN9n1VBrupZxh_cxAfMFNefIYT6ipPBnUNN7HqUiWY0KgXtOaq30oc8yM55xlf6FxqNmKYfShbaYbA34gRkJ3WOk4oX3eRLmfSDCry9D8pAVJ3Br5ZCZaLPu30ZONRJpeCeLL2jaRZXGRVES4WN9XqGPSQceKFLHzXraYhqkhng==&c=txzuvgd3pMVWonHRvAHlXBWqLsy_fbBk34EZj7LATr018ghs-d90sQ==&ch=cwyfLx0m1IaHR03wjFzUhSkOY_2vEOTN7z-1qeiHaY-QGf67PEQolw==&__=Ym9iQHd5emd1eXMuY29t and redirected to https://www.swiss-net.com.ar/ons/?0=bob@wyzguys.com
The AR cc-tld is for Argentina. Here is the email
And here is the landing page. Notice the URL, this would not be an IONIS web address.
I received the same email on a couple of other email addresses of mine. Just delete and move on,
The Art of Concealment: A New Magecart Campaign That’s Abusing 404 Pages
A new, sophisticated, and covert Magecart web skimming campaign has been targeting Magento and WooCommerce websites. Some of the victims of this campaign are associated with large organizations in the food and retail industries.
According to the evidence we’ve uncovered, this campaign has been active for a couple of weeks, and in some cases, even longer. This campaign managed to surprise us with a high-level concealment technique that we had not previously encountered. More..
[Risky New Data] More Than Half of Phishing Scams Now Use Obfuscation
A new report shows staggering phishing trends using obfuscation techniques that should make any organization feel worried. In Egress’s annual Phishing Threat Trends Report, new data was collected from January to September of this year with some key findings I want to highlight:
Phishing Campaigns Have Become More Sophisticated and Effective
Since obfuscation techniques were implemented the percentage of phishing emails increased by 24.4% this year, and now 55.2% of cybercriminals are using these tactics in their phishing emails.
Because of this, Microsoft cybersecurity defenses were bypassed by 25% year-over-year, and phishing emails are 29% more effective at fooling secure gateway products. One strategy bad actors are trying to execute in their attacks is chaining together multiple obfuscation methods to be successful.
The Most Widely Used Obfuscation Technique is HTML Smuggling
Research shows that 34% of obfuscated phishing emails analyzed use the HTML smuggling technique. Hackers distribute malware to appear dormant to make it more difficult to identify. As a result, the HTML page with the raw source code is really malware, which is why it’s so difficult for network-based cybersecurity tools to spot.
AI Tools Are Not Detecting Obfuscation Techniques
Egress also cautioned that artificial intelligence tools are being taken advantage of by threat actors to launch their phishing campaigns. On the other side of the coin, tools designed to detect AI-generated phishing emails are unreliable or don’t work in 71.4% of cases.
In a statement by Jack Chapman, VP of Threat Intelligence at Egress, “Without a doubt chatbots or large language models lower the barrier for entry to cybercrime, making it possible to create well-written phishing campaigns and generate malware that less capable coders could not produce alone.”
These findings highlight the importance of educating your end users with new-school security awareness training. End-user education is the only way these types of obfuscation attacks can be stopped with helpful tips to spot and report these types of malicious attacks.
Blog post with links:
https://blog.knowbe4.com/half-phishing-emails-use-obfuscation
Senior Executives Beware: The Rise of EvilProxy Phishing Campaigns
Menlo Security warns that a social engineering campaign is using the EvilProxy phishing kit to target senior executives across a range of industries, including banking and financial services, insurance, property management and real estate, and manufacturing.
EvilProxy allows threat actors to conduct adversary-in-the-middle (AitM) attacks by “harvesting session cookies enabling threat actors to bypass MFA protections.”
The phishing campaign exploited an open-redirect vulnerability affecting the job listing site Indeed. This allowed the attackers to craft a phishing link that appeared to lead to Indeed’s legitimate website, but redirected to a spoofed Microsoft login page. The blog post explains the attack chain.
Blog post with links:
https://blog.knowbe4.com/senior-executives-beware-rise-evilproxy-phishing-campaigns
Share
OCT





About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com