Did you know that the easiest way for me to get your password is just to ask for it? This is one way that cyber-criminals can get one of your passwords. In our last post we focused on password cracking. Today we will look at all the other ways that an clever attacker can compromise your password.
- Social Engineering – Sometimes the easiest way to get password information is just to ask for it. Social engineering is a type of con game with computer or network compromise as the goal. While the majority of social engineering exploits rely on a phishing emails, there are other approach vectors. Social engineering can happen in-person, over the phone, or by text or email. There may be some sort of impersonation attempt, such as a phone call from someone claiming to be from your company’s IT department, or a service tech from your ISP, or a tech from “Microsoft.” Defending against social engineering requires training staff what to look for, and a level of skepticism or suspicion whenever someone starts asking for passwords or other personal information.
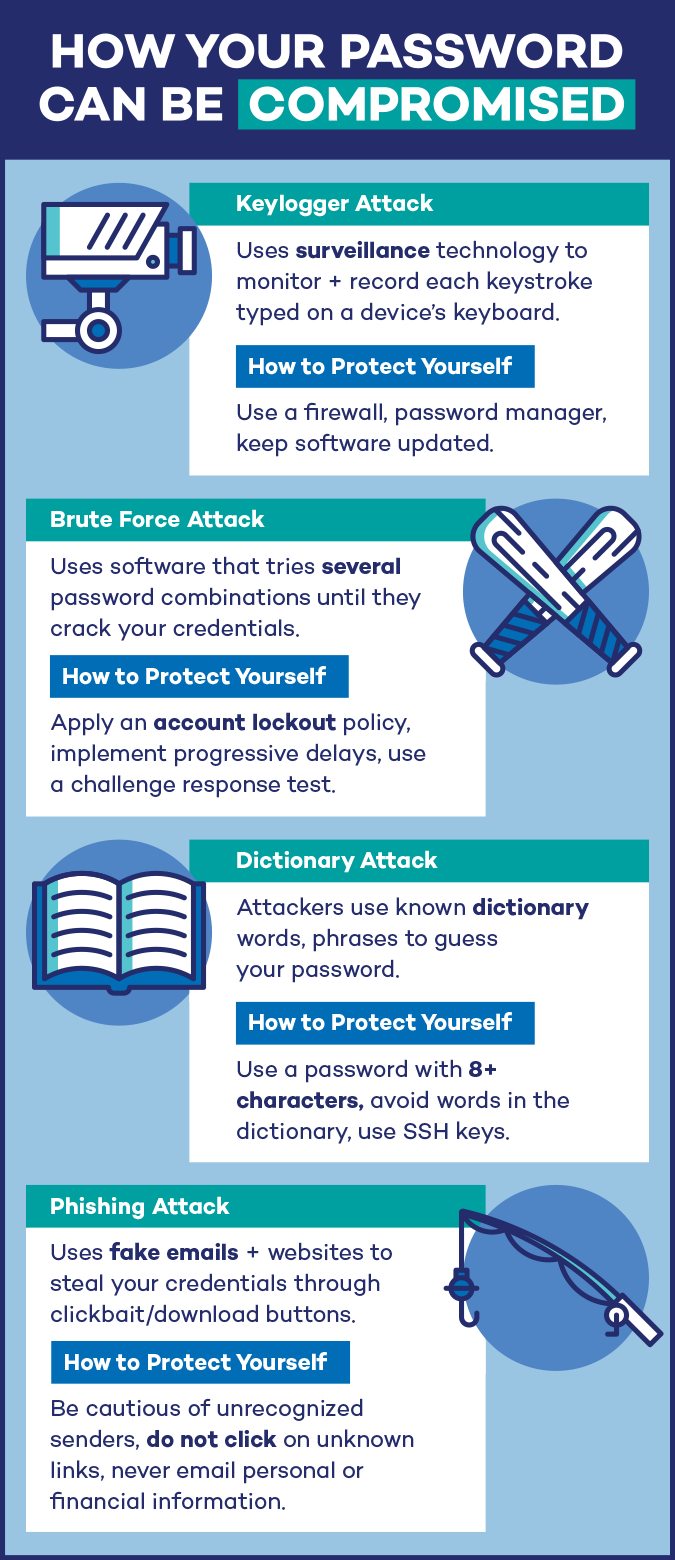
- Phishing – Phishing is a type of social engineering exploit that starts with an email with either a link or an attachment.
- Attachments – Email attachments usually will contain some sort of self executing code or software that runs when you open the attachment. Typically this will be something like a remote access Trojan Horse (RAT), a keylogger, or credential stealing banking malware. The best defense is to resist opening unexpected attachments, and verify the content with the sender before opening. Or check out the attachment in VirusTotal.
- Links – Links in phishing emails usually open a browser window and connect to a specially crafted web page called a “landing page.” Landing pages are often hosted on hijacked legitimate websites. These pages usually have a fake login screen for capturing your user and password information, or may have a longer web form for gathering more information. Often these pages will also surreptitiously download a RAT or keylogger too. To defend against malicious links avoid clicking without checking the link out first using the hover technique or by checking the link at VirusTotal.
- Spearphishing – is a more targeted form of phishing that may be targeting a specific individual or members of a single organization. The emails are generally crafted using research information gathered earlier to create messages that are very believable. These emails may appear to come from co-workers, supervisors, or known vendors or customers. Confirming emails with the sender is your best defense.
- Keylogging – A keylogger is a malware program that gathers your keystrokes, all the information you type during the day, including web addresses you visit, and user IDs and passwords you use to login. This information is sent back to the attacker once a day, and the text file will be searched for useful information. Using a good up-to-date anti-malware product is the best way to keep this sort of software from installing on your computer.
In the next post, we will look at the current recommended standards for creating a secure password, and policy recommendations from the National Institute of Standards and Technology (NIST).
A special thanks to Panda Security for inspiring the content of this series and providing us with the infographics used in this series.
ShareJUN




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com