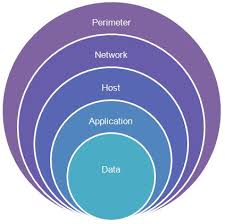
 The problem with cybersecurity it that an attacker only needs to exploit a single vulnerability, while a defender needs to protect everything. Defense has evolved from perimeter defense, to defending all endpoints, to adding automated detection and prevention appliances, to universal threat management that looks at not just north/south traffic passing through the Internet gateway, but also east/west traffic across the LAN between devices. This is called “defense in depth.”
The problem with cybersecurity it that an attacker only needs to exploit a single vulnerability, while a defender needs to protect everything. Defense has evolved from perimeter defense, to defending all endpoints, to adding automated detection and prevention appliances, to universal threat management that looks at not just north/south traffic passing through the Internet gateway, but also east/west traffic across the LAN between devices. This is called “defense in depth.”
Cybersecurity continues to evolve. One of the hopeful trends is the use of artificial intelligence and machine learning to detect attacks and intrusions, and mount a defense more quickly. This may help turn the tables against attackers and reduce or even end the advantage that attackers have held over defenders.
Computers are great at tasks that humans are bad at. For instance if you have ever had to look through a security log for information about a breach, you know this is a task you really want to turn over to a machine that has the speed and processing power to separate the desired information form the thousands of events in the log. A human, on the other hand, is better at the actual analysis of this information. Artificial intelligence and machine learning show promise to make this sort of information crunching even more useful. Cybersecurity areas where AI is being tested include:
- Discovering zero-day vulnerabilities and attacks – AI is being used not just to find and identify the vulnerabilities, but also to patch or defend them.
- Threat intelligence – Extracting tactical and strategic trends from a multitude of information sources, and using the information to formulate new defenses.
- Pivoting – Adapting to an adversary’s tactics and techniques and successfully defending against active exploits and attacks.
- Learning – Using the information gained from individual incidents and creating policies, rules, and defensive tactics to prevent attacks from working a second time.
Artificial intelligence will become an important and increasing part of the software and hardware tools and appliances that businesses will be using to secure their networks and information and prevent attackers from gaining their objectives.
More information:
Share
MAR




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com