 If you own a small business, you have a website. Would you be surprised to learn that your site is a top target of cyber-criminals? Most people believe their business is too small and insignificant to be interesting to attackers, but your website is valuable to them precisely because it is small.
If you own a small business, you have a website. Would you be surprised to learn that your site is a top target of cyber-criminals? Most people believe their business is too small and insignificant to be interesting to attackers, but your website is valuable to them precisely because it is small.
What makes a small business website an attractive target? It is because your website has a good, trustworthy reputation. Your site’s good reputation can be used by cyber-attackers, who are in it for the money, and have several ways that they can monetize an hijacked website. Once Google and other security services flag your site as malicious, the attackers move on and leave you to clean up the mess and try to restore your reputation.
Lots of small business websites are self-designed by the business owner. The site owner/designer rarely has any idea that their website need to be properly secured, and no idea how to do it. Even professional web designers may not have a good understanding of web site security. Often these sites are easy to hijack because they are poorly secured with a single relatively weak password. Usually the same password that protects the website also protects the web hosting account. This gives the cyber-attacker access to any email accounts that have been created on the domain name, too.
Some reasons that your site may be used by cyber-criminals include:
- The website has a clean reputation that can be exploited.
- Your compromised site may be rented to other cyber-criminals.
- Your site may be used to store and distribute malicious software, adult images and videos, stolen identity documents, and similar contraband.
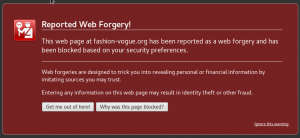
- Your attacker may use your site to host phishing landing pages.
- Your attacker may use your site to host spam landing pages that are used to sell counterfeit, knock-off or illegal products, or cracked software and games.
- Your site could be used to send spam emails. Your good site reputation will get the spam past email spam filters.
- Your site could be used to infect site visitors with malware. This would give the attackers access to the computers of your site’s visitors.
- The site has value to the owner that can be exploited.
- Your site could be held for ransom.
- Your web site could be defaced to host political messages, or for revenge or extortion.
- Your business email accounts may be hijacked and used to impersonate you or company employees. This can lead to wire transfer and invoicing scams.
- There is existing web traffic that can be exploited.
- Your site can be modified to contain redirection code or spammy links that redirects your site visitors to other websites
- Your website may be used to host links to pump up another website’s SEO and page rank.
- The website database may contain personally identifying information (PII) about site visitors and customers.
- User names and passwords can be sold to list brokers on the Dark Web.
- Other PII can be used in identity theft exploits.
- Some of the PII may be confidential or embarrassing, your client may be the victim or extortion.
- The server platform itself can be used to run programs and bots for the attacker.
- Your hijacked web server may be rented to other cyber-criminals.
- Your web server may be turned into a zombie and joined to a botnet to deliver a distributed denial of service (DDoS) attack.
- Your server may have software added to turn it into a spam bot.
- Your server may have the software installed to mine crypto-currency like BitCoin or Monero. It may also be used to distribute mining software to other servers.
Your website needs to be properly protected, and if you are using WordPress for your design tool, there are many great plugins that can help, including my favorite, WordFence Security. Obviously, the best solution is to keep attackers for acquiring your website in the first place. OnFriday, we will cover ways to recover after your website has been hijacked.
More information:
- What Happens When Your Website Is Hijacked
- What Happens When Your Website Gets Hijacked part 2
- Wordfence
APR




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com