Catch of the Day: New Secure Message Phish
Chef’s Special:
Also serving:
Examples of clever phish that made it past my spam filters and into my inbox. Some are sent by clients or readers like you, and other reliable sources on the Internet.
You can send phishing samples to me at phish@wyzguys.com.
My intention is to provide a warning and show current examples of phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your inbox. If the pictures are too small or extend off the page, double clicking the image will display them in a photo viewer app.
New Secure Message Phish
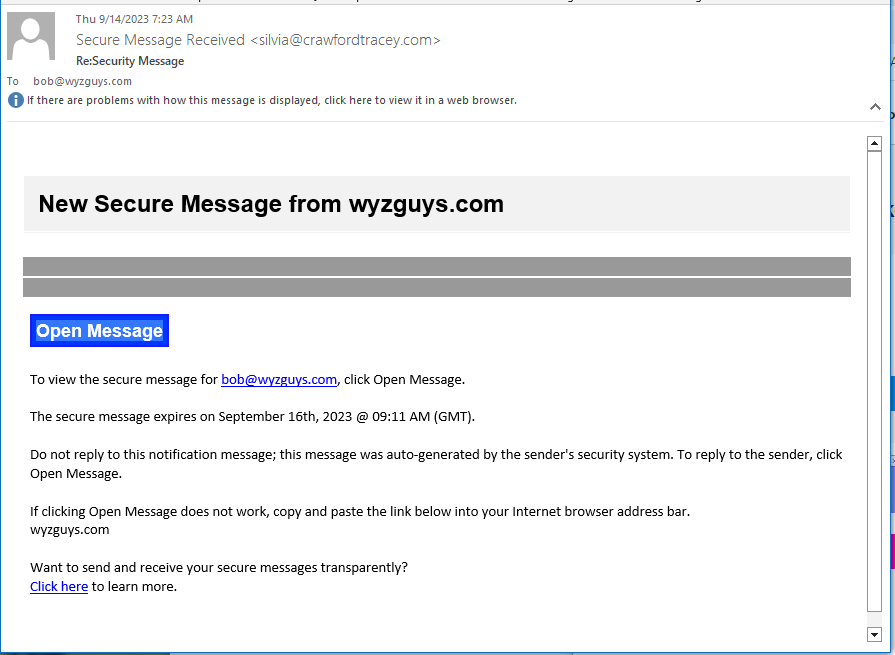
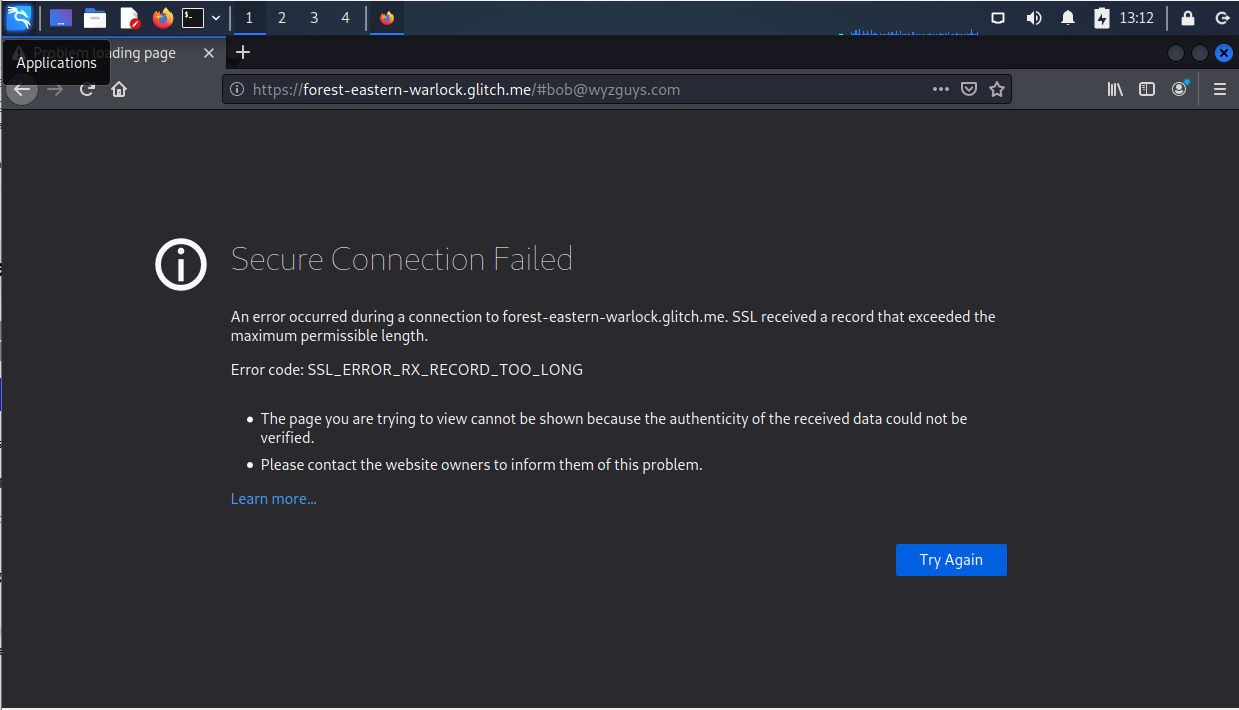
This was received on Thu 9/14/2023 at 7:23 am. I was able to investigate by noon of the same day, but the exploit was either set up incorrectly, or had already been taken down. The sender email address Secure Message Received <silvia@crawfordtracey.com> is incorrect for the domain. The Open Message link resolves to https://forest-eastern-warlock.glitch.me/#bob@wyzguys.com. But when I tried to get to the landing page, instead I got an error message.
Here’s the email
Here is where the landing page is supposed to be, but instead I got this error message
Here is information I got following the learn more… link at https://support.mozilla.org/en-US/kb/secure-connection-failed-firefox-did-not-connect?as=u&utm_source=inproduct
The domain glitch.me is a popular public site for creating quick and simple websites, which may be why the attackers are using Glitch Me to host the landing page. The error message may be the result of Glitch Me taking down the exploit site.
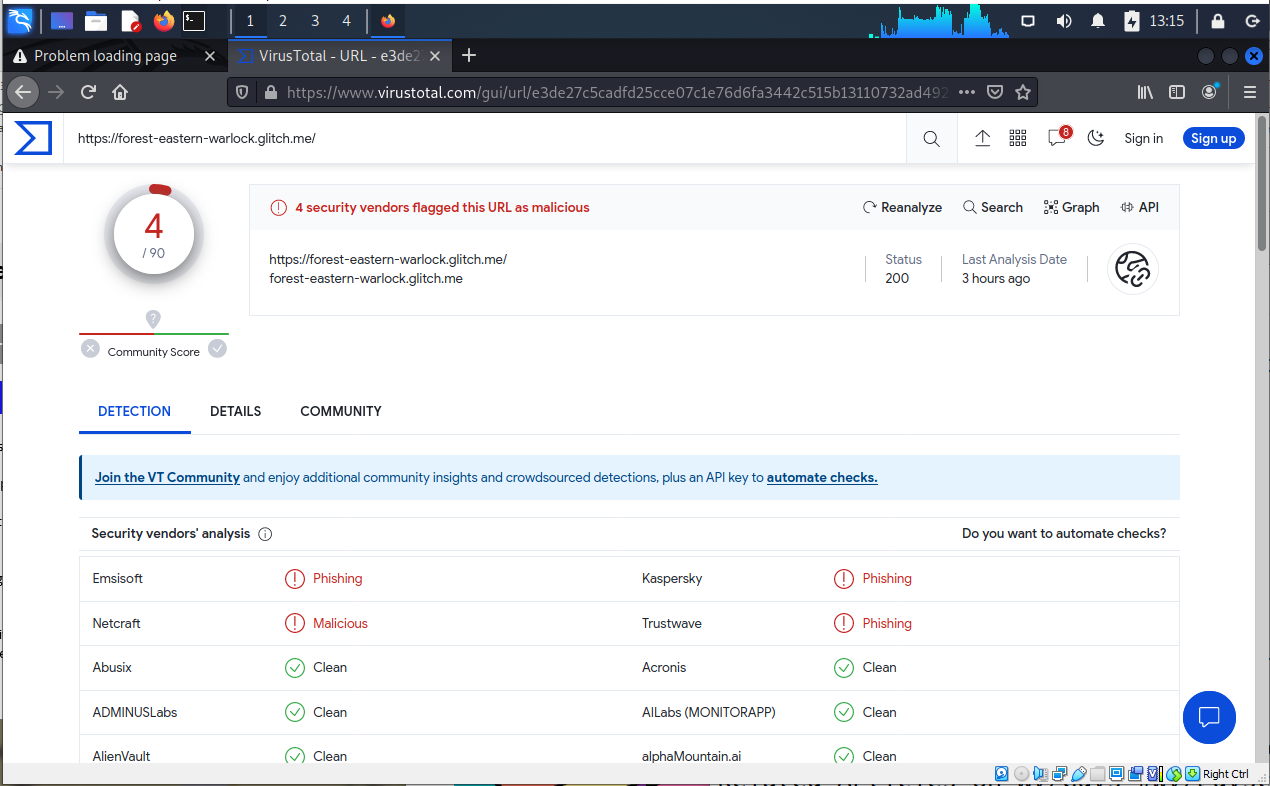
Further verification of the URL on virusTotal.com shows that this is a known phishing link. Further evidence that the site may have been taking down in the 4 hours between when I (and presumably hundreds of other people) received the email, and when I was finally able to investigate.
The good news is that VirusTotal and Glitch Me were quick to identify this exploit and take it down.
Share
SEP





About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com