A quick Saturday digest of cybersecurity news articles from other sources.
A quick Saturday digest of cybersecurity news articles from other sources.
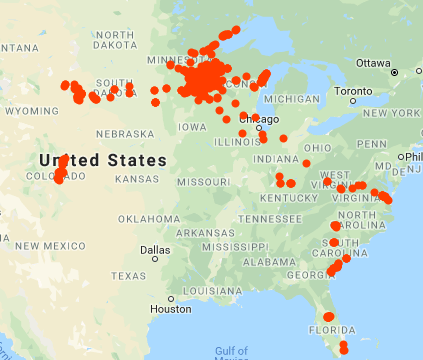
AA20-006A: Potential for Iranian Cyber Response to U.S. Military Strike in Baghdad
Original release date: January 6, 2020
Summary
The Cybersecurity and Infrastructure Security Agency (CISA) is sharing the following information with the cybersecurity community as a primer for assisting in the protection of our Nation’s critical infrastructure in light of the current tensions between the Islamic Republic of ...
Continue Reading →JAN