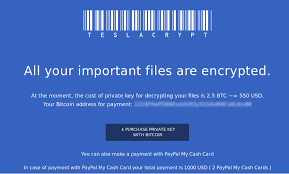
 Crypto-ransomware continues to be one of the most popular money making exploits for cyber criminals. The reason for this is simple; its works, and the return on investment is quite high. According to a recent article in Naked Security, the score will reach $1 billion in 2017.
Crypto-ransomware continues to be one of the most popular money making exploits for cyber criminals. The reason for this is simple; its works, and the return on investment is quite high. According to a recent article in Naked Security, the score will reach $1 billion in 2017.
A poll by the IBM company found that nearly 50% of the businesses polled had been hit by ransomware, and of those 70% paid to be the information returned. Of those:
- 11% paid $10,000-$20,000
- 25% paid $20,000-$40,000
- 20% paid more than $40,000
In my own professional experience I have seen the aftermath first hand. At one company there were two instances separated by a week, when two different employees were tricked into opening a ZIP attachment on a fake FedEx shipping advice email. They were fortunate the damage was limited to the individual’s computers, but without backups their data was irretrievably lost. Management declined to pay the ransom in this case, but offered to let the affected employees do so if they wanted to.
At another non-profit I dealt with lost everything on the victim’s computer, as well as a shared Dropbox information store that contained all the various forms and information that they used to run their operations. While the affected computer was re-imaged, none of the lost data was retrieved because the non-profit declined to pay.
There are many other instances, too many to enumerate here.
One thing to be aware off, is that most crypto-ransomware exploits will also encrypt data located on servers attached via drive mappings. You may want to look at other ways to connect people to resources. You also want to limit connections to those individuals who truly need access. You should definitely remove the Everyone group for all shared connections. This gives the malware unrestricted access to shared files.
There are a few anti-malware companies that are starting to offer anti-ransomware protection for endpoints. The two I am aware of are Sophos and Malwarebytes. I expect there to be others. I would recommend checking with your anti-malware company and seeing what they have in their new offerings, and pick something that will protect your endpoints from this exploit.
Backups are a critical resource in recovering your lost files. On-line troves such as Dropbox obviously do not protect against encryption exploits, so this does not count as backup.
Automatic online backup services such as Carbonite may suffer from the same issues. When I contacted Carbonite last year about their ability to restore after a crypto-ransomware attack, they said they said their system would just backup the changed files. I think Carbonite may still be effective, since the file names are usually changed with the encryption malware. This would not be a total loss, since the originally named files should survive, and not be replaced.
A real backup solution would involve using some sort of dedicated network attached storage. Where I work we use Datto backup products, and our clients are able to restore original files from the Datto appliances.
These are a few ways you can prepare for, and survive, a crypto-ransomware attack. We hope the tips provided here can give you a safer and more productive new year.
ShareJAN




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com