 A quick Saturday digest of cybersecurity news articles from other sources.
A quick Saturday digest of cybersecurity news articles from other sources.
Microsoft lets Windows users off the update leash
Microsoft has announced some big changes that will finally give Windows users more control over updates and releases.
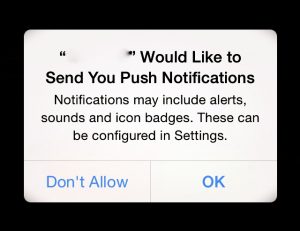 Firefox draws battle lines against push notification spam
Firefox draws battle lines against push notification spam
Mozilla ...
Continue Reading →MAY







