 Phone phreaking refers to the exploration of phone systems and networks to discover how they work. It also refers to the exploitation of telephone lines and systems in order to make free long distance calls. Like the term “hacking,” it can refer to both the curious and the criminal.
Phone phreaking refers to the exploration of phone systems and networks to discover how they work. It also refers to the exploitation of telephone lines and systems in order to make free long distance calls. Like the term “hacking,” it can refer to both the curious and the criminal.
Time to climb into Mr Peabody’s WABAC Machine for our history lesson. Phone phreaking got its start in the late 1950’s with the discovery by Joe Engressia that the 2600 hertz tone would reset the telephone line for long distance dialing. Entering your desired phone number would provide a long distance call without charging your phone line. A toy whistle given away in the breakfast cereal 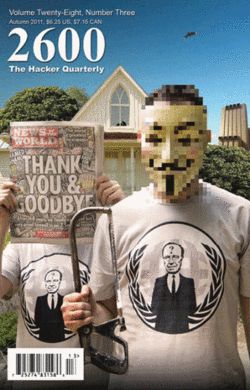 Cap’n Crunch could produce that tone. Prominent phone phreakers included super-hacker Kevin Mitnick, and future Apple computer inventors Steve Jobs and Steve Wozniak. Phreakers communicated their ideas and activities via newsletters and often by conference call. Magazines , such as 2600 the Hacker Quarterly, which was founded in 1984, spread the word.
Cap’n Crunch could produce that tone. Prominent phone phreakers included super-hacker Kevin Mitnick, and future Apple computer inventors Steve Jobs and Steve Wozniak. Phreakers communicated their ideas and activities via newsletters and often by conference call. Magazines , such as 2600 the Hacker Quarterly, which was founded in 1984, spread the word.
Back in the 60’s and 70’s, when long distance phone calls were a special event costing a dollar or more per minute, phreaking was a way for college kids to keep in touch with family and each other without having to pay the toll charges. This of course was a crime called toll fraud.
This became a criminal business enterprise. When domestic rates were high, someone wanting to make a less expensive long distance call could make it through the stolen telephone network access of a local phone phreaker. Even as domestic long distance fees dropped to pennies per minute, a lucrative trade could be made providing low cost international calls in immigrant neighborhoods.
I hadn’t heard much about international toll fraud, or other phreaking enterprises until I read a recent news release from the FBI.
 The FBI recently arrested a Pakistani national Muhammad Sohail Qasmani in Los Angeles. He had amassed nearly $4 million dollars through a type of toll fraud. He and his group of phone hackers would compromise hundreds of business telephone systems (PBXs), and set up unused extensions, and use them to dial into pay-per minute numbers typically used by psychics, adult entertainment, and chat lines. Qasmani bought several of these premium numbers, and would have his phreakers dial into the premium numbers from compromised phone systems. When the victimized company paid the phone bill, including the charges for the premium numbers, Qasmani and his crew would receive their split from the telephone number service company.
The FBI recently arrested a Pakistani national Muhammad Sohail Qasmani in Los Angeles. He had amassed nearly $4 million dollars through a type of toll fraud. He and his group of phone hackers would compromise hundreds of business telephone systems (PBXs), and set up unused extensions, and use them to dial into pay-per minute numbers typically used by psychics, adult entertainment, and chat lines. Qasmani bought several of these premium numbers, and would have his phreakers dial into the premium numbers from compromised phone systems. When the victimized company paid the phone bill, including the charges for the premium numbers, Qasmani and his crew would receive their split from the telephone number service company.
Qasmani was recently sentenced to 48 months in prison. Another Pakistani national, Noor Aziz Uddin is currently a fugitive wanted by the FBI for his activities leading this organization.
The take away for those of you who are tasked with running or managing a business PBX phone system, or those people who audit and pay the phone bill, is to be on the lookout for spurious charges such as these. Fraudulent activity should be reported to your phone company, and the FBI’s Internet Crime Complaint Center.
More information:
- FBI News – Telecom Hacking Scheme – July 6, 2017
- US DOJ – Press Release – June 28. 2017
- Wikipedia – Phreaking
- The Atlantic – What Ever Happened to Phone Phreaks?
- Wikipedia – 2600 The Hacker Quarterly
- 2600 – The Hacker Quarterly web site
AUG




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com