From Pinterest
JUN
 File this under Not Surprised.
File this under Not Surprised.
One of the problems with sending all our technology manufacturing jobs to foreign countries in order to produce less expensive goods is that some of these countries are not necessarily our best buddies. With some of them we might have what you would call “trust issues.”
Recently The Hacker News released an article about how a Chinese manufacturer of ARM processors (Allwinner sun8i for A83T, H3, or ...
Continue Reading → This is not a gripe about Spell-Check, although I am driven mad when my phone tries to “correct” the spelling of something I spelled correctly. Sometimes I get really funny and/or embarrassing results.
This is not a gripe about Spell-Check, although I am driven mad when my phone tries to “correct” the spelling of something I spelled correctly. Sometimes I get really funny and/or embarrassing results.
Speaking of embarrassing, have you ever mis-typed a domain name and ended up at a porn site? And caught a virus? (The computer equivalent of an STD?) This is the result of something called “typo-squatting.” Individuals will ...
Continue Reading →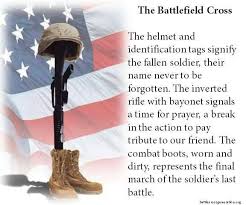 A special thanks today, to those among us who have served in the armed forces.
A special thanks today, to those among us who have served in the armed forces.
Today is a national day of remembrance for those who have fallen in the line of duty while serving our country in the armed forces, and those who lived to tell about it, but have left this world. Take time today to find a veteran or active duty military and thank them for their service.
Continue Reading →The cyber-criminal underground has found a real moneymaker in the various forms of encryption based ransomware schemes. These exploits turn all your readable work product, your documents, pictures, music and video files, into a collection of encrypted gibberish, and then kindly offers to sell you the decryption key. I recently saw an infographic from Symantec on the Bromium blog that illustrated the problem perfectly.
 One of the very worst breaches that can happen to you is for an attacker to be able to access your email account. If someone else can access your email, and read the messages you send and receive, and access your contact list and calendar, then they can learn many personal details about you that would make it easier to steal your identity, access other web accounts using the password reset ...
One of the very worst breaches that can happen to you is for an attacker to be able to access your email account. If someone else can access your email, and read the messages you send and receive, and access your contact list and calendar, then they can learn many personal details about you that would make it easier to steal your identity, access other web accounts using the password reset ...

Its been a while since we have written about AI and robotics, but an article in Tech Republic got me inspired to discuss some of the more disturbing uses of autonomous machines, from least to most scary
Thanks to my uncle Ron Weiss for this one:
They should put Prince on the $20 bill and call it $19.99… It’s “The bill formerly known as a twenty.”
Continue Reading →
 A recent rule by the Supreme Court has given the FBI authority to hack your computer if it is inadvertently part of a criminal botnet. Recent changes to a procedural rule known as Rule 41 allows the FBI to obtain a search warrant to use “network investigative techniques” or NIT (or more commonly called hacking) to search computers engaged in criminal activity anywhere in the world. This includes innocent computer ...
A recent rule by the Supreme Court has given the FBI authority to hack your computer if it is inadvertently part of a criminal botnet. Recent changes to a procedural rule known as Rule 41 allows the FBI to obtain a search warrant to use “network investigative techniques” or NIT (or more commonly called hacking) to search computers engaged in criminal activity anywhere in the world. This includes innocent computer ...
 Windows XP was released on August 24, 2001. It was officially retired by Microsoft two years ago on April 8, 2014. This makes WinXP almost 15 years old, which in operating system years is about 500 years old. Sophos reported:
Windows XP was released on August 24, 2001. It was officially retired by Microsoft two years ago on April 8, 2014. This makes WinXP almost 15 years old, which in operating system years is about 500 years old. Sophos reported:
Continue Reading →“Windows XP was still running on 10.9% of all desktops as of March 2016, according to stats compiled by Net Applications.
To put that in perspective, according to Net Applications’ figures, Windows XP is ...