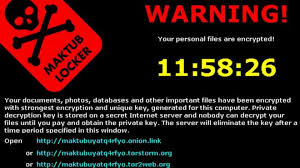
 Encryption ransomware can be a devastating event if it happens to your or your company. The three solutions are basically pay the money, restore from backup, or accept your losses and move on. All are expensive, and some can be severe enough to drive a business out-of-business.Monday we gave you several ways to prevent, or at least prepare a response to a crypto-ransomware exploit. Today we are going to look at early detection and defensive tactics.
Encryption ransomware can be a devastating event if it happens to your or your company. The three solutions are basically pay the money, restore from backup, or accept your losses and move on. All are expensive, and some can be severe enough to drive a business out-of-business.Monday we gave you several ways to prevent, or at least prepare a response to a crypto-ransomware exploit. Today we are going to look at early detection and defensive tactics.
According to a recent paper from Palo Alto Networks, the three main methods of deployment are email attachments, email links, and exploit kits. Regarding email, we have discussed at length in previous articles the importance of employee cybersecurity awareness training in defending the Inbox from email-borne exploits. Additional methods to reduce or eliminate email exploits would be:
- Better email filtering – get a spam firewall if you don’t have one or set one up through a cloud provider.
- IDS, IDS, or Unified Security Management (USM) solutions – AlienVault is a solution we are currently recommending for businesses that are getting serious about exploit detection and prevention. This sort of a solution will see the encryption activity early in the process and alert the IT or security staff to the issue.
- Block ZIP files – since some many exploits use the ZIP format for attaching files, blocking them at the email gateway would eliminate this problem. For those who are dependent on email for file sharing, there are many online resources (DropBox, OneDrive, Google Drive) for sharing these files in a way that is more secure and easy to verify.
- Block VB Macros – Exploits are showing up again in Word, Excel and other office attachments. Macros are blocked by default, but using Group Policy to prevent an end-user from enabling them at all would block this attack.
Exploit kits are different. Exploit kits are sophisticated tool-kits that exploit operating system and software vulnerabilities. These tool-kits can be specifically recreated for the job and intended target using something such as Metasploit, or they can be purchased as a turnkey service on the Dark Web. Usually exploit kits are executed when a victim visits a compromised but legitimate website, or through typographical errors, sometimes a malicious replica site with a close misspelling. Malicious software hidden on the site, often in an advertisement or malvertisement redirects you to the exploit kit landing page unnoticed. If your system is vulnerable, a download of a malicious program will be installed and the encryption of important files begins. Here are some good ways to defend again these:
- Application control systems will prevent any software from installing unless it has been previously approved for use in the corporation. In addition to blocking ransomware, this defeats almost all other malware installations, as well as games and non-business applications that sometimes users install without permission.
- Patches and updates – when you patch, you usually fix a security hole that will block one or more exploits kits from working on your system. Patch on a tight schedule. Waiting 90 days to update so you can “test” means the bad guys have 90 days to break in. (Are you really testing or just delaying?)
Friday we will look at recovery options for crypto-ransomware infections. We have stated that once you are encrypted there is no way back, but this is technically not always true. Find out more in our next post.
Share
AUG




About the Author:
I am a cybersecurity and IT instructor, cybersecurity analyst, pen-tester, trainer, and speaker. I am an owner of the WyzCo Group Inc. In addition to consulting on security products and services, I also conduct security audits, compliance audits, vulnerability assessments and penetration tests. I also teach Cybersecurity Awareness Training classes. I work as an information technology and cybersecurity instructor for several training and certification organizations. I have worked in corporate, military, government, and workforce development training environments I am a frequent speaker at professional conferences such as the Minnesota Bloggers Conference, Secure360 Security Conference in 2016, 2017, 2018, 2019, the (ISC)2 World Congress 2016, and the ISSA International Conference 2017, and many local community organizations, including Chambers of Commerce, SCORE, and several school districts. I have been blogging on cybersecurity since 2006 at http://wyzguyscybersecurity.com