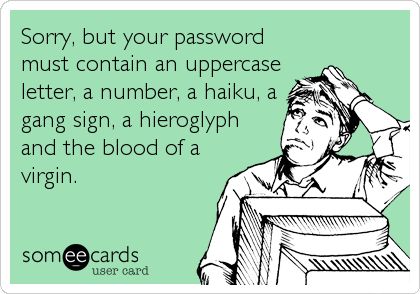
 Most corporate password policies are a waste off time and do not add anything extra to providing secure authentication. Many of these policies were put in place to meet the standards of various compliance bodies (PCI-DSS, HIPAA, etc.) But basically these policies are not keeping up with the state of the art in password cracking, as we discussed last November in our post on
Continue Reading →
Most corporate password policies are a waste off time and do not add anything extra to providing secure authentication. Many of these policies were put in place to meet the standards of various compliance bodies (PCI-DSS, HIPAA, etc.) But basically these policies are not keeping up with the state of the art in password cracking, as we discussed last November in our post on
Continue Reading →
DEC

 As we approach year-end, many small and medium sized business owners and managers are coming to the realization that their best intentions for creating a cybersecurity program in their organization have fallen short. This was the year, you promised yourself, that we get a handle on computer and network security.
As we approach year-end, many small and medium sized business owners and managers are coming to the realization that their best intentions for creating a cybersecurity program in their organization have fallen short. This was the year, you promised yourself, that we get a handle on computer and network security. The Mirai and Bashlight botnets have caused quite a stir in the cybersecurity and IT realms. The easy ability to round up and deploy millions of devices in a botnet using automated tools has raised the bar. How we respond to DDoS attacks will have to change.
The Mirai and Bashlight botnets have caused quite a stir in the cybersecurity and IT realms. The easy ability to round up and deploy millions of devices in a botnet using automated tools has raised the bar. How we respond to DDoS attacks will have to change. I was tempted to post this article late in October, when Brian Krebs suffered with the DDoS attack on his website, or when the Mirai botnet attack on DynDNS was in full swing, but decided to wait it out until after the election, in case it turns out that the Dyn attack was a precursor to an attack to disrupt the elections. And as of today, it appears that it was ...
I was tempted to post this article late in October, when Brian Krebs suffered with the DDoS attack on his website, or when the Mirai botnet attack on DynDNS was in full swing, but decided to wait it out until after the election, in case it turns out that the Dyn attack was a precursor to an attack to disrupt the elections. And as of today, it appears that it was ... NIST has created a self assessment tool for companies and organization who are working through the
NIST has created a self assessment tool for companies and organization who are working through the  Back on August 31 I received an email from the Department of Homeland Security about a set of
Back on August 31 I received an email from the Department of Homeland Security about a set of  October is National Cyber Security Awareness Month. This was released by US-CERT, and I thought it was worth posting.
October is National Cyber Security Awareness Month. This was released by US-CERT, and I thought it was worth posting. You don’t need to be a journalist, freedom fighter, or living under an oppressive political regime to have the desire for some online privacy. Maybe you are trying to put the contents of your life back into the Pandora’s box you opened when you signed up on Facebook. Maybe you would like a little privacy in your online life.
You don’t need to be a journalist, freedom fighter, or living under an oppressive political regime to have the desire for some online privacy. Maybe you are trying to put the contents of your life back into the Pandora’s box you opened when you signed up on Facebook. Maybe you would like a little privacy in your online life. As we add more mobile and portable devices to our digital collection, cybersecurity for mobile devices becomes more important. Smartphones, tablets, wearable tech, and ultra-portable laptops are certainly convenient and easy to carry, but that makes them easy for a thief to carry off. When these devices are stolen, you lose much more than the hardware. Every bit of information on the device is up for grabs too, from contact lists, personal information, ...
As we add more mobile and portable devices to our digital collection, cybersecurity for mobile devices becomes more important. Smartphones, tablets, wearable tech, and ultra-portable laptops are certainly convenient and easy to carry, but that makes them easy for a thief to carry off. When these devices are stolen, you lose much more than the hardware. Every bit of information on the device is up for grabs too, from contact lists, personal information, ...