 Phishing Email Alerts
Phishing Email Alerts
Catch of the Day: Netflix Account Grabber
Chef’s Special: A 4-pack of IONOS email account hijack attempts
Examples of clever phish that made it past my spam filters and into my Inbox, or from clients, or reliable sources on the Internet.
I would be delighted to accept suspicious phishing examples from you. Please forward your email to phish@wyzguys.com.
My intention is to provide a warning, examples of current phishing scams, related articles, and education about how these scams and exploits work, and how to detect them in your own inbox.
Alert: Massive registration of COVID-19 related domains
Over 130,000 domain names related to the COVID-19 pandemic have been registered in the last several months. While some of these registrations are for legitimate companies, organizations, and purposes, it is a safe bet that most of these are being using in phishing schemes. By using fear, the promise of information, or other social engineering techniques, cyber-criminals are using the pandemic to separate people from their money, email account credentials, or other valuable personal information. A good defensive strategy is a strong skepticism backed up with “click aversion.” Do NOT believe everything your read. Do NOT click on the link or open an attachment without checking it our using techniques we have explained in previous episodes of the Friday Phish Fry. Stay safe out there.
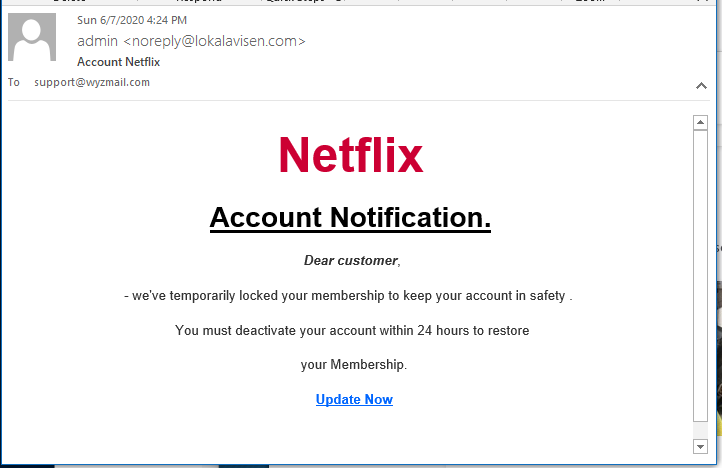
Netflix phish
This came to me as a simple credential stealing phish. Netflix accounts have resale value on the Dark Web.
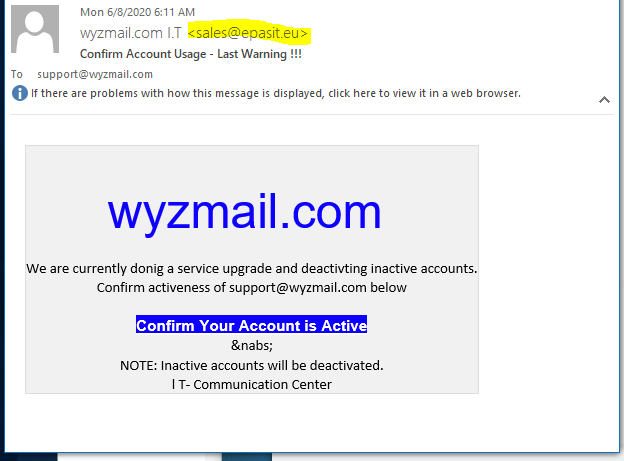
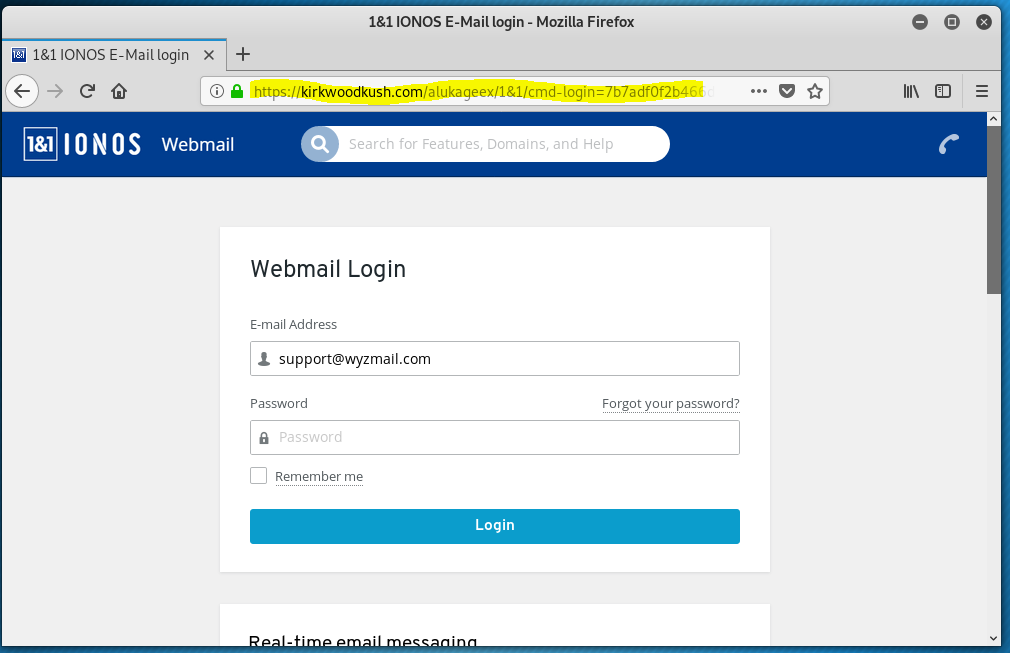
IONOS email account credential stealing phish
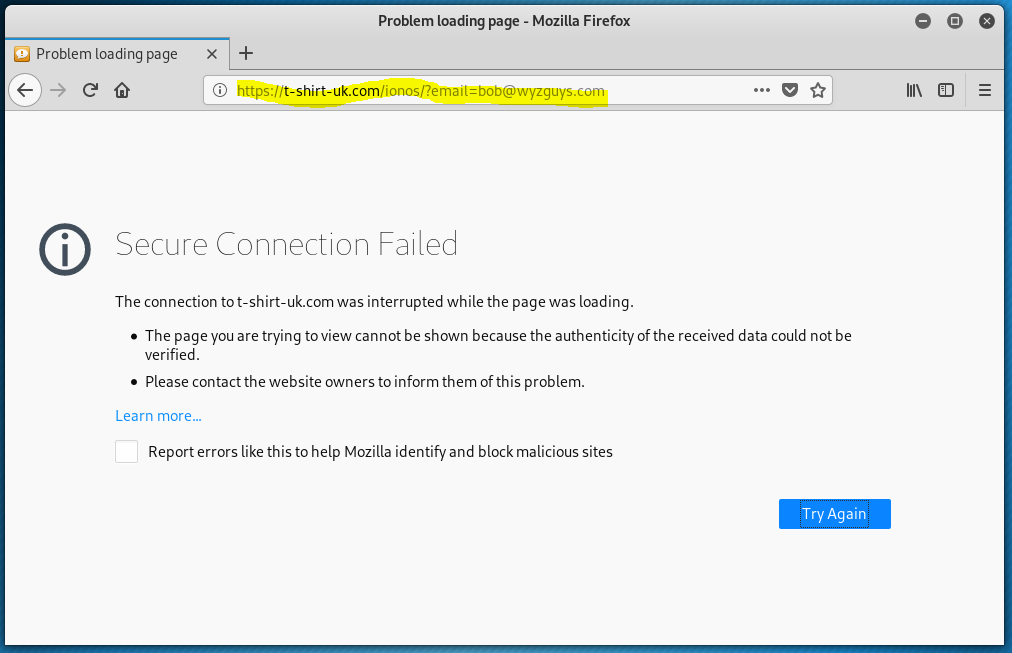
The sender’s email address and the confirmation link address were both clues that this was a phish.
These were all targeted attacks. I have used IONOS and its predecessor 1&1 for many years, This information is publicly available from registration databases such as WHOIS. They used a familiar vendor to make these phish more believable, in an effort to get my email account and web hosting credentials.
Why does this matter to you? These exploits are built in a way that that could easy use GoDaddy, Google Gmail, Microsoft Office365 and Outlook.com logos and trade dress. Phish landing in YOUR inbox will be customized to use web and email hosting companies that you use. You should be looking at these examples to familiarize yourself with the tactics, the types of emails used. Expect to see them customized to use logos and trade dress that is familiar to you.
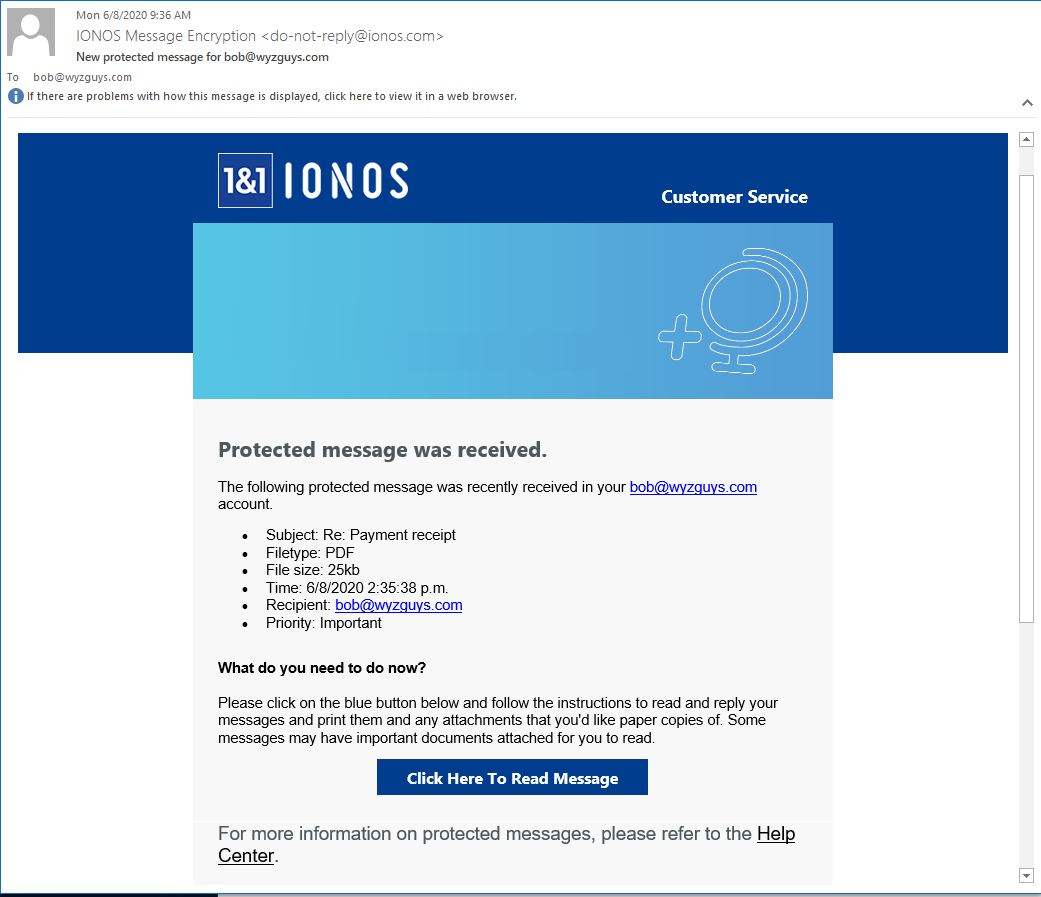
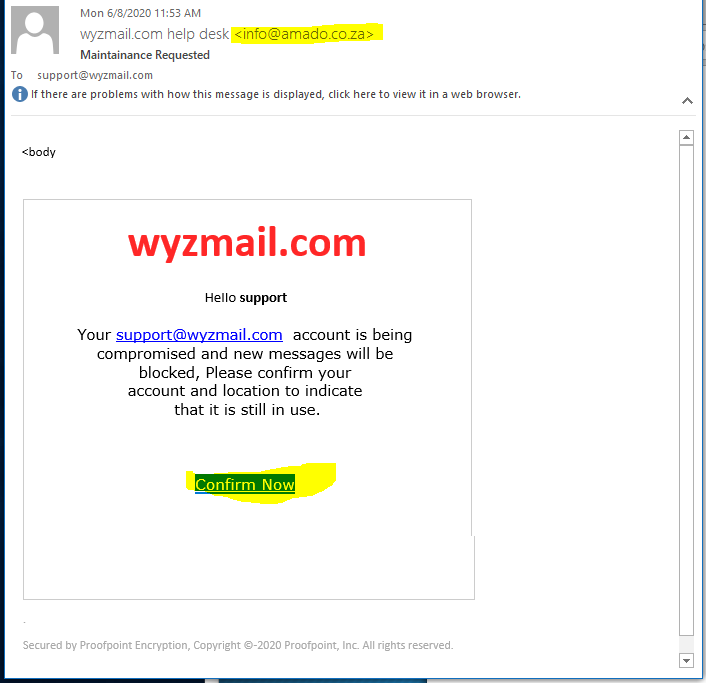
IONOS protected message phish
Here’s another shot at collecting may email account credentials.
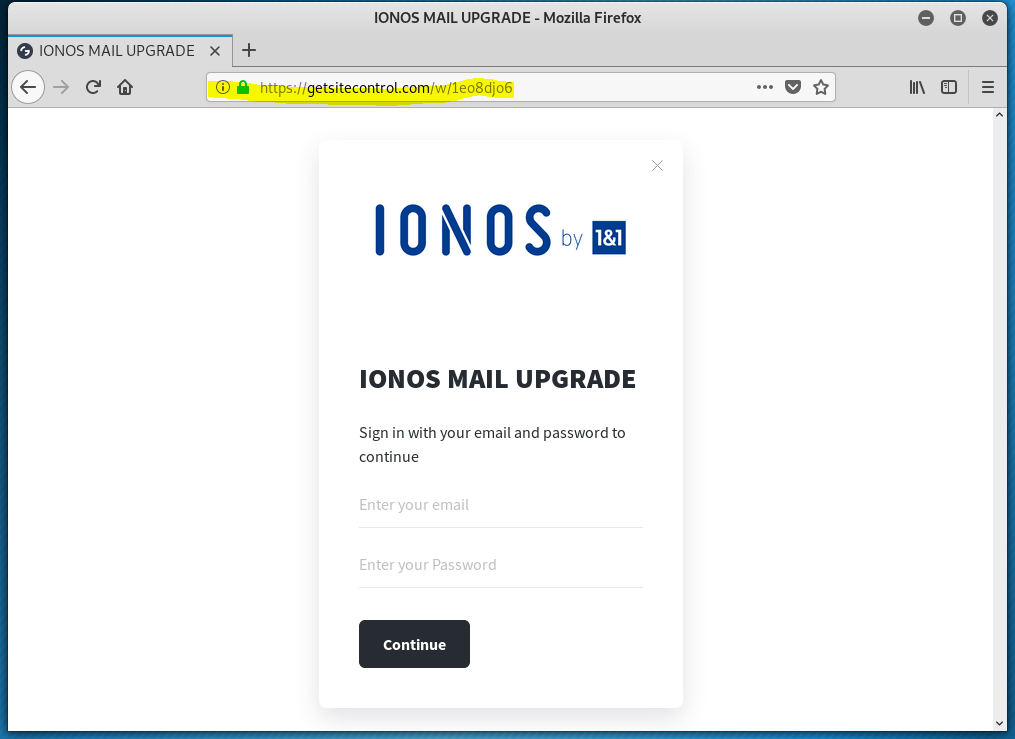
A third IONOS cred-stealing phish!
I guess someone really wants my email account. But the third time is not the charm for this phisher.
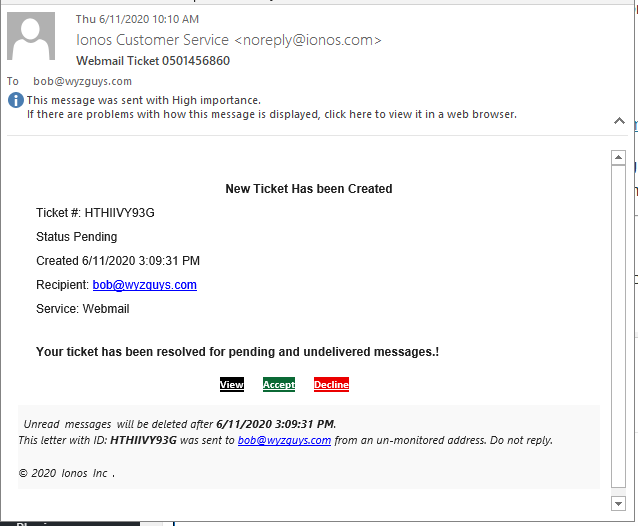
And yet a fourth IONOS cred-grabbing phish
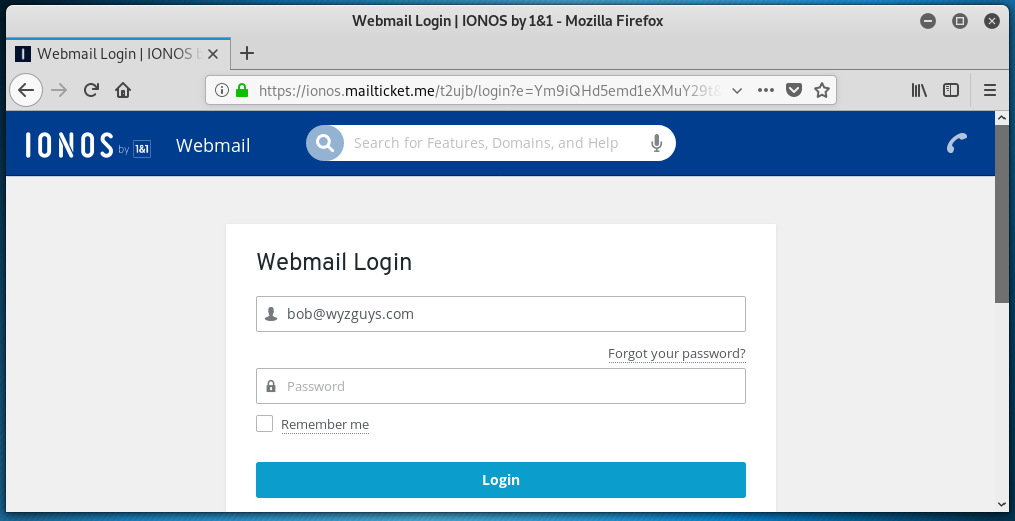
Here is another phishing email. Clicking on View, Accept, or Decline all resolve to this web address: https://www.biognostica.co.il/redirectv5/x00xbob@wyzguys.comx00x.
This connection is redirected to https://ionos.mailticket.me/t2ujb/login?e=Ym9iQHd5emd1eXMuY29t&p=1&session=696f6e6f732e6d61696c7469636b65742e6d65, This took me to another realistic looking landing page set up to steal my password.
Notice the look alike domain ionos.mailticket.me. The actual domain is NOT IONOS, but mailticket.me. IONOS is a subdomain, which domain could theoretically be used in other explots targeting a different email provider such as Gmail or Outlook.com simply by changing the subdomain to something like gmail.mailticket.me.
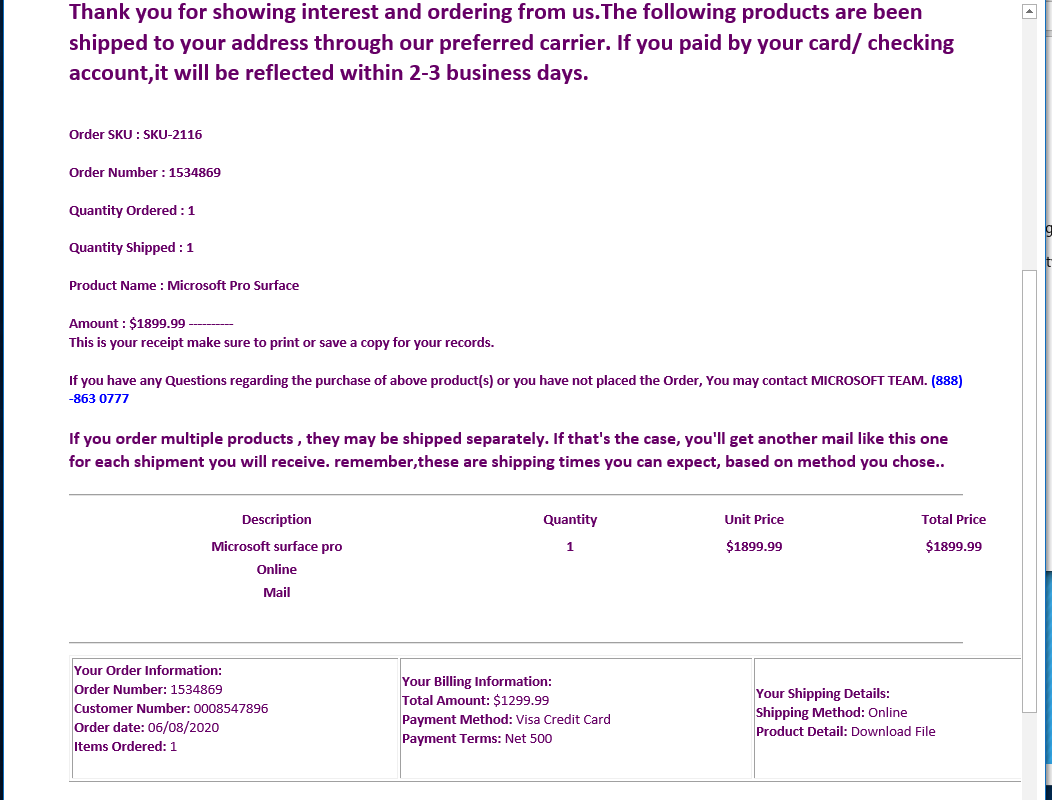
Fake Surface purchase advice
A client of mine sent me this email, and it looks like someone bought a $2000 Microsoft Surface Pro. The lure is the toll free number. A call there would probably connect you to a scam artist who would gather credit card or other personal information.
Crooks hijack “Black Lives Matter” to spread zombie malware
The email says it will let you have your say anonymously about Black Lives Matter. Do not open this email!
Subject: Vote anonymous about "Black Lives Matter" Leave a review confidentially about "Black Lives Matter"
This is an exploit to install Macro virus malware.
Cybercriminals now spoofing job hunters to deploy password-stealing malware
Malicious emails with file attachments masquerading as resumes and curriculum vitae are being sent to businesses to install malware that can capture passwords and other sensitive information, says Check Point Research.
The Value of a Hacked Email Account
Why would someone want to steal your email account user ID and password, also called account credentials? Here is the answer from Brian Krebs. “One of the most-viewed stories on this site is a blog post+graphic that I put together last year to illustrate the ways that bad guys can monetize hacked computers. But just as folks who don’t bank online or store sensitive data on their PCs often have trouble understanding why someone would want to hack into their systems, many people do not fully realize how much they have invested in their email accounts until those accounts are in the hands of cyber thieves.” Read more...
JUN





About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com