The password may not be dead, but it is on life support, and the prognosis is bad. Death is not only inevitable, it is immanent. The increasing power of password cracking software and machines, and the proliferation of complete Rainbow tables of solved passwords on the Dark Web markets mean your clever 8, 9 or 10 character password probably has been cracked already and is for sale on the Internet.
One solution to this situation has been the increased use of two-factor authentication (2FA) methods. There are four major versions being offered, and any of them is better than a password alone. You should definitely find out if your bank or brokerage account offers two-factor authentication, at a minimum.
The main methods are:
- Card and PIN or Chip and PIN. We are all pretty familiar with this, as it is how an ATM card works. You have to have the information on the card stripe (or coming soon – on a chip embedded in the card) and a Personal Identification Number (PIN) to complete your transaction. This method does not work online, only in person.
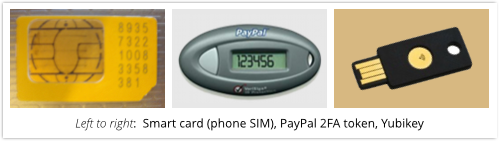
- Smart Cards or Keys. This may be a special SIM in your phone, or a token that has a number that changes every 60 seconds, or a USB devices that provides additional authentication when inserted into your computer.

- Login Verification. Under this scenario, a login notification is sent to your smartphone. Once it is confirmed, you are logged into the account.
- One-time passwords via SMS to a smartphone. When you log in to your online account, a password or number is sent to your phone via SMS, and you enter this number into your browser login page.
- Authentication Apps. This is an application that you install to your smart phone, and uses a combination of a cryptographic seed and the date and time to generate a one-time code that is good for 30 or 60 seconds. This is how the Google Authenticator works.
Of course all of these solutions have issues, if you are out of range of cell service, or overseas, some of these smartphone based systems won’t work. And if you lose your token or USB device, well, good luck. If they are stolen you have other problems. But no system is perfect, and if you have options like these available to you, you should set them up and use them, especially with financial accounts.
For more information check out this article on Sophos.
ShareDEC




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com