 Why are retailers in the US still stuck in the 20th century when it comes to credit card processing? Why are so many stores still using outdated magnetic stripe card readers, when EMV or “chip” card readers are available? Who is at fault? Is it the store or the credit card processing company?
Why are retailers in the US still stuck in the 20th century when it comes to credit card processing? Why are so many stores still using outdated magnetic stripe card readers, when EMV or “chip” card readers are available? Who is at fault? Is it the store or the credit card processing company?
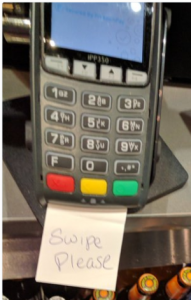
Stores were supposed to have the EMV card readers installed by October 2015, but two and a half years later, we are still seeing card readers like the one in the picture. Chip reading is possible, but not enabled for some reason. Evidently, retailers are waiting to have their new EMV readers to be certified by their card processor. There has been a shortage of personnel qualified to do this task. EMV stands for Europay, Mastercard, Visa. They are the three credit card companies that developed the standard.
What is the difference between the mag stripe, chip-and-sign, and chip-and-PIN processes? Is one better than another?
- Magnetic stripe – The magnetic stripe stores the credit card number and other personal information in a clear-text format that makes it a very poor form of security, basically there is none. Your mag stripe information can be cloned to something like a gift card in a few seconds by the same store employee you handed the card to. The backup security – your signature – is rarely checked by store staff, and even if it was, it is never challenged. Store owners pay for credit card losses if they are using magnetic stripe readers instead of EMV, so there is plenty of incentive for them to move to EMV.
- EMV Chip – The chip on the card creates an encrypted one-time charge code that is used for only one transaction. This information cannot be replayed on a second transaction. This is a variation of the “one-time pad” which is recognized as one of the most secure forms of encryption available, and nearly impossible to break. You can choose between “Credit” or “Debit” at the time of your transaction. Credit will get you chip-and sign. Debit gets you chip-and-PIN.
- EMV chip and signature – Once you have “dipped” or “tapped” your card on the card reader, the second form of security is again the trusty, old, and worthless signature. Certainly better than the mag stripe scenario, but not as secure as it could be.
- EMV chip and PIN – This is my personal favorite, and also favored by the FBI, chip-and-PIN gives us true two-factor authentication – something you have (the card) and something you know (the PIN number). This is what I insist on using whenever it is available to me. You can select “Debit” next time and do this yourself.
I think at this point, some gentle needling of the store owner by the customer is in order. We should begin insisting that the EMV chip readers are enabled and available to use.
More information:
- Mercury News – no more signatures – because a signature is proof of nothing.
MAY




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com