Phishing Email Alerts
Catch of the Day: Citibank Payment Phish
Chef’s Special: BEC Phish
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources on the Internet.
I would be delighted to accept suspicious phishing examples from you. Please forward your email to phish@wyzguys.com.
My intention is to provide a warning, examples of current phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your own inbox. If the pictures are too small or extend off the page, double-clicking on them will open them up in a photo viewer app.
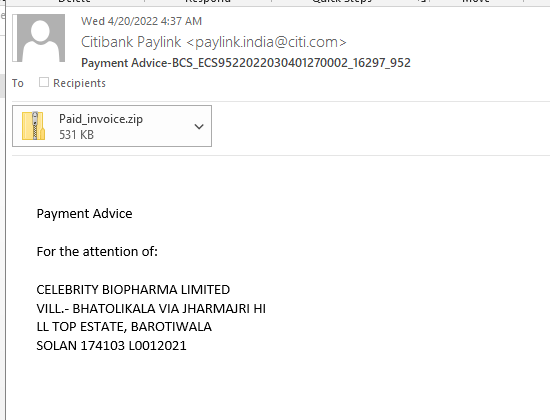
Citibank Payment Phish
I got this phish with an attachment titled Paid_invoice.zip. I don’t see attachments too often anymore, so this was an interesting investigation. The source was an email address from India
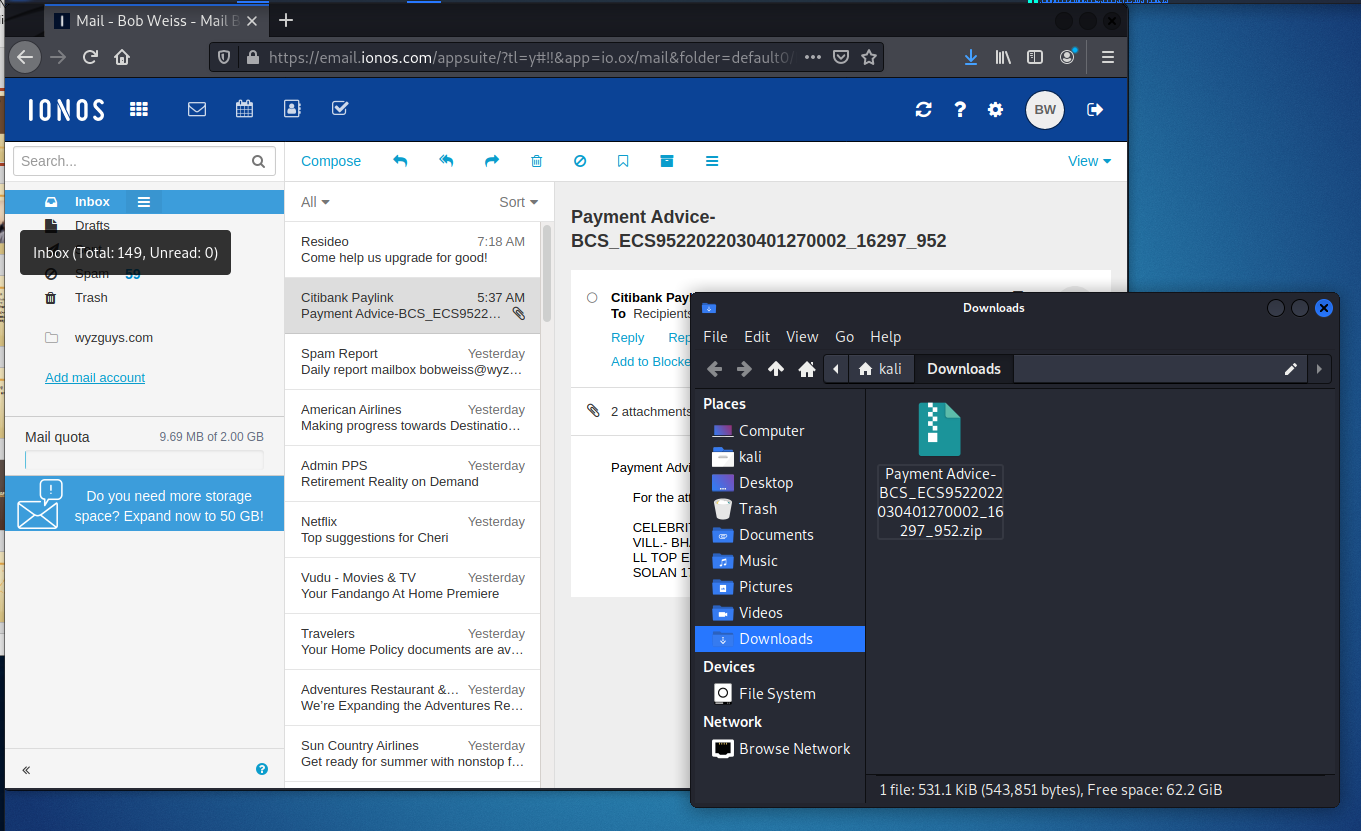
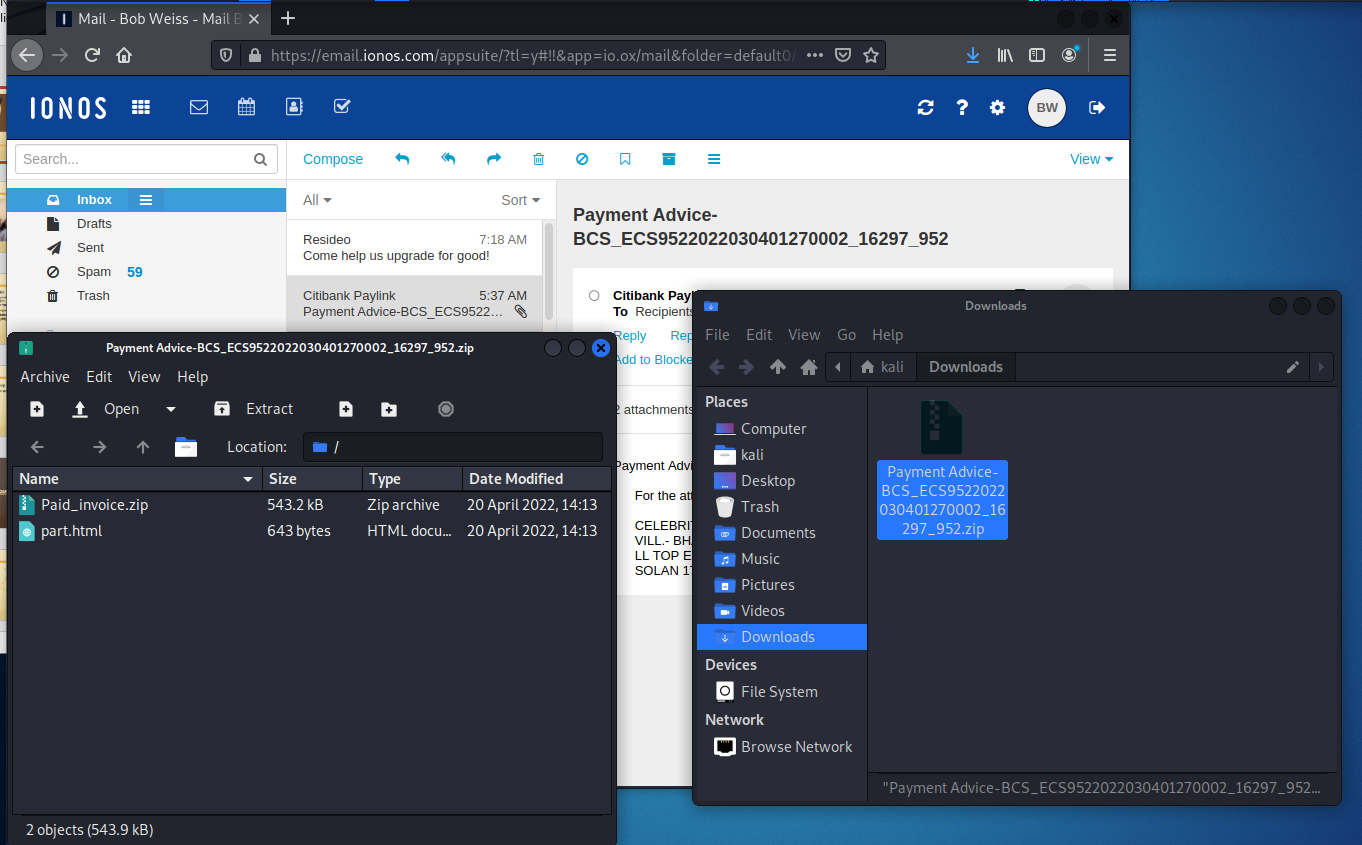
So I opened the email in my Kali Linux VM, and opened the attachment, which was in a ZIP or archive format
The archive contained another ZIP file, so this would defeat an email security system that opened and inspected ZIP attachments
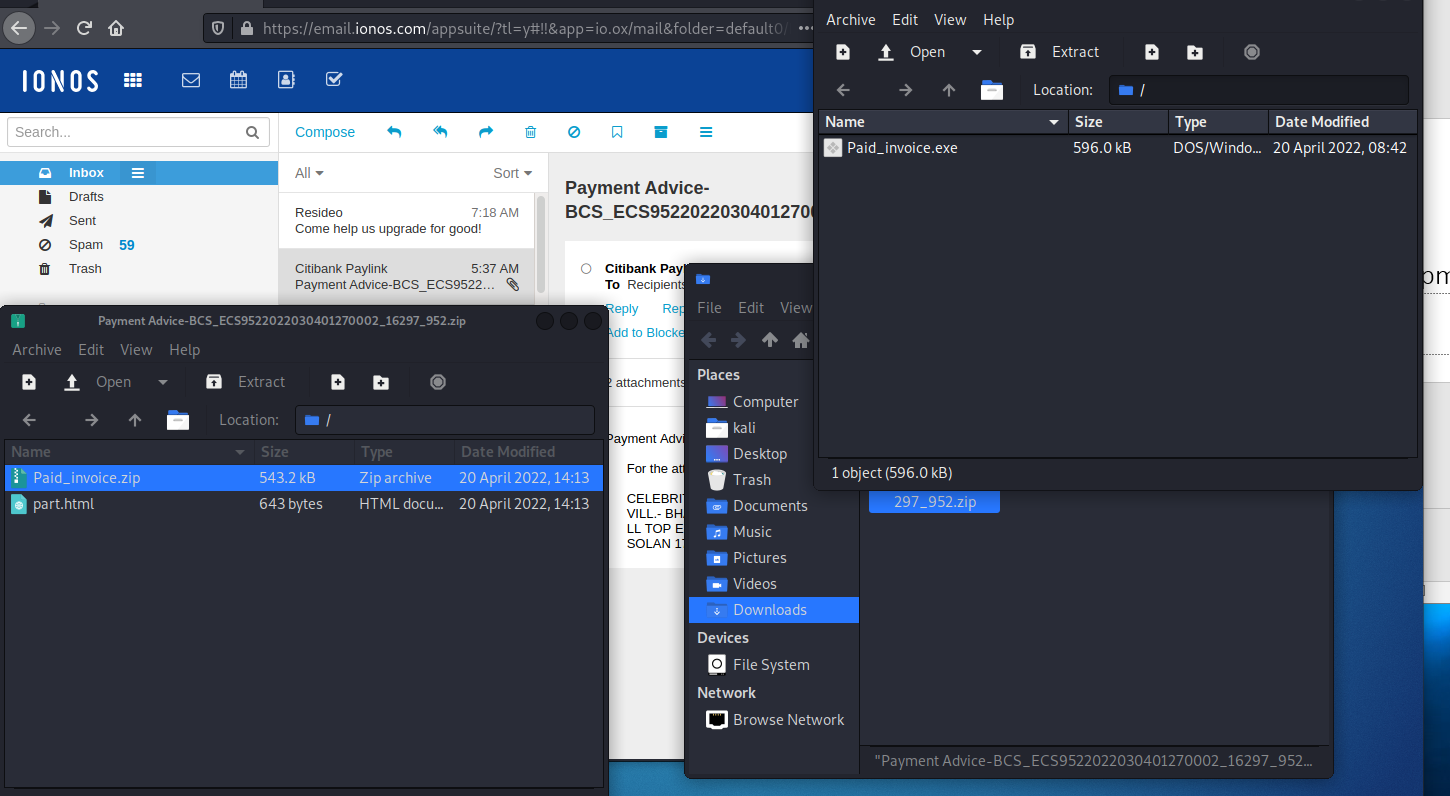
Opening the second ZIP revealed an executable program called Paid_invoice.exe. This was undoubtedly some sort of malware.
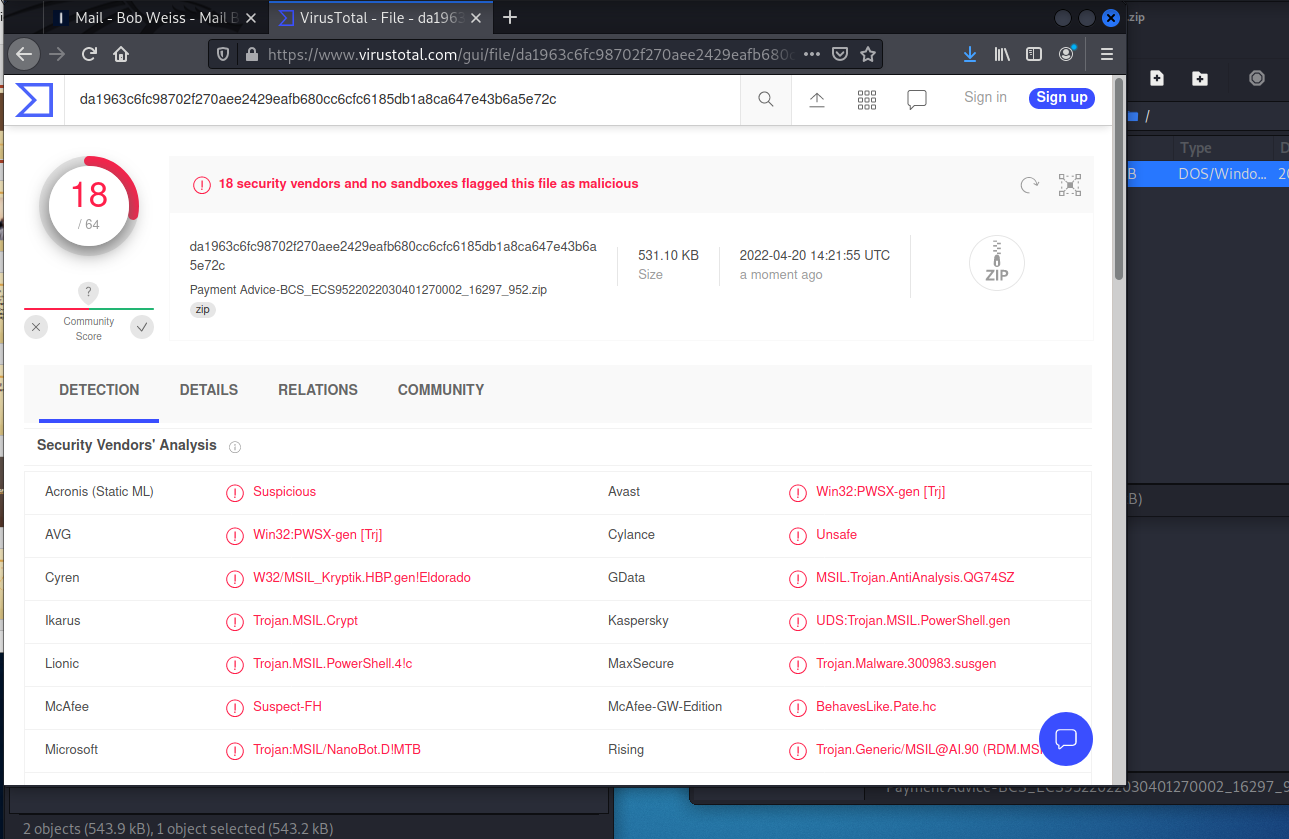
I ran the sample through VirusTotal, which revealed it as a well known Trojan horse.
You can avoid trouble like this one by verifying any ZIP attachments with the sender, or submitting the email to your Information Security department or VirusTotal.
The Costliest Cybercrime: Business Email Compromise (BEC)
Organizations in the U.S. lost $2.4 billion to business email compromise (BEC) scams (also known as CEO fraud) last year, according to Alan Suderman at Fortune.
“BEC scammers use a variety of techniques to hack into legitimate business email accounts and trick employees to send wire payments or make purchases they shouldn’t,” Suderman writes.
“Targeted phishing emails are a common type of attack, but experts say the scammers have been quick to adopt new technologies, like ‘deep fake’ audio generated by artificial intelligence to pretend to be executives at a company and fool subordinates into sending money.”
Suderman cites a case from San Francisco, where a nonprofit lost more than half a million dollars to one of these scams.
“In the case of Williams, the San Francisco nonprofit director, thieves hacked the email account of the organization’s bookkeeper, then inserted themselves into a long email thread, sent messages asking to change the wire payment instructions for a grant recipient, and made off with $650,000,” Suderman says. More…
Q1 2022 Report: Holiday-themed Phishing Emails Entice Employees To Click
Business, Online Services, and HR-Related Messages Get the Most Clicks
Business phishing emails remain the highest-clicked category around the world. This category contains typical communication that employees might receive. The subjects of these emails include fake invoices, purchase orders, requests for information, shared files, and more. Online Services includes messages that claim to be from well-known companies and most of the time contain spoofed domains of popular websites within the email copy.
HR-related messages could potentially affect daily work and spoof the users’ own domain with an “HR” mailbox name. The common thread is that the emails convey a sense of urgency and entice users to take an action.
Holiday Schedule Changes and Gift Notifications Trigger an Emotional Response
In our latest quarterly phishing report, we found that holiday-themed emails were the most tempting for employees to click on. HR-related messages such as a change in the schedule for the holidays likely piqued interest from employees to see if they would receive an extra day off or shortened work schedule due to the holidays.
It is important to remember that cybercriminals utilize various tactics such as preying on people’s emotions when executing their malicious scams. Remaining vigilant and adopting a heightened sense of suspicion around emails that trigger an emotional response can end up preventing a detrimental cybersecurity attack.”
See the Full Infographic with Top Messages in Each Category for Last Quarter:
https://blog.knowbe4.com/q2-2022-phishing-results-holiday-emails-entice-employees
LinkedIn was the most exploited brand in phishing attacks last quarter
Phishing attacks aimed at stealing LinkedIn account credentials surged during the first quarter of 2022, says Check Point Research.
For the first quarter of 2022, LinkedIn accounted for 52% of all phishing-related attempts analyzed by Check Point across the world. Its position at the top of the rankings revealed a major increase from the previous quarter when LinkedIn was in fifth position, accounting for only 8% of all phishing attempts. During the quarter, LinkedIn snagged the top spot from DHL, which dropped to second place, appearing in 14% of all attempts.
Beyond LinkedIn and DHL, other brands that appeared on the list included Google, Microsoft, FedEx, WhatsApp, Amazon, Maersk, AliExpress and Apple. The exploitation of LinkedIn is part of a larger strategy in which attackers are leveraging social networks ahead of shipping companies like DHL and technology players like Google and Microsoft. More…
Share
APR





About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com