 There has been a lot in the press about ransomware this year. Crypto-ransomware attacks are becoming more targeted and sophisticated, resulting in bigger extortion amounts and other financial losses to the victims.
There has been a lot in the press about ransomware this year. Crypto-ransomware attacks are becoming more targeted and sophisticated, resulting in bigger extortion amounts and other financial losses to the victims.
But last year’s most frequent and expensive cyber-crime is still email account compromise, or what the FBI calls Business Email Compromise (BEC) is still with us. The attackers using this exploit have also become more sophisticated.
A recent example is the $742,377 invoice that was sent to the city of Ocala Florida from a compromised email account of an actual building contractor that was working with the city on an airport project. Since it arrived from the actual email account of the contractor, the invoice was paid. But the payment was sent to a bank account controlled by the cyber-criminals.
In August 2019, a county in North Carolina paid $17 million to fraudsters who used the hijacked email account of a legitimate contractor working on a school.
This year the Portland Public Schools system narrowly avoided a similar scam that would have cost them $2.9 million.
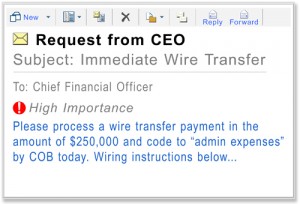 There are steps you can take to avoid falling for a similar invoice or wire transfer scam.
There are steps you can take to avoid falling for a similar invoice or wire transfer scam.
- Inform or train your employees, especially those in finance, accounts payable, and similar departments about this sort of scam. Informed employees are more likely to question these sorts of phishing emails.
- Do not use emails alone for approving payment. Use the phone or another non-email communication channel to confirm the amount and verify that the email was actually sent by the company.
- Be especially dubious of emails from vendors with new bank account or payment instructions. These absolutely need to be confirmed before sending any payments. Again, a quick phone call can save you thousands and even millions of dollars.
- If it seems weird, it is weird. Often our internal radar or early warning system will tell us that a certain request is odd. Listen to that inner voice. It is always better to check and verify. Better to be safe than sorry.
- If you are a victim report the crime. First warning the compromised vendor about the problem, get your own IT staff involved to check if your company has also been compromised. Victims can also file a complaint with the IC3. I have done that myself for a client or two.
Just because ransomware is the hot problem this year, don’t take your eye off the BEC problem. Either exploit could end up costing your company thousands or millions of dollars.
More information:
- The Role of the IC3 in Cybercrime Prosecution
- I Filed a Report with the Internet Crime Complaint Center
- The FBI Releases the IC3 2017 Internet Crime Report
NOV




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com